tag:blogger.com,1999:blog-16546719935396346662024-10-04T19:00:11.531-07:00闲言碎语一个人的闲言碎语drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.comBlogger62125tag:blogger.com,1999:blog-1654671993539634666.post-72800937505472218162021-12-09T04:45:00.008-08:002021-12-09T04:53:53.922-08:00codeql for mac <pre class='markdown'/>
# Codeql for mac
关键问题:
1. 安装codeql-cli
官方答案是 [codeql-cli-binaries/releases](https://github.com/github/codeql-cli-binaries/releases) 上下载。
我比较懒,所以直接 ```brew install codeql``` . 感谢官方的努力,使得懒人安装成为可能。
2. 报错 *ERROR: Referenced pack 'codeql-cpp' not found.*
这是让我头疼了两天的问题,基本 google 不到相关解决方案(完全是因为大家都比较老实,按照官方方案安装)。
原因是 ql 的依赖库 [ql](https://github.com/Semmle/ql) 找不到,这个在官方的安装方案中,是需要与 codeql 放在同一目录的。
所以,brew install 后,如果要达到同样的效果,需要在
```
/opt/homebrew/Caskroom/codeql/2.7.2/
``` 目录,
```
git clone https://github.com/Semmle/ql
```
3. 依然会报错 *Error: Connection is disposed.*
原因不知道,在 VSCode 的 setting.json 中,设置路径可解除报错,感觉是 codeql 自己无法自动识别库路径——即使你给它放在了同一目录下。
```
"codeQL.cli.executablePath": "/opt/homebrew/Caskroom/codeql/2.7.2/codeql/codeql"
```drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-62614972370787901022021-09-23T06:09:00.001-07:002021-09-23T06:11:07.372-07:00Mac With Apple M1 安装 airtest 失败解决方案<pre class='markdown'/>
# Mac With Apple M1 安装 airtest 失败解决方案
项目需要,需要利用 airtest 进行一些Android 模拟器的脚本测试,所以需要 pip install airtest. (关键的其实是 pocoui ,最终追踪下来,安装这个模块时出错的。)
然后就理所当然的出错了:
```
pip install airtest
.......
Error: Failed building wheel for numpy
```
网上找了各种问题原因,归结如下:
1. python 版本过高导致,最好使用稳定的3.8
2. python 版本过高导致,最好使用稳定的3.6
3. wheel 有问题,重装 wheel
按照1 的方案,安装了 python 3.8。 在 mac 下切换版本(homebrew 安装的环境下):
```
arch -arm64 brew install python@3.8
brew unlink python@3.9 && brew link --overwrite python@3.8
```
此时,pip3 就是 ``` python3.8 -m pip ``` 了。
但,安装依然报同样的错。
然后参考方案2,准备安装 python3.6 / python 3.7 。 结果,系统不支持。
```
arch -arm64 pip3 install python@3.7
python@3.7: The x86_64 architecture is required for this software.
Error: python@3.7: An unsatisfied requirement failed this build.
```
game over . (由此可以看出,明显是版本问题导致无法正常 pip 安装模块,跟 wheel 也就没啥关系了)
## 峰回路转的'绿色版'解决方案
这下没办法了,所以思考了一下,装个 airtestIDE 先手工一下,然后脚本处理好了,再同步到服务器进行调试。
安装 airtestIDE 过程省略。
发现 airtestIDE 使用一切正常,那是不是他的依赖都是 OK 的、预编译好了的?python 能不能直接用他的模块呢?
于是,打开包内容 -> Contents -> MacOS ,发现真有关键的 poco 模块,于是,将其中关键的 poco 、 airtest、airtest_selenium 模块都直接复制到 python 的 site-packages 中。
再运行,补充一些需要的模块,大功告成!
```
get free device number: 3
deviceList: ['emulator-5554-0', 'emulator-5554-1', 'emulator-5554-2']
[pkg:]:getEmu cnt: 1 left_time:120
[pkg:]:error adb:0 out :List of devices attached
... ...
... ...
... ...
```
drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-90072029744208107202021-07-08T05:48:00.006-07:002021-09-23T01:17:31.429-07:00MAC [伪]使用手册<pre class='markdown'/>
## finder显示完整路径
使用终端命令行:
```
defaults write com.apple.finder _FXShowPosixPathInTitle -bool TRUE;killall Finder
```
## 右键 Open With VSCode
```
1. 点击Dock => 其他 => 自动操作
2. 点击新建文稿
3. 点服务,点击选取
6、在左侧面板选择“实用工具”;然后找到”运行Shell脚本“,把它拽到右侧面板里;
在右侧“服务”收到选定选择文件夹,位置Finder(访达);“运行Shell脚本”的面板里,选择Shell”/bin/bash“,传递输入“作为自变量”,然后修改Shell脚本
复制以下内容:
for f in "$@"
do
open -a "Visual Studio Code" "$f"
done
7、之后,保存cmd+s,保存为Open With VSCode
8、选择电脑上任意一个文件夹,点击右键“服务”/"快速操作",就可以看到“Open With VSCode”菜单
```
## 偶现终端中文显示乱码
1. 运行```locale```命令查看本地编码方式
2. ```vi .zshrc```修改默认编码格式,添加如下内容
```
export LC_ALL="zh_CN.UTF-8"
export LANG="zh_CN.UTF-8"
```
3. ```source .zshrc```生效修改
## 错误: Cannot install under Rosetta 2 in ARM default prefix (/opt/homebrew)!
安裝 python3.8
一般正常都是执行 brew 安装即可,但最近在 M1 上却初现了如下错误:
```
brew install python@3.8
Error: Cannot install under Rosetta 2 in ARM default prefix (/opt/homebrew)!
To rerun under ARM use:
arch -arm64 brew install ...
To install under x86_64, install Homebrew into /usr/local.
```
直接按照提示执行如下命令即可:
```
arch -arm64 brew install python@3.8
```
然后有需求切换默认的 python 版本则:
```
brew link --overwrite python@3.8
```
drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-26581035338353359182021-06-10T19:38:00.005-07:002021-06-10T20:07:44.453-07:00Apple M1电脑装 Android 模拟器(AVD)<pre class='markdown'/>
# Apple M1电脑装 Android 模拟器(AVD)
> 新版 mbp or mba 使用 M1芯片,暂时还不支持虚拟化,所以很多模拟器都不可用了,虽然 google 释出了android-emulator-m1-preview,但还存在很多 bug,麻烦。网上看到一个通过 Android Studio下载 arm64版本的 AVD 的可行方案,记录一下。
## 具体步骤
1. 更新你的 Android Studio 到最新版本。
2. Android Studio 右上角打开 Android Virtual Device Manager - 点选 Create Vitrual Device。
**重点在选择System Image的时候,选 Other Images 的标签。ABI 显示支持的芯片是 arm64-v8a。**

3. 下载完成,启动时会遇到:The emulator process for AVD was killed。
4. 打开Terminal,执行: ~/Library/Android/sdk/emulator/darwin-aarch64-replace.sh
```
% Total % Received % Xferd Average Speed Time Time Time Current
Dload Upload Total Spent Left Speed
100 651 100 651 0 0 649 0 0:00:01 0:00:01 --:--:-- 649
100 91.8M 100 91.8M 0 0 7862k 0 0:00:11 0:00:11 --:--:-- 10.9M
unzip emulator-darwin-aarch64-0.2.zip
Archive: emulator-darwin-aarch64-0.2.zip
creating: emulator-darwin-aarch64-0.2/
inflating: emulator-darwin-aarch64-0.2/NOTICE.csv
...
inflating: emulator-darwin-aarch64-0.2/lib/ui_controller_service.proto
inflating: emulator-darwin-aarch64-0.2/emulator
rm: ./lib64/qt/libexec/qtwebengine_resources.pak: No such file or directory
```
5. 此时,需要手动补充文件,Terminal 执行下方命令打开目录: open ~/Library/Android/sdk/emulator/
6. 将 emulator-darwin-aarch64-0.2 目录中的所有文件移动到上一级,覆盖。
7. 打开AVD面板,启动模拟器,即可正常使用。
## 参考
1. [3分钟搞定Apple M1电脑使用Android模拟器](https://zhuanlan.zhihu.com/p/372158270)drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-62544112607040781252021-05-14T00:04:00.001-07:002021-05-14T00:04:30.864-07:00蜜罐与蜜罐识别<pre class='markdown'/>
# 蜜罐与蜜罐识别
## 蜜罐概述
>Honeypots are any security resource whose value lies in being probed, attacked, or compromised.
蜜罐是⼀种安全威胁的主动防御技术,它通过模拟⼀个或多个易受攻击的主机或服务来吸引攻击 者,捕获攻击流量与样本,发现⽹络威胁、提取威胁特征,蜜罐的价值在于被探测、攻陷。其在 本质上来说,是⼀个与攻击者进⾏攻防博弈的过程。蜜罐提供服务,攻击者提供访问,通过蜜罐 对攻击者的吸引,攻击者对蜜罐进⾏攻击,在攻击的过程中,有经验的攻击者也可能识别出⽬标 是⼀个蜜罐。
蜜罐的基本功能:
1. ⽹络欺骗。 使⼊侵者相信存在有价值的、可利⽤的安全弱点,蜜罐的价值就是在其被探测、
攻击或者攻陷的时候得以体现,⽹络欺骗技术是蜜罐技术体系中最为关键的核⼼技术,常⻅的有模拟服务端⼝、模拟系统漏洞和应⽤服务、流量仿真等。
2. 数据捕获。 ⼀般分为三层实现,最外层由防⽕墙来对出⼊蜜罐系统的⽹络连接进⾏⽇志记
录;中间层由⼊侵检测系统来完成,抓取蜜罐系统内所有的⽹络包;最⾥层的由蜜罐主机来完成,捕获蜜罐主机的所有系统⽇志、⽤户击键序列和屏幕显示。
3. 数据分析。 要从⼤量的⽹络数据中提取出攻击⾏为的特征和模型是相当困难的,数据分析是
蜜罐技术中的难点,主要包括⽹络协议分析、⽹络⾏为分析、攻击特征分析和⼊侵报警等。数据分析对捕获的各种攻击数据进⾏融合与挖掘,分析⿊客的⼯具、策略及动机,提取未知攻击的特征,或为管理者提供实时信息。
4. 数据控制。 数据控制是蜜罐的核⼼功能之⼀,⽤于保障蜜罐⾃身的安全。蜜罐作为⽹络攻击
者的攻击⽬标,若被攻破将得不到任何有价值的信息,还可能被⼊侵者利⽤作为攻击其他系统的跳
板。虽然允许所有对蜜罐的访问,但却要对从蜜罐外出的⽹络连接进⾏控制,使其不会成为⼊侵者的跳板危害其他系统。
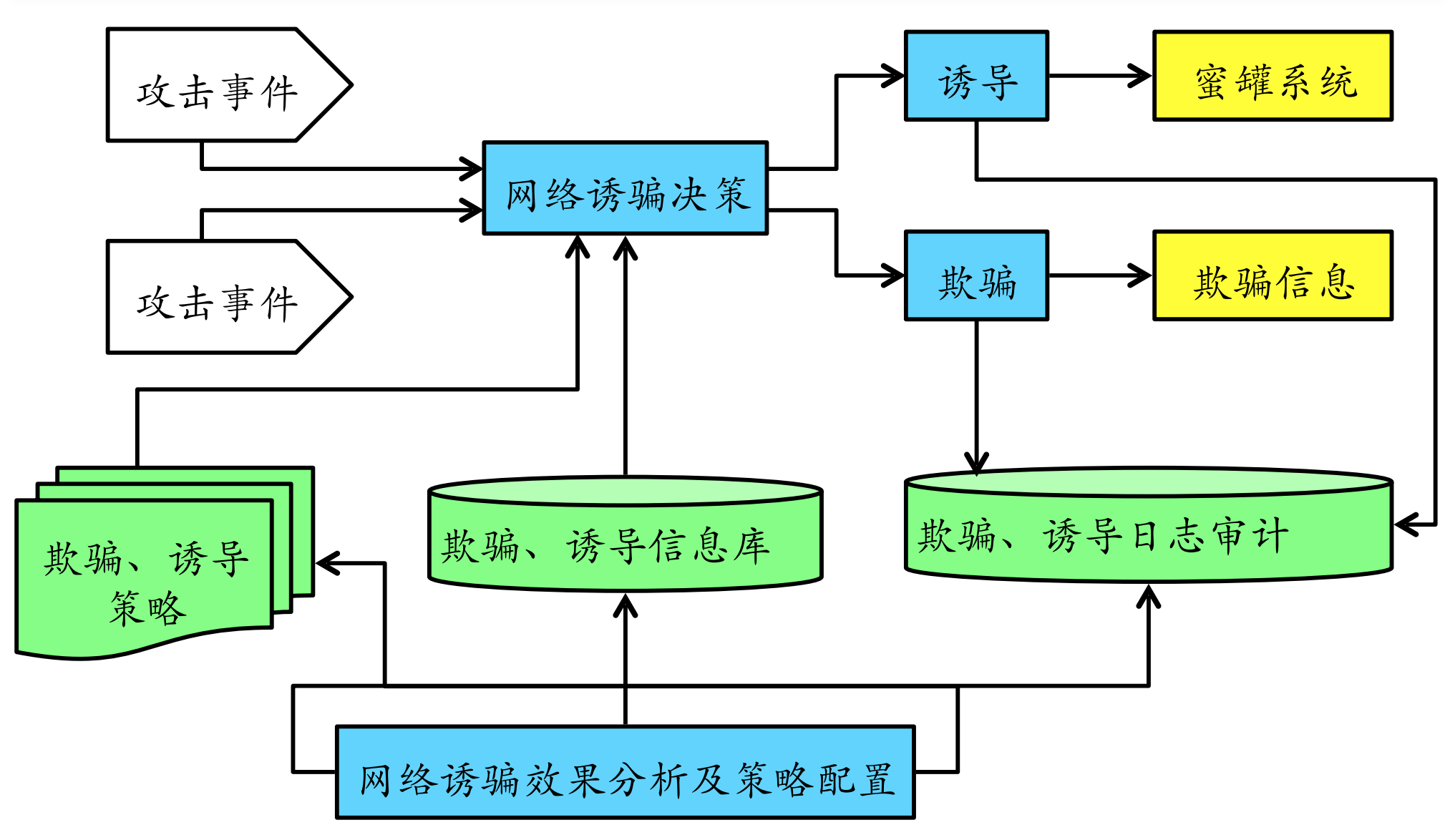
## 蜜罐关键技术
### ⽹络欺骗技术
其设计⽬标是为了让⽹络攻击者产⽣攻击或⼊侵蜜罐的兴趣。典型技术如:蜜罐主机、陷阱⽹络、诱导和欺骗信息设计。
- 蜜罐主机
主要分为:空系统,⽆业务模拟的真实完整操作系统及应⽤程序。镜像系统,对⽣产业务进⾏镜像模拟。虚拟系统,基于虚拟机软件不包含真实业务和业务数据的镜像系统。
- 陷阱⽹络
由多个蜜罐主机、路由器、防⽕墙、IDS、审计系统等组成的供攻击者⼊侵的⽹络。⽬前的陷阱⽹络已经进化到主要通过虚拟化和云计算来实现,不再需要⼤量真实物理主机和⽹络设备。
- 诱导
主要指的是基于地址转换技术和基于代理技术将蜜罐主机隐藏在⼀个受控隔离内⽹,引诱攻击者主动攻击,从⽽可以在⽹关或代理服务器上进⾏便利的数据捕获。
- 欺骗信息设计
例如:端⼝扫描欺骗设计、主机操作系统信息欺骗设计、后⻔欺骗信息设计、Web 扫描欺骗信息设计和⼝令欺骗信息设计。
### 数据控制
之所以需要数据控制,是因为在蜜罐捕获到(恶意)访问⾏为时要么是⾃动响应要么是需要⼈⼯⼲预。⽆论是哪种⽅式,都可能存在联动操作的延时,这就给了攻击者时间和机会彻底攻陷蜜罐系统,从⽽以被攻陷的蜜罐为跳板攻击真实主机和⽹络。
因此在设计蜜罐的数据控制机制时,通常⾄少需要设计两层数据控制。第⼀,这是符合纵深防御原则的,充分考虑了单⼀数据控制失败的情况,增加⾃动发现并阻⽌提权和破坏性强攻击(⼊侵)⾏为的机会。第⼆,可以设置多重伪装,尽可能避免被攻击者察觉他在攻击的是⼀个蜜罐系统。
### 数据捕获
蜜罐相⽐较于⼊侵检测既有继承,同时⼜有⼀些特别的数据捕获来源。
- 系统层⾯,蜜罐可以实现键盘捕获、屏幕记录和进程访问历史记录。
- ⽹络层⾯,蜜罐⽀持攻击图(路径)的重建。
- 数据层⾯,蜜罐⽀持基于蜜信的传播路径重构。
为了保证捕获数据的安全性,通常不能在蜜罐系统本地存储捕获的数据,必需采⽤远程存储⽅式。
### 数据分析
⼊侵检测数据分析算法都可以⽤于蜜罐中的数据分析,例如基于异常的算法:基于特征选择异常检测、基于⻉叶斯推理异常检测、基于模式预测异常检测和基于神经⽹络异常检测。但是在实践中,蜜罐和⼊侵检测对于数据分析的应⽤还是存在⼀些差异的,如下表格所示:
||蜜罐|入侵检测
-- |--|--
目的|还原入侵|发现入侵
手段|异常检测|误用检测、异常检测
⼊侵检测对于数据分析的应⽤主要专注于对于⼊侵⾏为的发现,识别⼊侵类型及⼊侵来源;⽽蜜罐则通过对⼊侵⾏为的精确还原,在发现⼊侵⾏为的基础上进⼀步分析出攻击意图、攻击者身份,并进⾏⻛险影响的评估。
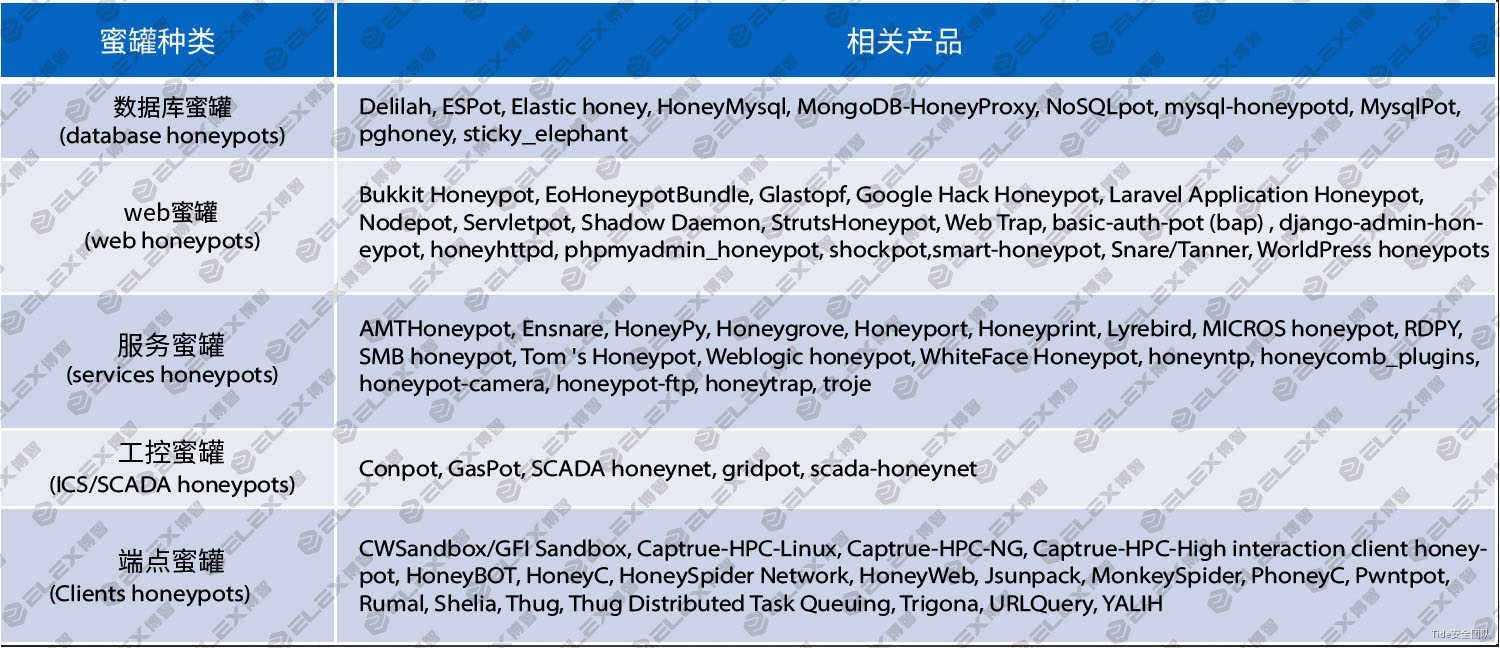
## 常见蜜罐产品
蜜罐可以分为数据库蜜罐、web蜜罐、服务蜜罐、工控蜜罐及端点蜜罐,各种蜜罐对应的相关产品如下图所示:
## 开源蜜罐识别
互联网中的低交互蜜罐大部分为开源蜜罐。由于其特有的开放特性,人们能够对其特征进行识别和规避。
### 协议的返回特征
部分开源蜜罐在模拟协议时,在响应中可能未能实现完全的随机,导致遗留了明显的特征可供反蜜罐人员用于识别(e.g. version/libevent/rusage_user )

### 协议实现的缺陷
在部分开源的蜜罐中模拟实现部分协议并不完善,可以通过发送一些特定的请求包获得的响应来判断是否为蜜罐。
- ssh协议: 协商版本号阶段,由于开源蜜罐只支持固定版本,当遇到不支持版本时会报错。
- Mysql协议: 抓取读取的文件名
- telnet协议: 在命令为空或者直接回车换行时,会响应default模板,该模板内容为test。
### 明显的WEB的特征
部分开源蜜罐提供了web服务,这些web服务中常常会带有一些明显的特征,可以根据这些特征来检测蜜罐。如特定的js文件、build_hash或者版本号等。
- HFish: 在默认8080端口实现了一个WordPress登录页面,页面中由一个名为x.js的javascript文件用来记录尝试爆破的登录名密码。直接通过判断wordpress登录页是否存在x.js文件就可判断是否为蜜罐。
- glastopf: 可以通过页面最下方的blog comments的输入框进行识别。

### 上下文特征
部分开源蜜罐存在命令执行上下文明显的特征,
- Cowrie: a. 设备名称为localhost; b. 设备中所有进程启动于6月22日或6月23日; c. 存在用户名richard。
- 最新版的Cowrie: 在默认配置下一些一些命令得到的结果是固定不变的。如:cat /proc/meminfo 这个命令无论执行多少次得到的内容都是不变的,而这真实的系统中是不可能的。
- HFish: 和telnet协议一样SSH协议在直接进行回车换行时会默认执行default输出test
### Fuzz testing 特征
部分蜜罐借用Fuzz testing的思想实现了蜜罐系统,因此会有如下特征:
- 响应任意端口的TCP SYN Packet。
- 根据协议特征,永远返回正确的响应。
- 返回预定义或者随机的Payload特征库集合。
该类蜜罐可以通过跨服务的特征进行判断,如开放了HTTP服务同时响应了upnp协议,或者根据server的长度或者个数来判断。
## 工控蜜罐识别
### IP地址识别
一般工控设备如plc、dcs、rtu等很少直接暴露到互联网,在业务需要情况下可能会将工控设备直接暴露在互联网,比如设备远程维护等。
通过查询IP地址对应的ISP,来判断所述IP是否属于云服务器提供商的IP地址。当所述IP属于云服务器,并且开放了PLC的工控协议服务如modbus、s7、ethernetip等,则可判定IP为工控蜜罐。
### 操作系统及MAC厂商指纹识别
一般工控设备均为嵌入式设备,如plc、dcs、rtu大多使用实时操作系统如vxworks、QNX,HMI设备一般使用wincc操作系统等;通过TCP/IP操作系统指纹识别,获取目标IP的TCP/IP协议栈指纹,当目标IP的操作系统被识别为Linux的非嵌入式操作系统。并且该设备未经过路由转发与映射,通常可认为是蜜罐系统。
一般工控蜜罐,如服务蜜罐大多部署在linux vmware及docker容器里面,而仿真服务部署在windows系统上面。
### 指纹特征识别
- Openplc modbus蜜罐服务指纹特征识别
安装部署Openplc,并且阅读源码如下,分析蜜罐特征,可以看出openplc只实现了1-16功能码,而重要的设备信息功能码如报告从设备信息17功能码、获取设备信息43功能、施耐德获取cpu、工程等信息90私有功能码均未实现。
可以构造17、43、90功能码去请求openplc,获取设备信息,均会返回非法功能码指纹
- openplc http协议指纹识别
openplc默认开放了http 8080端口,浏览器访问http://ip:8080 查看plc管理页面与真实工控plc设备不一样,并提取http指纹特征。
- Conpot S7 协议 蜜罐服务指纹特征识别
阅读conpot s7comm源码,找到S7服务蜜罐通用特征:"Original Siemens Equipment","88111222","IM151-8 PN/DP CPU"
特征2:最后6个字节始终为 “\x00\x00\x00\x00\x00\x00”
- Conpot ENIP蜜罐服务指纹特征识别
阅读conpot enip蜜罐服务代码,发现向设备发送63功能码获取设备信息,返回的数据device_status== \x60\x31 和device_state == \xff
- 其它工控蜜罐
其它蜜罐及仿真服务程序包括,conpot、openplc、CryPLH2、仿真程序包括modbus tester、Mod Rssim、snap7、opendnp3、qtester104、DNP3_testhaness、EtherNetIP Virtual等。
## 蜜罐反识别方法
通过对蜜罐部署方式及特征分析,如果我们部署蜜罐服务时候,可以考虑采用以下方法进行规避。
1. 如果蜜罐服务要部署在外网,尽量避免使用云服务厂商提供的服务。
2. 如果蜜罐服务部署在企业内网,尽量在蜜罐服务或者仿真程序前面部署一个vxworks系统的设备,并在上面开启端口转发服务,或者利用Qmenu模拟运行vxworks操作系统,使攻击者误以为扫描到的工控设备使用的是vxworks实时操作系统。
3. 定期修改蜜罐内部特征,如conpot蜜罐模板信息,conpot源码中返回报文的协议特征。同一个ip蜜罐节点,尽量只开放如真实plc设备的端口和服务,如502、80、161等端口,避免开放过多及无效的应用端口,被攻击者快速识别蜜罐。
4. 修改宿主机mac地址,尽可能修改成西门子、GE等工控设备的MAC地址,增加攻击者识别蜜罐的难度。
5. 服务蜜罐尽可能实现协议规约必须的功能码,如施耐德plc的17、42、90信息获取功能码任何一个。
6. 尽可能实现高交付服务蜜罐,也可以采用虚实结合部署方式进行部署,增加蜜罐识别难度。
## 参考
1. [Tide安全团队/工控安全Wiki/蜜罐技术](https://www.yuque.com/tidesec/ics/a4f46ba681b34d017fbed21398cb2517)
2. [浅析开源蜜罐识别与全网测绘](https://www.secrss.com/articles/28577)
3. [一种工控蜜罐识别与反识别技术研究与应用实践](https://www.freebuf.com/articles/ics-articles/230402.html)drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-831687086025913582021-05-10T04:43:00.002-07:002021-05-10T04:43:23.257-07:00【转】光明日报:饭圈文化的哲学省思<pre class='markdown'/>
## 1. 不被允许的“姨妈”
3月31日,新浪微博的文学博主“亚非文学 bot”发布退博声明。2 月底某男星粉丝举报AO3平台事件引发的舆论海啸裹挟了众多非传统饭圈的网络群体,被网络舆论戏称为“227 大团结”,余波未止,而此次退出微博的亚非文学 bot 与后续为声援也退博的中东欧诗歌bot则再一次将该粉丝群体推向风口浪尖。亚非文学 bot 为十几位小语种文学的学生运营,整理并翻译了大量文学作品和相关研究,尽管此前确实曾动过退博的念头,但导火索依然是粉丝的攻击。
退博数日前,bot曾转发了含该男星“泥塑黑称”的账号投稿一一“赞姨娇俏bot'ーー并在其粉丝质问后“违规”地回敬了一句人格化的嘲讽,“天呐,我以上帝的名义发誓,失去了您的关注实在是太让我心痛了,”点燃了粉丝们的怒火,对bot进行辱骂与人肉威胁。
“泥塑”是饭圈文化中的一种特殊现象,广义上的“泥塑”指放大女艺人的男性气质或反之,而狭义的也是更为粉丝群体所默认的“泥塑”指女化。因为跨性别的处理,泥塑的支持者往往热衷于鼓吹泥塑体现了先进的女权主义思想,以及更高级的足以欣赏“矛盾美学”的审美品味,通过泥塑,这些粉丝们建构起了“先锋者”的自我形象,泥塑此时成为一种暗含优越性的文化资本,泥塑得越彻底、越夸张意味着越具有智识上的优越。尽管泥塑粉倡导性别价值多元、美学表达多元,但对泥塑对象的普遍口味和要求还是“年轻的美女”,因为“漂亮”才有资格当“女的”,不是任何人都配被泥塑。当不同饭圈的泥塑粉发生矛盾时,对对方的攻击离不开对其偶像的侮辱,对偶像的攻击时常从外貌开始,即剥夺他成为“美女”的权利。
“赞姨”不仅是对自己以俊朗外貌闻名的偶像进行泥塑,而且是“调侃”甚至“侮辱”意味的泥塑,为其粉丝所不能容忍。
上世纪六七十年代,福柯在《疯癫与文明》《规训与惩罚》等著作中提出“凝视理论”,将“凝视”解读为一种权力关系,其中凝视者为主体,被凝视者则是被压抑的客体。1975 年女性主义电影评论家 Laura Mulvey 由此发展,提出男性凝视(male gaze)的概念,女性作为被观看的对象受制于男性的审美和背后强大的男权势力。泥塑文本中常见的“女儿”“姐姐”甚至是“小妈”都是梦幻的、浪漫主义的,这些女性与现实的牵绊无关而仅仅是幻想的造物,相比之下,“姨化”所指涉的“姨母”“大妈”这样容貌衰老且让人联想到琐碎的日常生活的女性,显然为泥塑所不容,“姨”的出现无情击破了粉丝的梦境
与少女审美相伴相生的是女性普遍对外貌与年龄的焦虑,这种焦虑也渗透进了自诩先进的泥塑之中。从这一角度来说,泥塑和造梦自慰的玛丽苏极为密切。我们很难看到有粉丝会去泥塑一个年长的男演员,也几乎不会在泥塑文本中看到“奶奶”“外婆”这样的主角,在“美女”的世界里,这些年长的不再能取悦男性性欲的女性是不仅被静音的对象,还是需要被反驳和驱逐的污名。
然而在泥塑的矛盾心态背后,是什么支撑起粉丝对其他群体与个人不断的侵犯和攻讦,在他们自诩正义和苦情的内部叙事之后,其狂热心态和扩张举动之下的核心逻辑为何,依然是我们要关心的问题。
## (2)双向造神:“我和他/她都知道,但是,但是”
粉丝们的狂热或许可以在他们塑造的明星形象中找到答案。许多粉丝群体都热衷于将自家爱豆想象成“美强惨”。一方面,他颜值不凡,才华出众;但另一方面,如此优秀的爱豆又处在一个被资本和恶意包围的”无情世界”之中:被资本方摆布,被经纪人操弄,更常被其他的群体中伤。由此,明星的形象酷似宗教叙事中的受难者——德行崇高,并无罪过,却在污浊的尘世中受尽苦难。
而粉丝们往往以追随受难者的殉道者自居。在明星面前,他们自觉渺小,“在现实中,我都不配给这样的美人花钱”是他们常挂嘴边的口头禅。他们唯一能做的就是扮演“无情世界的感情”,帮助爱豆在残酷的商业逻辑下取得成功。当下的粉丝们极少对文化工业的压迫与收编懵然不知,大颇为矛盾的是,他们利用这份清醒加剧了自己的沉沦,而这正是殉道的意义所在——纵然清楚商业资本掌控的无情世界将吞噬普通的消费者粉丝,粉丝们仍愿飞蛾扑火,为爱豆付出自己满溢的情感,更不吝惜自己的金钱,自我感动于殉道者的意象。
这种“受难者”和“殉道者”的叙事之所以在如今的粉丝心理中大行其道,年轻一代原子化的,孤独的生活状态是不可忽视的因素。在精神分析理论中,个人的孤独、渺小一直是一个重要的主题。按照精神分析的理论,在人的成长过程中存在一个所谓的“俄狄浦斯时刻”。在俄狄浦斯时刻前的口腔期,当一个孩子最初吮吸母亲的乳房时,他感到自己的全部欲望(吮吸)都能得到外界的回应和满足。然而,在成长的过程中,他们终将发现外界是一个“异己”的存在,并非所有的欲望都可以被满足,相反,有时尽管不愿,但欲望必须服从于外界的规则。由此,“孤独”和“无力”的感受一直伴随孩子的成长,这种孤独包括而不仅仅是人际关系意义上的孤独,更是外在世界带来的异己感和面对异己世界的无力感。
而今天,作为追星主要群体的年轻一代比他们的长辈更加孤独。中年人或许已有了家庭,拥有稳定的人际关系。在他们的成长过程中,街坊、亲戚、邻里的关系也更为深厚,进而多少缓解了外部世界的“异己”感受。但对于“原子化”的年轻一代来说,追星往往成为了令这种“孤独感”爆发的窗口。
因此,“受难者”和“殉道者”的叙事就成为了孤独感投射的结果。粉丝们之所以认为爱豆身处“无情世界”,是因为他们自己就被异己感和无力感环绕。而当他们看到自己的投入使爱豆一步步在无情世界中杀出一条血路时,他们感到自己的欲望得到了满足,努力得到了回应,异己感和无力感被消解,这也就成为了粉丝们自豪感和成就感的重要来源。而当粉丝们痴迷于这样的自豪感,将“殉道者”的叙事当作了超越孤独和异己感的良方,追星过程中的狂热也就不难被理解。
在追星实践中,“受难”-“殉道”叙事带来的狂热在很多情况下都体现为对消费主义的热情。要帮助自己的爱豆在“无情世界”中突破重围,最直接的方法就是通过支持他所代言的商品来为他赢得 “顶级流量”的身份。这一身份不仅意味着诸多现实的利好,更意味着殉道者们成功完成了自己追随受难者的使命。
除此之外,鲍德里亚早已指出,在当今社会,消费的目的很大程度上已不再是商品带来的使用价值,而是作为“符号”的商品——它标定了个人的身份与认同。因此,支持自家爱豆带货,并让自己的购买行为为超话中的其他同道所知,粉丝们方能确证自己“忠实粉丝”的身份,进而享受属于受难者的自豪和成就感。
## (3)焦虑的迁徙:从消费到安利
相比其他符号性的消费,明星消费更显得“没完没了”,粉丝们往往不知疲倦地为自己的爱豆持续投入。这是因为“顶级流量”的身份富于不确定性:“顶流”的头衔永远基于和其他明星的比较,充满竞争和较量。而且只要竞争还在继续,头衔的归属就时刻可能改变。
因此,每一次“明星带货”都是一场充满了不确定的考验。粉丝们每小时都会统计自家爱豆的带货数量,以便确定他体现出了与“顶级流量”相称的带货能力。然而,一次统计最多只能证明在当次统计之前,爱豆保住了顶级流量的地位,未来瞬息万变,这一头衔可以维持多久难以预料。换言之,“顶级流量”的身份只能从过去中得到确认,却不得不面对来自未来的挑战——这种时间上的错置带来了不可能被消除的不确定性。由此,消费成为了齐格蒙特·鲍曼所说的驱魔仪式,成为了粉丝们缓解焦虑的救命稻草。
作为驱魔仪式,消费的功用在于舒缓不确定性带来的焦虑感。并且无论最后的结果怎样,消费的效果都无法被否定:如果销量巨大,那么“我”便成为了消费大军中的一员,如果销量不够理想,在痛苦之余“我”也能以自己已经尽力来自我安慰。简言之,在充满了不确定性的争夺“顶级流量”的残酷游戏中,不断的“消费”是最能有效应对一切焦虑的驱魔手段。
正因为饭圈要求粉丝们不断地进行消费和投入,为自己的爱豆确立顶流身份。由此,不断吸收新的粉丝,获得新的购买力,就成为了亟欲帮助爱豆维持顶流头衔的粉丝们的必然选择。
在饭圈中,旨在赢得新粉丝的“安利”极为重要。甚至有人喊出了“安利是合格粉丝的终生事业”这样的口号。在消费主义的规训下,原本“自娱自乐”的理想已经从根本上不再可能,一旦为自家爱豆赢得“顶级流量”身份的欲望出现在饭圈之中,饭圈的扩张和话语的传播就已成必然。
而在吸收新血的同时,对流量和商业价值的追逐让粉丝们对一些在他们看来“损害明星商业价值的行为”发起了征讨。一个十分典型的例子就是饭圈对于“泥塑”的态度。泥塑在饭圈遭到抵制的一个重要原因就是,将男爱豆女化的“泥塑”行为破坏了爱豆的“苏感”(对女性群体的吸引力),进而影响爱豆商业价值。由此,基于商业价值和“顶级流量”的身份,消费主义为粉丝们划定了敌我界限。
因此,自我身份建构的需求和多方面推动的饭圈滥化使饭圈不断干涉或吞并其他意识形态,演变为一个凶悍的且组织性极强的机器。至于其未来可能的走向,和在更大的领域可能产生的社会影响,都不可被小觑。征讨和扩张,这几乎是饭圈自诞生就已注定的轨迹。
drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-34154848788850609662021-04-20T20:02:00.001-07:002021-04-20T20:04:19.797-07:00[面经]关于手机窃听<pre class='markdown'/>
# 手机窃听
>华为面试时几个面试官反复提及手机窃听的技术手段问题。
>
>我仅回答了画像圈定问题,没有涉及到潜在技术问题。
>
>所以回来后检索了一下相关信息,才知道原来还有侧信道攻击的事。
常规认为的方式是,APP 申请了麦克风权限,后台静默监听关键字——类似 siri 的响应。
这里闹出过一个全民皆知的笑话——[NEX化身“流氓鉴定器”?升降式摄像头让偷拍无处可藏!](https://www.sohu.com/a/239463633_100206155)
而2019年3·15,《IT 时报》提出了两个技术实现方案,在未授权麦克风权限的情况下,窃听用户谈话关键词。
1. 加速器“窃听”扬声器
2. “浏览器指纹”乱点鸳鸯谱
## 加速器“窃听”扬声器
在网络与分布式系统安全会议(NDSS)上,浙江大学网络空间安全学院任奎团队、加拿大麦吉尔大学、多伦多大学学者团队展示了一项最新的研究成果——智能手机App可在用户不知情、无需系统授权的情况下,利用手机内置加速度传感器采集手机扬声器所发出声音的震动信号,实现对用户语音的窃听。
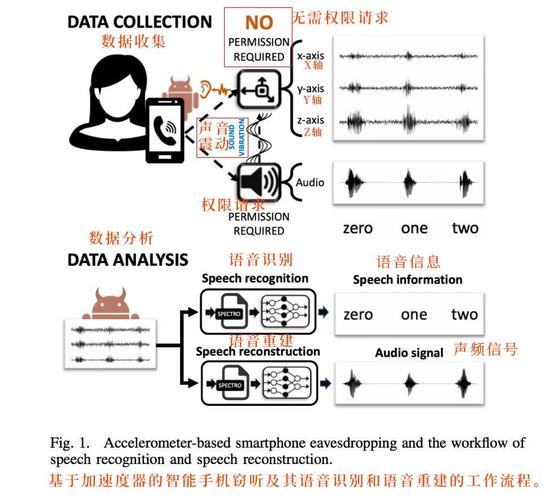
标准的侧信道攻击。
通过加速器感知手机扬声器播放声音时的震动,然后后台算法还原语音,基本可以做到:
- 语音密码识别
- 语音敏感词识别
- 语音还原
但这里技术上<font color=red>**未还原环境音潜在的被窃听风险**</font>。
## “浏览器指纹”乱点鸳鸯谱
这就是我回答里提到的,群体画像精准定位。
这个技术实现难度低,主要窃取和共享在同一局域网内或同一位置区域长期接触的家人、同事、朋友的使用习惯并进行配对和共享推荐,造成的危害相对较小。

这种应该是普遍的手法,安全可靠,群体画像后广告精准投放,转化会更高。当然也会给人留下被偷听的'幸存者偏差'错觉。
## 参考
1. [原来,手机是这样“窃听”你的](https://tech.sina.com.cn/i/2020-03-15/doc-iimxxstf9273990.shtml)drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com1tag:blogger.com,1999:blog-1654671993539634666.post-57470462110243712272021-04-16T02:30:00.002-07:002021-04-17T08:28:47.815-07:00[面经]hook 原理 <pre class="markdown">
# hook原理
>在面微信的时候被开发的面试官问到了hook原理。我简单介绍了一般是替换函数地址的形式,保障先调用替换函数,再调用原始函数。
>
>面试官的理解是有两种hook方式:一种是地址替换型,一种是代码插入型。
>
>由此可知我对hook的不甚了解,所以专门找了相关资料进行学习。如文为学习总结。
## hook方式
Hook技术无论对安全软件还是恶意软件都是十分关键的一项技术,其本质就是劫持函数调用。但是由于处于Linux 用户态,每个进程都有自己独立的进程空间,所以必须先注入到所要Hook 的进程空间,修改其内存中的进程代码,替换其过程表的符号地址。
APP 劫持三步走:
1. 注入进程
- ptrace
- dlopen
2. hook 目标函数
- Java Hook
- Static Field Hook:静态成员hook
- Method Hook:函数hook
- Native So Hook
- GOT Hook:全局偏移表hook
- SYM Hook:符号表hook
- Inline Hook:函数内联hook
3. 执行自身代码
- 获取敏感信息
- 修改返回值
- etc.

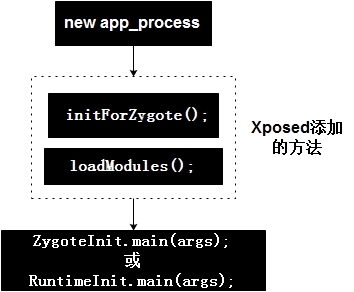
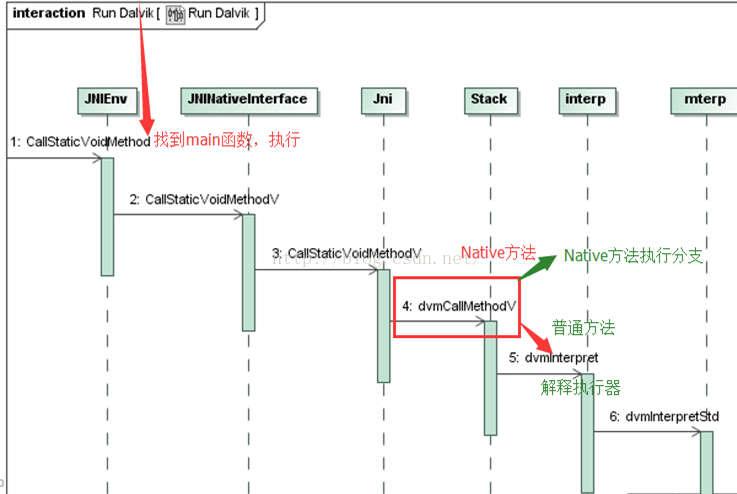
## xposed hook 原理分析
xposed 虽然目前已经不更新了,不过依然是 Android 平台最著名、最广泛使用的 hook 框架。
xposed hook 工作原理:
1. 获取 root 权限
2. 替换/system/bin/app_process
3. app_process在启动过程中会加载XposedBridge.jar,完成对Zygote进程及其创建的Dalvik虚拟机的劫持
4. XposedBridge.jar中会根据用户所编写的 xposed 模块,对对应 classloader 中的 method 进行替换
```
/**
*
* 将输入的Class中的Method方法的nativeFunc替换为xposedCallHandler
*
* @param env JniEnv
* @param reflectedMethodIndirect 待反射的函数
* @param declaredClassIndirect 定义的class
* @param slot 函数偏移量
* @param additionalInfoIndirect 添加的函数
*
*/
void XposedBridge_hookMethodNative(JNIEnv* env, jclass clazz, jobject reflectedMethodIndirect,
jobject declaredClassIndirect, jint slot, jobject additionalInfoIndirect) {
// 容错
if (declaredClassIndirect == NULL || reflectedMethodIndirect == NULL) {
dvmThrowIllegalArgumentException("method and declaredClass must not be null");
return;
}
// 根据函数的偏移量,从classloader中找到准备替换的函数。
ClassObject* declaredClass = (ClassObject*) dvmDecodeIndirectRef(dvmThreadSelf(), declaredClassIndirect);
Method* method = dvmSlotToMethod(declaredClass, slot);
if (method == NULL) {
dvmThrowNoSuchMethodError("Could not get internal representation for method");
return;
}
if (isMethodHooked(method)) {
// already hooked
return;
}
// 保存替换前的数据信息
XposedHookInfo* hookInfo = (XposedHookInfo*) calloc(1, sizeof(XposedHookInfo));
memcpy(hookInfo, method, sizeof(hookInfo->originalMethodStruct));
hookInfo->reflectedMethod = dvmDecodeIndirectRef(dvmThreadSelf(), env->NewGlobalRef(reflectedMethodIndirect));
hookInfo->additionalInfo = dvmDecodeIndirectRef(dvmThreadSelf(), env->NewGlobalRef(additionalInfoIndirect));
// 替换函数方法 , 让nativeFunction指向本地的hookedMethodCallback
SET_METHOD_FLAG(method, ACC_NATIVE);
method->nativeFunc = &hookedMethodCallback;
method->insns = (const u2*) hookInfo;
method->registersSize = method->insSize;
method->outsSize = 0;
if (PTR_gDvmJit != NULL) {
// reset JIT cache
char currentValue = *((char*)PTR_gDvmJit + MEMBER_OFFSET_VAR(DvmJitGlobals,codeCacheFull));
if (currentValue == 0 || currentValue == 1) {
MEMBER_VAL(PTR_gDvmJit, DvmJitGlobals, codeCacheFull) = true;
} else {
ALOGE("Unexpected current value for codeCacheFull: %d", currentValue);
}
}
}
```
## frida hook 原理
frida代码结构:
```
frida-core: Frida core library intended for static linking into bindings
frida-gum: Low-level code instrumentation library used by frida-core bindings
frida-python: Frida Python bindings
frida-node: Frida Node.js bindings
frida-qml: Frida Qml plugin
frida-swift: Frida Swift bindings
frida-tools: Frida CLI tools
capstone: instruction disammbler
```
frida的工作模式有两种:
- attach模式
attach到已经存在的进程,核心原理是ptrace修改进程内存,如果进程处于调试状态(traceid不等于0),则attach失败
- spawn模式
启动一个新的进程并挂起,在启动的同时注入frida代码,适用于在进程启动前的一些hook,如hook RegisterNative等,注入完成后调用resume恢复进程。
frida 的 hook 区分了 art 模式和 dalvik 模式。
### Dalvik hook 实现
frida兼容了低版本的Android, 低于Android 5.0时,采用Dalvik虚拟机,其核心实现在replaceDalvikImplementation函数中。
frida-dalvik-hook 的原理和 xposed 的 hook 原理是一样的,把 java 函数变成 native 函数,然后修改入口信息为自定义函数信息。
```
//https://android.googlesource.com/platform/dalvik/+/6d874d2bda563ada1034d2b3219b35d800fc6860/vm/oo/Object.h#418
struct Method {
ClassObject* clazz; /* method所属的类 public、native等*/
u4 accessFlags; /* 访问标记 */
u2 methodIndex; //method索引
//三个size为边界值,对于native函数,这3个size均等于参数列表的size
u2 registersSize; /* ins + locals */
u2 outsSize;
u2 insSize;
const char* name;//函数名称
/*
* Method prototype descriptor string (return and argument types)
*/
DexProto prototype;
/* short-form method descriptor string */
const char* shorty;
/*
* The remaining items are not used for abstract or native methods.
* (JNI is currently hijacking "insns" as a function pointer, set
* after the first call. For internal-native this stays null.)
*/
/* the actual code */
const u2* insns; /* instructions, in memory-mapped .dex */
/* cached JNI argument and return-type hints */
int jniArgInfo;
/*
* Native method ptr; could be actual function or a JNI bridge. We
* don't currently discriminate between DalvikBridgeFunc and
* DalvikNativeFunc; the former takes an argument superset (i.e. two
* extra args) which will be ignored. If necessary we can use
* insns==NULL to detect JNI bridge vs. internal native.
*/
DalvikBridgeFunc nativeFunc;
/*
* Register map data, if available. This will point into the DEX file
* if the data was computed during pre-verification, or into the
* linear alloc area if not.
*/
const RegisterMap* registerMap;
};
…
…
…
function replaceDalvikImplementation (fn) {
if (fn === null && dalvikOriginalMethod === null) {
return;
}
//备份原来的method,
if (dalvikOriginalMethod === null) {
dalvikOriginalMethod = Memory.dup(methodId, DVM_METHOD_SIZE);
dalvikTargetMethodId = Memory.dup(methodId, DVM_METHOD_SIZE);
}
if (fn !== null) {
//自定的代码
implementation = implement(f, fn);
let argsSize = argTypes.reduce((acc, t) => (acc + t.size), 0);
if (type === INSTANCE_METHOD) {
argsSize++;
}
// 把method变成native函数
/*
* make method native (with kAccNative)
* insSize and registersSize are set to arguments size
*/
const accessFlags = (Memory.readU32(methodId.add(DVM_METHOD_OFFSET_ACCESS_FLAGS)) | kAccNative) >>> 0;
const registersSize = argsSize;
const outsSize = 0;
const insSize = argsSize;
Memory.writeU32(methodId.add(DVM_METHOD_OFFSET_ACCESS_FLAGS), accessFlags);
Memory.writeU16(methodId.add(DVM_METHOD_OFFSET_REGISTERS_SIZE), registersSize);
Memory.writeU16(methodId.add(DVM_METHOD_OFFSET_OUTS_SIZE), outsSize);
Memory.writeU16(methodId.add(DVM_METHOD_OFFSET_INS_SIZE), insSize);
Memory.writeU32(methodId.add(DVM_METHOD_OFFSET_JNI_ARG_INFO), computeDalvikJniArgInfo(methodId));
//调用dvmUseJNIBridge为这个Method设置一个Bridge,本质上是修改结构体中的nativeFunc为自定义的implementation函数
api.dvmUseJNIBridge(methodId, implementation);
patchedMethods.add(f);
} else {
patchedMethods.delete(f);
Memory.copy(methodId, dalvikOriginalMethod, DVM_METHOD_SIZE);
implementation = null;
}
}
```
### ART hook实现
frida的ART hook实现也是把java method转为native method, 但ART的运行机制不同于Dalvik, 其实现也较为复杂。
ART虚拟机执行 Java 方法主要有两种模式:
- quick code 模式:执行 arm 汇编指令
- Interpreter 模式:由解释器解释执行 Dalvik 字节码
所以 frida 要将 java method 转为 native method,需要将ARTMethod 结构进行如下修改:
```
patchMethod(methodId, {
//jnicode入口entry_point_from_jni_改为自定义的代码
'jniCode': implementation,
//修改为access_flags_为native
'accessFlags': (Memory.readU32(methodId.add(artMethodOffset.accessFlags)) | kAccNative | kAccFastNative) >>> 0,
//art_quick_generic_jni_trampoline函数的地址
'quickCode': api.artQuickGenericJniTrampoline,
//artInterpreterToCompiledCodeBridge函数地址
'interpreterCode': api.artInterpreterToCompiledCodeBridge
});
```
参考链接
1. [动态注入技术(hook技术)](https://www.kancloud.cn/alex_wsc/android/504478)
2. [Xposed源码剖析——概述](https://blog.csdn.net/yzzst/article/details/47659987)
3. [Xposed源码剖析——app_process作用详解](https://blog.csdn.net/yzzst/article/details/47829657)
4. [Xposed源码剖析——Xposed初始化](https://blog.csdn.net/yzzst/article/details/47834077)
5. [Xposed源码剖析——hook具体实现](https://blog.csdn.net/yzzst/article/details/47913867)
6. [Frida源码分析](https://mabin004.github.io/2018/07/31/Mac%E4%B8%8A%E7%BC%96%E8%AF%91Frida/)
</pre>drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-61769567260476208212021-02-25T00:32:00.006-08:002021-02-25T00:32:54.237-08:00Frida hook java 层调用栈,用于回溯调用关系<div style="background-color: #1e1e1e; color: #d4d4d4; font-family: Menlo, Monaco, "Courier New", monospace; font-size: 12px; line-height: 18px; white-space: pre;"><div><span style="color: #6a9955;">//调用方法</span></div><div><span style="color: #569cd6;">function</span> <span style="color: #dcdcaa;">printStack</span>() {</div><div> <span style="color: #569cd6;">var</span> <span style="color: #9cdcfe;">Exception</span>= <span style="color: #9cdcfe;">Java</span>.<span style="color: #dcdcaa;">use</span>(<span style="color: #ce9178;">"java.lang.Exception"</span>);</div><div> <span style="color: #569cd6;">var</span> <span style="color: #9cdcfe;">ins</span> = <span style="color: #9cdcfe;">Exception</span>.<span style="color: #dcdcaa;">$new</span>(<span style="color: #ce9178;">"Exception"</span>);</div><div> <span style="color: #569cd6;">var</span> <span style="color: #9cdcfe;">straces</span> = <span style="color: #9cdcfe;">ins</span>.<span style="color: #dcdcaa;">getStackTrace</span>();</div><br /><div> <span style="color: #c586c0;">if</span> (<span style="color: #569cd6;">undefined</span> == <span style="color: #9cdcfe;">straces</span> || <span style="color: #569cd6;">null</span> == <span style="color: #9cdcfe;">straces</span>) </div><div> {</div><div> <span style="color: #c586c0;">return</span>;</div><div> }</div><br /><div> <span style="color: #9cdcfe;">console</span>.<span style="color: #dcdcaa;">log</span>(<span style="color: #ce9178;">"=============================Stack start======================="</span>);</div><div> <span style="color: #6a9955;">// console.log(JSON.stringify(straces[0]));</span></div><div> <span style="color: #c586c0;">for</span> (<span style="color: #569cd6;">var</span> <span style="color: #9cdcfe;">i</span> = <span style="color: #b5cea8;">0</span>; <span style="color: #9cdcfe;">i</span> < <span style="color: #9cdcfe;">straces</span>.<span style="color: #9cdcfe;">length</span>; <span style="color: #9cdcfe;">i</span>++)</div><div> {</div><div> <span style="color: #569cd6;">var</span> <span style="color: #9cdcfe;">str</span> = <span style="color: #ce9178;">" "</span> + <span style="color: #9cdcfe;">JSON</span>.<span style="color: #dcdcaa;">stringify</span>(<span style="color: #9cdcfe;">straces</span>[<span style="color: #9cdcfe;">i</span>].<span style="color: #dcdcaa;">getClassName</span>());//关键变更点,<span style="color: #dcdcaa;">getStackTrace获取的是类,需要取类名信息才能有效打印</span></div><div> <span style="color: #9cdcfe;">console</span>.<span style="color: #dcdcaa;">log</span>(<span style="color: #9cdcfe;">str</span>);</div><div> }</div><br /><div> <span style="color: #9cdcfe;">console</span>.<span style="color: #dcdcaa;">log</span>(<span style="color: #ce9178;">""</span>);</div><div> <span style="color: #9cdcfe;">console</span>.<span style="color: #dcdcaa;">log</span>(<span style="color: #ce9178;">"=============================Stack end=======================</span><span style="color: #d7ba7d;">\r\n</span><span style="color: #ce9178;">"</span>);</div><div> <span style="color: #9cdcfe;">Exception</span>.<span style="color: #dcdcaa;">$dispose</span>();</div><div>}</div><div><span style="color: #6a9955;">//以下为使用方法</span></div><div><span style="color: #9cdcfe;">Java</span>.<span style="color: #dcdcaa;">perform</span>(<span style="color: #569cd6;">function</span> () {</div><br /><div> <span style="color: #569cd6;">const</span> <span style="color: #4fc1ff;">StringBuilder</span> = <span style="color: #9cdcfe;">Java</span>.<span style="color: #dcdcaa;">use</span>(<span style="color: #ce9178;">'java.lang.StringBuilder'</span>);</div><div> <span style="color: #4fc1ff;">StringBuilder</span>.<span style="color: #9cdcfe;">toString</span>.<span style="color: #dcdcaa;">implementation</span> = <span style="color: #569cd6;">function</span> () {</div><div> <span style="color: #6a9955;">// send("in StringBuiler");</span></div><div> <span style="color: #569cd6;">var</span> <span style="color: #9cdcfe;">result</span> = <span style="color: #569cd6;">this</span>.<span style="color: #dcdcaa;">toString</span>();</div><div> <span style="color: #9cdcfe;">console</span>.<span style="color: #dcdcaa;">log</span>(<span style="color: #ce9178;">"=============================Stack Print=======================</span><span style="color: #d7ba7d;">\r\n</span><span style="color: #ce9178;">"</span>);</div><div> <span style="color: #9cdcfe;">console</span>.<span style="color: #dcdcaa;">log</span>(<span style="color: #9cdcfe;">result</span>);</div><div> <span style="color: #c586c0;">return</span> <span style="color: #9cdcfe;">result</span>;</div><div> };</div></div><p><span style="background-color: #1e1e1e; color: #d4d4d4; font-family: Menlo, Monaco, "Courier New", monospace; font-size: 12px; white-space: pre;">});</span> </p>drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-63316297246255887362021-02-22T03:46:00.003-08:002021-02-22T03:46:41.397-08:00后缀为 .xls 的excel文件保护密码爆破<p> 打开后缀为xls的excel文件,alt+f11呼出VBA。</p><p>双击<span style="background-color: white; color: #404040; font-family: -apple-system, BlinkMacSystemFont, "Apple Color Emoji", "Segoe UI Emoji", "Segoe UI Symbol", "Segoe UI", "PingFang SC", "Hiragino Sans GB", "Microsoft YaHei", "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 16px;">ThisWorkbook,新建一个代码。</span></p><p><span style="background-color: white; color: #404040; font-family: -apple-system, BlinkMacSystemFont, "Apple Color Emoji", "Segoe UI Emoji", "Segoe UI Symbol", "Segoe UI", "PingFang SC", "Hiragino Sans GB", "Microsoft YaHei", "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 16px;">然后复制粘贴如下爆破代码,点击运行即可。</span></p><pre class="line-numbers language-php" style="background: rgb(45, 45, 45); border-radius: 4px; box-sizing: border-box; color: #cccccc; counter-reset: linenumber 0; font-family: Consolas, Monaco, "Andale Mono", "Ubuntu Mono", monospace; font-size: 12px; hyphens: none; line-height: 1.5; margin-bottom: 20px; margin-top: 0px; overflow-wrap: normal; overflow: scroll auto; overscroll-behavior-x: contain; padding: 1em 1em 1em 3.8em; position: relative; tab-size: 4; word-break: break-all; z-index: 0;"><code class=" language-php" style="background: none transparent; border: none; box-sizing: border-box; color: inherit; font-family: Consolas, Monaco, "Andale Mono", "Ubuntu Mono", monospace; font-size: 1em; hyphens: none; line-height: 1.5; overflow-wrap: normal; padding: 0px; position: relative; tab-size: 4; vertical-align: unset; white-space: inherit; word-break: normal; word-spacing: normal;"><span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Public</span> Sub 工作表保护密码破解<span class="token punctuation" style="box-sizing: border-box;">(</span><span class="token punctuation" style="box-sizing: border-box;">)</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Const</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">DBLSPACE</span> <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> String <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> vbNewLine <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> vbNewLine
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Const</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">AUTHORS</span> <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> String <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">DBLSPACE</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> vbNewLine <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">_</span>
<span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"作者:McCormick JE McGimpsey "</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Const</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">HEADER</span> <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> String <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"工作表保护密码破解"</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Const</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">VERSION</span> <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> String <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">DBLSPACE</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"版本 Version 1.1.1"</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Const</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">REPBACK</span> <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> String <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">DBLSPACE</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">""</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Const</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">ZHENGLI</span> <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> String <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">DBLSPACE</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">""</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Const</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">ALLCLEAR</span> <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> String <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">DBLSPACE</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"该工作簿中的工作表密码保护已全部解除!!"</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">DBLSPACE</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"请记得另保存"</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">_</span>
<span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">DBLSPACE</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"注意:不要用在不当地方,要尊重他人的劳动成果!"</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Const</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">MSGNOPWORDS1</span> <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> String <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"该文件工作表中没有加密"</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Const</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">MSGNOPWORDS2</span> <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> String <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"该文件工作表中没有加密2"</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Const</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">MSGTAKETIME</span> <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> String <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"解密需花费一定时间,请耐心等候!"</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">DBLSPACE</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"按确定开始破解!"</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Const</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">MSGPWORDFOUND1</span> <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> String <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"密码重新组合为:"</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">DBLSPACE</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"$$"</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">DBLSPACE</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">_</span>
<span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"如果该文件工作表有不同密码,将搜索下一组密码并修改清除"</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Const</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">MSGPWORDFOUND2</span> <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> String <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"密码重新组合为:"</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">DBLSPACE</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"$$"</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">DBLSPACE</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">_</span>
<span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"如果该文件工作表有不同密码,将搜索下一组密码并解除"</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Const</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">MSGONLYONE</span> <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> String <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> <span class="token double-quoted-string string" style="box-sizing: border-box; color: #7ec699;">"确保为唯一的?"</span>
Dim w1 <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Worksheet<span class="token punctuation" style="box-sizing: border-box;">,</span> w2 <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Worksheet
Dim i <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Integer<span class="token punctuation" style="box-sizing: border-box;">,</span> j <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Integer<span class="token punctuation" style="box-sizing: border-box;">,</span> k <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Integer<span class="token punctuation" style="box-sizing: border-box;">,</span> l <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Integer
Dim m <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Integer<span class="token punctuation" style="box-sizing: border-box;">,</span> n <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Integer<span class="token punctuation" style="box-sizing: border-box;">,</span> i1 <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Integer<span class="token punctuation" style="box-sizing: border-box;">,</span> i2 <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Integer
Dim i3 <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Integer<span class="token punctuation" style="box-sizing: border-box;">,</span> i4 <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Integer<span class="token punctuation" style="box-sizing: border-box;">,</span> i5 <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Integer<span class="token punctuation" style="box-sizing: border-box;">,</span> i6 <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Integer
Dim PWord1 <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> String
Dim ShTag <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Boolean<span class="token punctuation" style="box-sizing: border-box;">,</span> WinTag <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">As</span> Boolean
Application<span class="token punctuation" style="box-sizing: border-box;">.</span>ScreenUpdating <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> <span class="token boolean constant" style="box-sizing: border-box; color: #f8c555;">False</span>
With ActiveWorkbook
WinTag <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> <span class="token punctuation" style="box-sizing: border-box;">.</span>ProtectStructure <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Or</span> <span class="token punctuation" style="box-sizing: border-box;">.</span>ProtectWindows
End With
ShTag <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> <span class="token boolean constant" style="box-sizing: border-box; color: #f8c555;">False</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">For</span> Each w1 In Worksheets
ShTag <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> ShTag <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Or</span> w1<span class="token punctuation" style="box-sizing: border-box;">.</span>ProtectContents
Next w1
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">If</span> Not ShTag <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">And</span> Not WinTag Then
MsgBox <span class="token constant" style="box-sizing: border-box; color: #f8c555;">MSGNOPWORDS1</span><span class="token punctuation" style="box-sizing: border-box;">,</span> vbInformation<span class="token punctuation" style="box-sizing: border-box;">,</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">HEADER</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Exit</span> Sub
End <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">If</span>
MsgBox <span class="token constant" style="box-sizing: border-box; color: #f8c555;">MSGTAKETIME</span><span class="token punctuation" style="box-sizing: border-box;">,</span> vbInformation<span class="token punctuation" style="box-sizing: border-box;">,</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">HEADER</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">If</span> Not WinTag Then
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Else</span>
On Error Resume Next
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Do</span> <span class="token single-quoted-string string" style="box-sizing: border-box; color: #7ec699;">'dummy do loop
For i = 65 To 66: For j = 65 To 66: For k = 65 To 66
For l = 65 To 66: For m = 65 To 66: For i1 = 65 To 66
For i2 = 65 To 66: For i3 = 65 To 66: For i4 = 65 To 66
For i5 = 65 To 66: For i6 = 65 To 66: For n = 32 To 126
With ActiveWorkbook
.Unprotect Chr(i) & Chr(j) & Chr(k) & _
Chr(l) & Chr(m) & Chr(i1) & Chr(i2) & _
Chr(i3) & Chr(i4) & Chr(i5) & Chr(i6) & Chr(n)
If .ProtectStructure = False And _
.ProtectWindows = False Then
PWord1 = Chr(i) & Chr(j) & Chr(k) & Chr(l) & _
Chr(m) & Chr(i1) & Chr(i2) & Chr(i3) & _
Chr(i4) & Chr(i5) & Chr(i6) & Chr(n)
MsgBox Application.Substitute(MSGPWORDFOUND1, _
"$$", PWord1), vbInformation, HEADER
Exit Do '</span>Bypass all <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">for</span><span class="token punctuation" style="box-sizing: border-box;">.</span><span class="token punctuation" style="box-sizing: border-box;">.</span><span class="token punctuation" style="box-sizing: border-box;">.</span>nexts
End <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">If</span>
End With
Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next
Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next
Loop Until <span class="token boolean constant" style="box-sizing: border-box; color: #f8c555;">True</span>
On Error <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">GoTo</span> <span class="token number" style="box-sizing: border-box; color: #f08d49;">0</span>
End <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">If</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">If</span> WinTag <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">And</span> Not ShTag Then
MsgBox <span class="token constant" style="box-sizing: border-box; color: #f8c555;">MSGONLYONE</span><span class="token punctuation" style="box-sizing: border-box;">,</span> vbInformation<span class="token punctuation" style="box-sizing: border-box;">,</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">HEADER</span>
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Exit</span> Sub
End <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">If</span>
On Error Resume Next
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">For</span> Each w1 In Worksheets
<span class="token single-quoted-string string" style="box-sizing: border-box; color: #7ec699;">'Attempt clearance with PWord1
w1.Unprotect PWord1
Next w1
On Error GoTo 0
ShTag = False
For Each w1 In Worksheets
'</span>Checks <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">for</span> all clear ShTag triggered to <span class="token number" style="box-sizing: border-box; color: #f08d49;">1</span> <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">if</span> not<span class="token punctuation" style="box-sizing: border-box;">.</span>
ShTag <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">=</span> ShTag <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Or</span> w1<span class="token punctuation" style="box-sizing: border-box;">.</span>ProtectContents
Next w1
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">If</span> ShTag Then
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">For</span> Each w1 In Worksheets
With w1
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">If</span> <span class="token punctuation" style="box-sizing: border-box;">.</span>ProtectContents Then
On Error Resume Next
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Do</span> <span class="token single-quoted-string string" style="box-sizing: border-box; color: #7ec699;">'Dummy do loop
For i = 65 To 66: For j = 65 To 66: For k = 65 To 66
For l = 65 To 66: For m = 65 To 66: For i1 = 65 To 66
For i2 = 65 To 66: For i3 = 65 To 66: For i4 = 65 To 66
For i5 = 65 To 66: For i6 = 65 To 66: For n = 32 To 126
.Unprotect Chr(i) & Chr(j) & Chr(k) & _
Chr(l) & Chr(m) & Chr(i1) & Chr(i2) & Chr(i3) & _
Chr(i4) & Chr(i5) & Chr(i6) & Chr(n)
If Not .ProtectContents Then
PWord1 = Chr(i) & Chr(j) & Chr(k) & Chr(l) & _
Chr(m) & Chr(i1) & Chr(i2) & Chr(i3) & _
Chr(i4) & Chr(i5) & Chr(i6) & Chr(n)
MsgBox Application.Substitute(MSGPWORDFOUND2, _
"$$", PWord1), vbInformation, HEADER
'</span>leverage finding Pword by trying on other sheets
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">For</span> Each w2 In Worksheets
w2<span class="token punctuation" style="box-sizing: border-box;">.</span>Unprotect PWord1
Next w2
<span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Exit</span> <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">Do</span> 'Bypass all <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">for</span><span class="token punctuation" style="box-sizing: border-box;">.</span><span class="token punctuation" style="box-sizing: border-box;">.</span><span class="token punctuation" style="box-sizing: border-box;">.</span>nexts
End <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">If</span>
Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next
Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next<span class="token punctuation" style="box-sizing: border-box;">:</span> Next
Loop Until <span class="token boolean constant" style="box-sizing: border-box; color: #f8c555;">True</span>
On Error <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">GoTo</span> <span class="token number" style="box-sizing: border-box; color: #f08d49;">0</span>
End <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">If</span>
End With
Next w1
End <span class="token keyword" style="box-sizing: border-box; color: #cc99cd;">If</span>
MsgBox <span class="token constant" style="box-sizing: border-box; color: #f8c555;">ALLCLEAR</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">AUTHORS</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">VERSION</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">REPBACK</span> <span class="token operator" style="box-sizing: border-box; color: #67cdcc;">&</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">ZHENGLI</span><span class="token punctuation" style="box-sizing: border-box;">,</span> vbInformation<span class="token punctuation" style="box-sizing: border-box;">,</span> <span class="token constant" style="box-sizing: border-box; color: #f8c555;">HEADER</span>
End Sub</code></pre>drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com1tag:blogger.com,1999:blog-1654671993539634666.post-61331750648236303302020-12-29T04:32:00.002-08:002021-04-15T08:03:02.148-07:00M1的 MACOS (理论上)安装任意 iOS APP 的方案<br />苹果M1芯片基于ARM可直接在新版 MacBook 上使用iOS应用 , 也就是多数iOS应用都可以在MacBook上使用。<br /><br />不过部分 APP 依然不支持在MacBook 上安装(在 appstore 上搜索不到),于是大家就开始直接下载 ipa 包进行安装运行了。<br /><br />为了避免从第三方平台下载导致的安全问题,找到一个通过 '同步/备份机制' 绕过下载验证的方案,具体方案如下,理论上可安装任意 iOS APP。<div><br /><div><ol style="text-align: left;"><li>在macOS应用商店里下载<a href="https://www.blogger.com/#">Apple Configurator 2</a>工具 ,安装该软件后打开并连接你的iPhone或iPad下载APP。</li><li>在Apple Configurator 2工具里点击你连接的iPhone或iPad , 然后右键选择添加、添加APP、搜索你要的APP。</li><li>找到你要的APP后点击添加就可以自动下载 , 下载完成会提示你的设备已存在该应用,此时切记不要点击替换。(这里注意到,保持该界面不动,先进行4,提取缓存的 ipa 文件后再处理这里的应用;另,如果设备未安装,会直接进行安装,不会保留缓存 ipa 文件。)</li><li>使用快捷键组合Command+Shift+G打开以下路径,打开这个路径就可以看到下载好的IPA文件将其复制出来。</li></ol><div><pre class="prettyprint linenums prettyprinted" style="background-color: #272822; box-sizing: border-box; color: #f8f8f2; font-size: 15px; margin-bottom: 12px; margin-top: 12px; overflow-wrap: break-word; overflow-x: auto; padding: 12px 0px; white-space: pre-wrap;"><ol class="linenums" style="background: transparent; border: 0px; box-sizing: border-box; margin: 0px 0px 0px 40px; padding: 0px 0px 0px 12px;"><li class="L0" style="box-sizing: border-box; color: #bebec5; font-size: 13px; line-height: 24px; list-style: decimal; padding-left: 8px;"><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">~</span><span class="str" style="background: transparent; border: 0px; box-sizing: border-box; color: #e6db74; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">/Library/</span><span class="typ" style="background: transparent; border: 0px; box-sizing: border-box; color: #a6e22e; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">Group</span><span class="pln" style="background: transparent; border: 0px; box-sizing: border-box; color: #66d9ef; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;"> </span><span class="typ" style="background: transparent; border: 0px; box-sizing: border-box; color: #a6e22e; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">Containers</span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">/</span><span class="pln" style="background: transparent; border: 0px; box-sizing: border-box; color: #66d9ef; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">K36BKF7T3D</span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">.</span><span class="kwd" style="background: transparent; border: 0px; box-sizing: border-box; color: #f92659; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">group</span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">.</span><span class="pln" style="background: transparent; border: 0px; box-sizing: border-box; color: #66d9ef; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">com</span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">.</span><span class="pln" style="background: transparent; border: 0px; box-sizing: border-box; color: #66d9ef; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">apple</span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">.</span><span class="pln" style="background: transparent; border: 0px; box-sizing: border-box; color: #66d9ef; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">configurator</span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">/</span><span class="typ" style="background: transparent; border: 0px; box-sizing: border-box; color: #a6e22e; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">Library</span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">/</span><span class="typ" style="background: transparent; border: 0px; box-sizing: border-box; color: #a6e22e; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">Caches</span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">/</span><span class="typ" style="background: transparent; border: 0px; box-sizing: border-box; color: #a6e22e; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">Assets</span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">/</span><span class="typ" style="background: transparent; border: 0px; box-sizing: border-box; color: #a6e22e; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">TemporaryItems</span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">/</span><span class="typ" style="background: transparent; border: 0px; box-sizing: border-box; color: #a6e22e; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">MobileApps</span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">/</span></li></ol></pre><span> </span></div><blockquote style="border: none; margin: 0 0 0 40px; padding: 0px;"><div style="text-align: left;">5. 双击IPA文件进行安装 , 打开会报错没有权限 , 打开终端然后输入以下命令对特定路径的APP进行权限处理即可。</div></blockquote><div><pre class="prettyprint linenums prettyprinted" style="background-color: #272822; box-sizing: border-box; color: #f8f8f2; font-size: 15px; margin-bottom: 12px; margin-top: 12px; overflow-wrap: break-word; overflow-x: auto; padding: 12px 0px; white-space: pre-wrap;"><ol class="linenums" style="background: transparent; border: 0px; box-sizing: border-box; margin: 0px 0px 0px 40px; padding: 0px 0px 0px 12px;"><li class="L0" style="box-sizing: border-box; color: #bebec5; font-size: 13px; line-height: 24px; list-style: decimal; padding-left: 8px;"><span class="pln" style="background: transparent; border: 0px; box-sizing: border-box; color: #66d9ef; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">sudo xattr </span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">-</span><span class="pln" style="background: transparent; border: 0px; box-sizing: border-box; color: #66d9ef; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">r </span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">-</span><span class="pln" style="background: transparent; border: 0px; box-sizing: border-box; color: #66d9ef; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">d com</span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">.</span><span class="pln" style="background: transparent; border: 0px; box-sizing: border-box; color: #66d9ef; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">apple</span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">.</span><span class="pln" style="background: transparent; border: 0px; box-sizing: border-box; color: #66d9ef; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">quarantine </span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">/</span><span class="typ" style="background: transparent; border: 0px; box-sizing: border-box; color: #a6e22e; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">Applications</span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">/</span><span class="typ" style="background: transparent; border: 0px; box-sizing: border-box; color: #a6e22e; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">WeChat</span><span class="pun" style="background: transparent; border: 0px; box-sizing: border-box; color: #f8f8f2; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">.</span><span class="pln" style="background: transparent; border: 0px; box-sizing: border-box; color: #66d9ef; margin: 0px; padding: 0px; transition: all 0.5s ease-in-out 0s;">app</span></li></ol></pre><audio controls="controls" style="display: none;"></audio></div></div></div>drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-68894304819878324432020-11-26T04:18:00.004-08:002020-12-23T05:50:11.634-08:00[日常修复] MACOS 升级后,git 命令执行报错: missing xcrun at: /Library/Developer/CommandLineTools/usr/bin/xcrun<p></p><p></p><p></p><div class="markdown-here-wrapper" data-md-url="https://www.blogger.com/blog/post/edit/1654671993539634666/6889430481987832443"><p style="margin: 0px 0px 1.2em !important;"> 报错信息:</p>
<pre style="font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; font-size: 1em; line-height: 1.2em; margin: 1.2em 0px;"><code style="background-color: #f8f8f8; border-radius: 3px; border-radius: 3px; border: 1px solid rgb(204, 204, 204); border: 1px solid rgb(234, 234, 234); display: block !important; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0.5em 0.7em; padding: 0px 0.3em; white-space: pre-wrap; white-space: pre;">~ $ git
xcrun: error: invalid active developer path (/Library/Developer/CommandLineTools), missing xcrun at: /Library/Developer/CommandLineTools/usr/bin/xcrun
</code></pre><p style="margin: 0px 0px 1.2em !important;">修复方案:</p>
<pre style="font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; font-size: 1em; line-height: 1.2em; margin: 1.2em 0px;"><code style="background-color: #f8f8f8; border-radius: 3px; border-radius: 3px; border: 1px solid rgb(204, 204, 204); border: 1px solid rgb(234, 234, 234); display: block !important; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0.5em 0.7em; padding: 0px 0.3em; white-space: pre-wrap; white-space: pre;">~ $ xcode-select --install
xcode-select: note: install requested for command line developer tools
</code></pre><p style="margin: 0px 0px 1.2em !important;">触发 xcode 更新,确认更新即可。</p>
<div style="font-size: 0em; height: 0; margin: 0; max-height: 0; max-width: 0; overflow: hidden; padding: 0; width: 0;" title="MDH:PHA+Jm5ic3A75oql6ZSZ5L+h5oGv77yaPC9wPjxwPmBgYDwvcD48cD5+ICQgZ2l0PC9wPjxwPnhj
cnVuOiBlcnJvcjogaW52YWxpZCBhY3RpdmUgZGV2ZWxvcGVyIHBhdGggKC9MaWJyYXJ5L0RldmVs
b3Blci9Db21tYW5kTGluZVRvb2xzKSwgbWlzc2luZyB4Y3J1biBhdDogL0xpYnJhcnkvRGV2ZWxv
cGVyL0NvbW1hbmRMaW5lVG9vbHMvdXNyL2Jpbi94Y3J1bjwvcD48cD5gYGA8L3A+PHA+5L+u5aSN
5pa55qGI77yaPC9wPjxwPmBgYDwvcD48cD5+ICQgeGNvZGUtc2VsZWN0IC0taW5zdGFsbDwvcD48
cD54Y29kZS1zZWxlY3Q6IG5vdGU6IGluc3RhbGwgcmVxdWVzdGVkIGZvciBjb21tYW5kIGxpbmUg
ZGV2ZWxvcGVyIHRvb2xzPC9wPjxwPmBgYDwvcD48cD48YnI+PC9wPjxwPuinpuWPkSB4Y29kZSDm
m7TmlrDvvIznoa7orqTmm7TmlrDljbPlj6/jgII8L3A+PHA+PC9wPg=="></div></div><p><br /></p><p><br /></p><p><br /></p><p></p><p></p>drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com1tag:blogger.com,1999:blog-1654671993539634666.post-82893299865683647442020-07-22T19:22:00.000-07:002020-07-22T19:22:37.925-07:00[转]AFL(二)afl-qemu无源码fuzz<div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;">使用brew/apt方式安装的afl没有afl-qemu-trace(不支持使用QEMU模式),所以我们需要下载afl的源码自己编译。</div><h2 id="0x1-" style="-webkit-text-stroke-width: 0.3px; background-color: white; border-bottom: 1px solid rgb(238, 238, 238); box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 1.4em; margin: 1.3em 0px 1em; padding: 0px;">0x1 安装配置</h2><div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;">编译完成后,需要配置qemu环境。不过,afl提供了一个脚本,在<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">qemu-mode</code>文件夹下的<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">build_qemu_support.sh</code>。运行这个脚本来配置qemu环境,但qemu-mode只支持linux,macOS可以在docker上使用,docker使用参考<a href="http://www.gandalf.site/2018/12/macoskali-linux-for-docker.html" style="background: transparent; box-sizing: border-box; color: lightseagreen; text-decoration-line: none;">macOS上使用kali-linux for docker</a>:</div><pre style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">$ ./build_qemu_support.sh
=================================================
AFL binary-only instrumentation QEMU build script
=================================================
[*] Performing basic sanity checks...
[-] Error: QEMU instrumentation is supported only on Linux.
</code></pre><div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;">编译成功信息如下:</div><pre style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">[+] Build process successful!
[*] Copying binary...
-rwxr-xr-x 1 root root 10956864 Dec 13 12:26 ../afl-qemu-trace
[+] Successfully created '../afl-qemu-trace'.
[*] Testing the build...
[+] Instrumentation tests passed.
[+] All set, you can now use the -Q mode in afl-fuzz!
</code></pre><h4 id="-" style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 1.2em; margin: 1.3em 0px 1em; padding: 0px;">遇到的坑</h4><ol style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 1.2em 0px; padding-left: 2em;"><li style="box-sizing: border-box; margin: 0.5em 0px;">运行后会提示libtool等资源库没有安装,使用<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">sudo apt install</code>安装即可:<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">$ ./build_qemu_support.sh
=================================================
AFL binary-only instrumentation QEMU build script
=================================================
[*] Performing basic sanity checks...
[-] Error: 'libtool' not found, please install first.
$ apt-get install libtool-bin
</code></pre></li><li style="box-sizing: border-box; margin: 0.5em 0px;">安装一些软件包时,有时会出现找不到glib2的错误:<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">$ apt install glib2
Reading package lists... Done
Building dependency tree
Reading state information... Done
E: Unable to locate package glib2
</code></pre>查看<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">build_qemu_support.sh</code>相关代码,需要在<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">/usr/include/glib-2.0/</code>或者<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">/usr/local/include/glib-2.0/</code>有相关库:<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">if [ ! -d "/usr/include/glib-2.0/" -a ! -d "/usr/local/include/glib-2.0/" ]; then
echo "[-] Error: devel version of 'glib2' not found, please install first."
exit 1
</code></pre>可通过安装以下工具来解决:<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">sudo apt-get install libgtk2.0-dev
</code></pre></li><li style="box-sizing: border-box; margin: 0.5em 0px;">qemu编译错误:<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">util/memfd.c:40:12: error: static declaration of 'memfd_create' follows non-static declaration
static int memfd_create(const char *name, unsigned int flags)
^~~~~~~~~~~~
In file included from /usr/include/x86_64-linux-gnu/bits/mman-linux.h:115,
from /usr/include/x86_64-linux-gnu/bits/mman.h:45,
from /usr/include/x86_64-linux-gnu/sys/mman.h:41,
from /root/afl-2.52b/qemu_mode/qemu-2.10.0/include/sysemu/os-posix.h:29,
from /root/afl-2.52b/qemu_mode/qemu-2.10.0/include/qemu/osdep.h:104,
from util/memfd.c:28:
</code></pre>afl默认qemu版本太老,官方已经<a href="https://git.qemu.org/?p=qemu.git;a=commit;h=75e5b70e6b5dcc4f2219992d7cffa462aa406af0" style="background: transparent; box-sizing: border-box; color: lightseagreen; text-decoration-line: none;">patch</a>:<br style="box-sizing: border-box;" /><a href="https://git.qemu.org/?p=qemu.git;a=blobdiff;f=configure;h=99ccc1725ace3dd1e8be3e3b74c8ebd3fbd1c1eb;hp=9c8aa5a98bd4f7baf54dd7d75344be7487155036;hb=75e5b70e6b5dcc4f2219992d7cffa462aa406af0;hpb=200780a3a3ed067dfb2e0d2210b0ed09e748ba26" style="background: transparent; box-sizing: border-box; color: lightseagreen; text-decoration-line: none;">./configure</a>:<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">@@ -3923,7 +3923,7 @@ fi
# check if memfd is supported
memfd=no
cat > $TMPC << EOF
-#include <sys/memfd.h>
+#include <sys/mman.h>
</code></pre><a href="https://git.qemu.org/?p=qemu.git;a=blobdiff;f=util/memfd.c;h=412e94a405fc97110c4f4ce2508a04d1a5ad5ab0;hp=4571d1aba866a67de41721aa17e4f54e0df695ef;hb=75e5b70e6b5dcc4f2219992d7cffa462aa406af0;hpb=200780a3a3ed067dfb2e0d2210b0ed09e748ba26" style="background: transparent; box-sizing: border-box; color: lightseagreen; text-decoration-line: none;">./util/memfd.c</a>:<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">@@ -31,9 +31,7 @@
#include "qemu/memfd.h"
-#ifdef CONFIG_MEMFD
-#include <sys/memfd.h>
-#elif defined CONFIG_LINUX
+#if defined CONFIG_LINUX && !defined CONFIG_MEMFD
</code></pre>修改完成后使用如下指令重打包,再修改<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">build_qemu_support.sh</code>里的<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">QEMU_SHA384</code>重新编译即可,<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">SHA384</code>值可以使用<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">sha384sum</code>获取:<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">$ tar -Jcf qemu-2.10.0.tar.xz qemu-2.10.0/
$ sha384sum qemu-2.10.0.tar.xz
</code></pre></li></ol><h4 id="-qemu-" style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 1.2em; margin: 1.3em 0px 1em; padding: 0px;">更换qemu版本</h4><div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;">如果想使用更新版本qemu,可以直接将<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">build_qemu_support.sh</code>设置的版本换成<a href="https://www.qemu.org/download/#source" style="background: transparent; box-sizing: border-box; color: lightseagreen; text-decoration-line: none;">官方的较新版本</a>,但更换版本后问题较多:</div><pre style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">#VERSION="2.10.0"
VERSION="2.12.1"
#QEMU_SHA384="68216c935487bc8c0596ac309e1e3ee75c2c4ce898aab796faa321db5740609ced365fedda025678d0"
QEMU_SHA384="92957551a3a21b1ed48dc70d9dd91905859a5565ec98492ed709a3b64daf7c5a0265d670030ee7e6d16da96436795435"
</code></pre><ol style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 1.2em 0px; padding-left: 2em;"><li style="box-sizing: border-box; margin: 0.5em 0px;">patch错误:<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">patching file linux-user/elfload.c
Hunk #2 succeeded at 2233 (offset 146 lines).
Hunk #3 succeeded at 2268 (offset 146 lines).
patching file accel/tcg/cpu-exec.c
Hunk #1 succeeded at 37 (offset 1 line).
Hunk #2 succeeded at 147 with fuzz 2 (offset 1 line).
Hunk #3 FAILED at 369.
1 out of 3 hunks FAILED -- saving rejects to file accel/tcg/cpu-exec.c.rej
</code></pre>patch针对的是上层路径的文件更新,可以直接注释掉<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">#patch -p1 <../patches/cpu-exec.diff || exit 1
</code></pre></li><li style="box-sizing: border-box; margin: 0.5em 0px;">缺少pixman,安装即可<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">apt-get install libpixman*
</code></pre></li><li style="box-sizing: border-box; margin: 0.5em 0px;">LINK错误:<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">LINK x86_64-linux-user/qemu-x86_64
linux-user/syscall.o: In function `do_syscall':
/root/afl-2.52b/qemu_mode/qemu-2.12.0/linux-user/syscall.c:11983: undefined reference to `afl_forksrv_pid'
linux-user/elfload.o: In function `load_elf_image':
/root/afl-2.52b/qemu_mode/qemu-2.12.0/linux-user/elfload.c:2236: undefined reference to `afl_entry_point'
/root/afl-2.52b/qemu_mode/qemu-2.12.0/linux-user/elfload.c:2236: undefined reference to `afl_entry_point'
/root/afl-2.52b/qemu_mode/qemu-2.12.0/linux-user/elfload.c:2271: undefined reference to `afl_start_code'
/root/afl-2.52b/qemu_mode/qemu-2.12.0/linux-user/elfload.c:2271: undefined reference to `afl_start_code'
/root/afl-2.52b/qemu_mode/qemu-2.12.0/linux-user/elfload.c:2275: undefined reference to `afl_end_code'
/root/afl-2.52b/qemu_mode/qemu-2.12.0/linux-user/elfload.c:2275: undefined reference to `afl_end_code'
/root/afl-2.52b/qemu_mode/qemu-2.12.0/linux-user/elfload.c:2236: undefined reference to `afl_entry_point'
/root/afl-2.52b/qemu_mode/qemu-2.12.0/linux-user/elfload.c:2236: undefined reference to `afl_entry_point'
/root/afl-2.52b/qemu_mode/qemu-2.12.0/linux-user/elfload.c:2271: undefined reference to `afl_start_code'
/root/afl-2.52b/qemu_mode/qemu-2.12.0/linux-user/elfload.c:2271: undefined reference to `afl_start_code'
/root/afl-2.52b/qemu_mode/qemu-2.12.0/linux-user/elfload.c:2275: undefined reference to `afl_end_code'
/root/afl-2.52b/qemu_mode/qemu-2.12.0/linux-user/elfload.c:2275: undefined reference to `afl_end_code'
collect2: error: ld returned 1 exit status
Makefile:193: recipe for target 'qemu-x86_64' failed
make[1]: *** [qemu-x86_64] Error 1
Makefile:478: recipe for target 'subdir-x86_64-linux-user' failed
make: *** [subdir-x86_64-linux-user] Error 2
</code></pre>上层patch中对源码文件做了修改,导致部分外部变量没有导入,注释掉相关patch即可:<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;"># patch -p1 <../patches/elfload.diff || exit 1
# patch -p1 <../patches/syscall.diff || exit 1
</code></pre></li><li style="box-sizing: border-box; margin: 0.5em 0px;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">afl-qemu-trace</code>测试失败<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">[+] Successfully created '../afl-qemu-trace'.
[*] Testing the build...
[-] Error: afl-qemu-trace instrumentation doesn't seem to work!
</code></pre>应该是用64位<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">afl-qemu-trace</code>工具测试32位程序引起的,忽略即可,或者通过如下指令指定32位架构:<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">$ CPU_TARGET=i386 ./build_qemu_support.sh
</code></pre>结果如下,实际也是忽略了测试:<pre style="box-sizing: border-box; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">[+] Successfully created '../afl-qemu-trace'.
[!] Note: can't test instrumentation when CPU_TARGET set.
[+] All set, you can now (hopefully) use the -Q mode in afl-fuzz!
</code></pre></li></ol><div data-unique="0x2使用afl-qemufuzz" name="0x2使用afl-qemufuzz" style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px;"></div><h1 id="0x2-afl-qemu-fuzz" style="-webkit-text-stroke-width: 0.3px; background-color: white; border-bottom: 1px solid rgb(221, 221, 221); box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 1.6em; margin: 1.3em 0px 1em; padding: 0px;">0x2 使用afl-qemu fuzz</h1><div data-unique="0x21同cpu架构程序" name="0x21同cpu架构程序" style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px;"></div><h2 id="0x21-cpu-" style="-webkit-text-stroke-width: 0.3px; background-color: white; border-bottom: 1px solid rgb(238, 238, 238); box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 1.4em; margin: 1.3em 0px 1em; padding: 0px;">0x21 同cpu架构程序</h2><div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;">以系统中<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">wget</code>指令为例,使用如下指令执行fuzz,<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">-Q</code>参数表示使用qemu模式;<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">-m</code>参数设置使用内存大小,不设置则默认200MB:</div><pre style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">$ afl-fuzz -i fuzz_in -o fuzz_out -m 200 -Q wget @@
</code></pre><div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;">运行成功界面如下(ubuntu for docker):<br style="box-sizing: border-box;" /><a href="https://user-images.githubusercontent.com/11291711/49939045-a062e800-ff16-11e8-9695-42f8721317a2.png" style="background: transparent; box-sizing: border-box; color: lightseagreen; text-decoration-line: none;"><img border="0" data-original-height="631" data-original-width="800" height="504" src="https://user-images.githubusercontent.com/11291711/49939045-a062e800-ff16-11e8-9695-42f8721317a2.png" style="border: 0px; box-sizing: border-box; display: inline-block; height: auto; max-width: 100%; vertical-align: middle;" width="640" /></a></div><div data-unique="0x22不同cpu架构程序" name="0x22不同cpu架构程序" style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px;"></div><h2 id="0x22-cpu-" style="-webkit-text-stroke-width: 0.3px; background-color: white; border-bottom: 1px solid rgb(238, 238, 238); box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 1.4em; margin: 1.3em 0px 1em; padding: 0px;">0x22 不同cpu架构程序</h2><div data-unique="0x221获取目标文件" name="0x221获取目标文件" style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px;"></div><h3 id="0x221-" style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 1.3em; margin: 1.3em 0px 1em; padding: 0px;">0x221 获取目标文件</h3><div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;">Android adbd程序为例,获取adbd文件:</div><pre style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">$ file /system/bin/adbd
/system/bin/adbd: ELF executable, 64-bit LSB arm64, static, for Android 28, BuildID=2ef781f7497eaad0b8ba145996afd9a1, not stripped
$ adb pull /system/bin/adbd ./
</code></pre><div data-unique="0x222编译目标架构qemu模式" name="0x222编译目标架构qemu模式" style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px;"></div><h3 id="0x222-qemu-" style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 1.3em; margin: 1.3em 0px 1em; padding: 0px;">0x222 编译目标架构qemu模式</h3><div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;">如果fuzz的程序与qemu架构不同,则可能出现如下错误,需要用之前方式指定正确架构进行编译qemu模式:</div><pre style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">$ afl-fuzz -i fuzz_in -o fuzz_out/ -Q ./adbd @@
...
[-] Hmm, looks like the target binary terminated before we could complete a
handshake with the injected code. There are two probable explanations:
- The current memory limit (200 MB) is too restrictive, causing an OOM
fault in the dynamic linker. This can be fixed with the -m option. A
simple way to confirm the diagnosis may be:
( ulimit -Sv $[199 << 10]; /path/to/fuzzed_app )
Tip: you can use http://jwilk.net/software/recidivm to quickly
estimate the required amount of virtual memory for the binary.
- Less likely, there is a horrible bug in the fuzzer. If other options
fail, poke <lcamtuf@coredump.cx> for troubleshooting tips.
[-] PROGRAM ABORT : Fork server handshake failed
Location : init_forkserver(), afl-fuzz.c:2253
</code></pre><div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;">编译arm64版本工具,qemu支持的架构类型见<code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: inline; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; padding: 0px 0.3em; white-space: pre-wrap;">./qemu-2.10.0/linux-user/host/</code>目录,其中arm为32位arm,aarch64为64位arm:</div><pre style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">$ ls ./qemu-2.10.0/linux-user/host/
aarch64 arm i386 ia64 mips ppc ppc64 s390 s390x sparc sparc64 x32 x86_64
</code></pre><div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;">以64位arm为例,编译指令如下:</div><pre style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">$ CPU_TARGET=aarch64 ./build_qemu_support.sh
</code></pre><div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;">编译aarch64版本后,继续执行fuzz:</div><pre style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">$ ../afl-2.52b/afl-fuzz -i fuzz_in/ -o fuzz_out/ -Q ./adbd
</code></pre><div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;">依然错误:</div><pre style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">[-] PROGRAM ABORT : Test case 'id:000000,orig:testcase' results in a crash
Location : perform_dry_run(), afl-fuzz.c:2852
</code></pre><div data-unique="0x223qemuusermode检查" name="0x223qemuusermode检查" style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px;"></div><h3 id="0x223-qemu-user-mode-" style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 1.3em; margin: 1.3em 0px 1em; padding: 0px;">0x223 qemu user mode检查</h3><div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;">由于可执行文件的架构不一样,所以需要按照QEMU user mode仿真做一下检查,运行成功后再进行fuzz,详情参考:<a href="https://www.gandalf.site/2018/12/iotqemuiot.html" style="background: transparent; box-sizing: border-box; color: lightseagreen; text-decoration-line: none;">IoT(七)通过qemu调试IoT固件和程序</a>里的用户模式调试程序。</div><div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;">在该文中,adbd程序由于缺少外部资源依然执行失败(如需对有外部资源依赖的程序进行fuzz,可在该平台编译对应版本的fuzz工具),故重新选取能够执行成功的静态编译工具,如Android上的三方工具busybox:</div><pre style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">$ file busybox
busybox: ELF 64-bit LSB executable, ARM aarch64, version 1 (SYSV), statically linked, stripped
$ qemu-aarch64 busybox
BusyBox v1.25.0-NetHunter (2016-03-19 19:36:31 EDT) multi-call binary.
BusyBox is copyrighted by many authors between 1998-2015.
Licensed under GPLv2. See source distribution for detailed
copyright notices.
Usage: busybox [function [arguments]...]
or: busybox --list[-full]
or: busybox --install [-s] [DIR]
or: function [arguments]...
....
</code></pre><div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;">此处可成功对busybox进行fuzz:</div><pre style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em; overflow: auto;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(234, 234, 234); box-sizing: border-box; display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0px 0.3em;">../afl-2.52b/afl-fuzz -i fuzz_in/ -o fuzz_out/ -Q ./busybox @@
</code></pre><div style="-webkit-text-stroke-width: 0.3px; background-color: white; box-sizing: border-box; color: #333333; font-family: "Roboto Slab", serif; font-size: 16px; margin: 0px 0px 1.2em !important;"><a href="https://user-images.githubusercontent.com/11291711/50451233-c3a58280-096d-11e9-807a-12353f51f10a.png" style="background: transparent; box-sizing: border-box; color: lightseagreen; text-decoration-line: none;"><img border="0" data-original-height="642" data-original-width="800" height="512" src="https://user-images.githubusercontent.com/11291711/50451233-c3a58280-096d-11e9-807a-12353f51f10a.png" style="border: 0px; box-sizing: border-box; display: inline-block; height: auto; max-width: 100%; vertical-align: middle;" width="640" /></a></div>drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-87632261194849549302020-04-16T02:21:00.003-07:002020-04-16T05:42:11.511-07:00利用 hexo 搭建github blog<div style="font-family: Arial, sans; font-size: 12px; margin-bottom: 1.2em !important;">
主要还是看 hexo 的 next 主题挺不错的,所以选择了用 hexo 搭建 github 的 blog。<br />使用 hexo 搭建 blog 的前置条件还是很多的:</div>
<pre style="font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(204, 204, 204); display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0.5em 0.7em;">1. brew install npm
2. npm install -g hexo-cli
3. npm install -g hexo
</code></pre>
<div style="font-family: Arial, sans; font-size: 12px; margin-bottom: 1.2em !important;">
如上,即已安装前置的 node.js 和 hexo。</div>
<div style="font-family: Arial, sans; font-size: 12px; margin-bottom: 1.2em !important;">
之后需要创建一个新文件夹(文件夹必须为空,否则无法 init hexo),目录下执行</div>
<pre style="font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(204, 204, 204); display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0.5em 0.7em;">1. hexo init
2. npm install
3. hexo g
4. hexo s
</code></pre>
<div style="font-family: Arial, sans; font-size: 12px; margin-bottom: 1.2em !important;">
即启动本地 blog 服务,输入 <a href="http://localhost:4000/">http://localhost:4000/</a> 即刻本地查看。</div>
<div style="font-family: Arial, sans; font-size: 12px; margin-bottom: 1.2em !important;">
此时需要同步到 github,在 github 进行部署。<br />这里需要编辑 _config.yml 以通过 hexo d 进行发布(单纯同步工程至 github 不可行)。</div>
<pre style="font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(204, 204, 204); display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0.5em 0.7em;">deploy:
type: git
repo: git@github.com:username/username.github.io.git
branch: master
</code></pre>
<div style="font-family: Arial, sans; font-size: 12px; margin-bottom: 1.2em !important;">
这时一般是没有 git 命令的(执行 hexo d 会报错),需要安装 hexo-deployer-git</div>
<pre style="font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(204, 204, 204); display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0.5em 0.7em;">npm install hexo-deployer-git
</code></pre>
<div style="font-family: Arial, sans; font-size: 12px; margin-bottom: 1.2em !important;">
此时,通过如下命令可进行发布</div>
<pre style="font-family: Consolas, Inconsolata, Courier, monospace; font-size: 1em; line-height: 1.2em; margin-bottom: 1.2em; margin-top: 1.2em;"><code style="background-color: #f8f8f8; border-radius: 3px; border: 1px solid rgb(204, 204, 204); display: block !important; font-family: Consolas, Inconsolata, Courier, monospace; font-size: 0.85em; margin: 0px 0.15em; overflow: auto; padding: 0.5em 0.7em;">1. hexo clean
2. hexo g
3. hexo d
</code></pre>
<br />
<div style="font-family: Arial, sans; font-size: 0em; height: 0px; margin: 0px; max-height: 0px; max-width: 0px; overflow: hidden; padding: 0px; width: 0px;" title="MDH:PHAgc3R5bGU9Im1hcmdpbjogMHB4OyBmb250LWZhbWlseTogJnF1b3Q7UGluZ0ZhbmcgVEMmcXVv
dDs7IGZvbnQtc2l6ZTogbWVkaXVtOyI+PGJyIGNsYXNzPSJBcHBsZS1pbnRlcmNoYW5nZS1uZXds
aW5lIj7kuLvopoHov5jmmK/nnIsgaGV4byDnmoQgbmV4dCDkuLvpopjmjLrkuI3plJnnmoTvvIzm
iYDku6XpgInmi6nkuobnlKggaGV4byDmkK3lu7ogZ2l0aHViIOeahCBibG9n44CCPC9wPjxwIHN0
eWxlPSJtYXJnaW46IDBweDsgZm9udC1mYW1pbHk6ICZxdW90O1BpbmdGYW5nIFRDJnF1b3Q7OyBm
b250LXNpemU6IG1lZGl1bTsiPuS9v+eUqCBoZXhvIOaQreW7uiBibG9nIOeahOWJjee9ruadoeS7
tui/mOaYr+W+iOWkmueahO+8mjwvcD48cCBzdHlsZT0ibWFyZ2luOiAwcHg7IGZvbnQtZmFtaWx5
OiAmcXVvdDtQaW5nRmFuZyBUQyZxdW90OzsgZm9udC1zaXplOiBtZWRpdW07Ij48YnI+PC9wPjxw
IHN0eWxlPSJtYXJnaW46IDBweDsgZm9udC1mYW1pbHk6ICZxdW90O1BpbmdGYW5nIFRDJnF1b3Q7
OyBmb250LXNpemU6IG1lZGl1bTsiPmBgYDwvcD48cCBzdHlsZT0ibWFyZ2luOiAwcHg7IGZvbnQt
ZmFtaWx5OiAmcXVvdDtQaW5nRmFuZyBUQyZxdW90OzsgZm9udC1zaXplOiBtZWRpdW07Ij4xLiBi
cmV3IGluc3RhbGwgbnBtPC9wPjxwIHN0eWxlPSJtYXJnaW46IDBweDsgZm9udC1mYW1pbHk6ICZx
dW90O1BpbmdGYW5nIFRDJnF1b3Q7OyBmb250LXNpemU6IG1lZGl1bTsiPjIuIG5wbSBpbnN0YWxs
IC1nIGhleG8tY2xpPC9wPjxwIHN0eWxlPSJtYXJnaW46IDBweDsgZm9udC1mYW1pbHk6ICZxdW90
O1BpbmdGYW5nIFRDJnF1b3Q7OyBmb250LXNpemU6IG1lZGl1bTsiPjMuIG5wbSBpbnN0YWxsIC1n
IGhleG88L3A+PHAgc3R5bGU9Im1hcmdpbjogMHB4OyBmb250LWZhbWlseTogJnF1b3Q7UGluZ0Zh
bmcgVEMmcXVvdDs7IGZvbnQtc2l6ZTogbWVkaXVtOyI+YGBgPC9wPjxwIHN0eWxlPSJtYXJnaW46
IDBweDsgZm9udC1mYW1pbHk6ICZxdW90O1BpbmdGYW5nIFRDJnF1b3Q7OyBmb250LXNpemU6IG1l
ZGl1bTsiPjxicj48L3A+PHAgc3R5bGU9Im1hcmdpbjogMHB4OyBmb250LWZhbWlseTogJnF1b3Q7
UGluZ0ZhbmcgVEMmcXVvdDs7IGZvbnQtc2l6ZTogbWVkaXVtOyI+5aaC5LiK77yM5Y2z5bey5a6J
6KOF5YmN572u55qEIG5vZGUuanMg5ZKMIGhleG/jgII8L3A+PHAgc3R5bGU9Im1hcmdpbjogMHB4
OyBmb250LWZhbWlseTogJnF1b3Q7UGluZ0ZhbmcgVEMmcXVvdDs7IGZvbnQtc2l6ZTogbWVkaXVt
OyI+PGJyPjwvcD48cCBzdHlsZT0ibWFyZ2luOiAwcHg7IGZvbnQtZmFtaWx5OiAmcXVvdDtQaW5n
RmFuZyBUQyZxdW90OzsgZm9udC1zaXplOiBtZWRpdW07Ij7kuYvlkI7pnIDopoHliJvlu7rkuIDk
uKrmlrDmlofku7blpLko5paH5Lu25aS55b+F6aG75Li656m677yM5ZCm5YiZ5peg5rOVIGluaXQg
aGV4bynvvIznm67lvZXkuIvmiafooYw8L3A+PHAgc3R5bGU9Im1hcmdpbjogMHB4OyBmb250LWZh
bWlseTogJnF1b3Q7UGluZ0ZhbmcgVEMmcXVvdDs7IGZvbnQtc2l6ZTogbWVkaXVtOyI+PGJyPjwv
cD48cCBzdHlsZT0ibWFyZ2luOiAwcHg7IGZvbnQtZmFtaWx5OiAmcXVvdDtQaW5nRmFuZyBUQyZx
dW90OzsgZm9udC1zaXplOiBtZWRpdW07Ij5gYGA8L3A+PHAgc3R5bGU9Im1hcmdpbjogMHB4OyBm
b250LWZhbWlseTogJnF1b3Q7UGluZ0ZhbmcgVEMmcXVvdDs7IGZvbnQtc2l6ZTogbWVkaXVtOyI+
MS4gaGV4byBpbml0PC9wPjxwIHN0eWxlPSJtYXJnaW46IDBweDsgZm9udC1mYW1pbHk6ICZxdW90
O1BpbmdGYW5nIFRDJnF1b3Q7OyBmb250LXNpemU6IG1lZGl1bTsiPjIuIG5wbSBpbnN0YWxsPC9w
PjxwIHN0eWxlPSJtYXJnaW46IDBweDsgZm9udC1mYW1pbHk6ICZxdW90O1BpbmdGYW5nIFRDJnF1
b3Q7OyBmb250LXNpemU6IG1lZGl1bTsiPjMuIGhleG8gZzwvcD48cCBzdHlsZT0ibWFyZ2luOiAw
cHg7IGZvbnQtZmFtaWx5OiAmcXVvdDtQaW5nRmFuZyBUQyZxdW90OzsgZm9udC1zaXplOiBtZWRp
dW07Ij40LiBoZXhvIHM8L3A+PHAgc3R5bGU9Im1hcmdpbjogMHB4OyBmb250LWZhbWlseTogJnF1
b3Q7UGluZ0ZhbmcgVEMmcXVvdDs7IGZvbnQtc2l6ZTogbWVkaXVtOyI+YGBgPC9wPjxwIHN0eWxl
PSJtYXJnaW46IDBweDsgZm9udC1mYW1pbHk6ICZxdW90O1BpbmdGYW5nIFRDJnF1b3Q7OyBmb250
LXNpemU6IG1lZGl1bTsiPjxicj48L3A+PHAgc3R5bGU9Im1hcmdpbjogMHB4OyBmb250LWZhbWls
eTogJnF1b3Q7UGluZ0ZhbmcgVEMmcXVvdDs7IGZvbnQtc2l6ZTogbWVkaXVtOyI+5Y2z5ZCv5Yqo
5pys5ZywIGJsb2cg5pyN5Yqh77yM6L6T5YWlIGh0dHA6Ly9sb2NhbGhvc3Q6NDAwMC8g5Y2z5Yi7
5pys5Zyw5p+l55yL44CCPC9wPjxwIHN0eWxlPSJtYXJnaW46IDBweDsgZm9udC1mYW1pbHk6ICZx
dW90O1BpbmdGYW5nIFRDJnF1b3Q7OyBmb250LXNpemU6IG1lZGl1bTsiPjxicj48L3A+PHAgc3R5
bGU9Im1hcmdpbjogMHB4OyBmb250LWZhbWlseTogJnF1b3Q7UGluZ0ZhbmcgVEMmcXVvdDs7IGZv
bnQtc2l6ZTogbWVkaXVtOyI+5q2k5pe26ZyA6KaB5ZCM5q2l5YiwIGdpdGh1Yu+8jOWcqCBnaXRo
dWIg6L+b6KGM6YOo572y44CCPC9wPjxwIHN0eWxlPSJtYXJnaW46IDBweDsgZm9udC1mYW1pbHk6
ICZxdW90O1BpbmdGYW5nIFRDJnF1b3Q7OyBmb250LXNpemU6IG1lZGl1bTsiPui/memHjOmcgOim
gee8lui+kSBfY29uZmlnLnltbCDku6XpgJrov4cgaGV4byBkIOi/m+ihjOWPkeW4gyjljZXnuq/l
kIzmraXlt6XnqIvoh7MgZ2l0aHViIOS4jeWPr+ihjCnjgII8L3A+PHAgc3R5bGU9Im1hcmdpbjog
MHB4OyBmb250LWZhbWlseTogJnF1b3Q7UGluZ0ZhbmcgVEMmcXVvdDs7IGZvbnQtc2l6ZTogbWVk
aXVtOyI+PGJyPjwvcD48cCBzdHlsZT0ibWFyZ2luOiAwcHg7IGZvbnQtZmFtaWx5OiAmcXVvdDtQ
aW5nRmFuZyBUQyZxdW90OzsgZm9udC1zaXplOiBtZWRpdW07Ij5gYGA8L3A+PHAgc3R5bGU9Im1h
cmdpbjogMHB4OyBmb250LWZhbWlseTogJnF1b3Q7UGluZ0ZhbmcgVEMmcXVvdDs7IGZvbnQtc2l6
ZTogbWVkaXVtOyI+ZGVwbG95OjwvcD48cCBzdHlsZT0ibWFyZ2luOiAwcHg7IGZvbnQtZmFtaWx5
OiAmcXVvdDtQaW5nRmFuZyBUQyZxdW90OzsgZm9udC1zaXplOiBtZWRpdW07Ij4mbmJzcDsgdHlw
ZTogZ2l0PC9wPjxwIHN0eWxlPSJtYXJnaW46IDBweDsgZm9udC1mYW1pbHk6ICZxdW90O1BpbmdG
YW5nIFRDJnF1b3Q7OyBmb250LXNpemU6IG1lZGl1bTsiPiZuYnNwOyByZXBvOiBnaXRAZ2l0aHVi
LmNvbTp1c2VybmFtZS91c2VybmFtZS5naXRodWIuaW8uZ2l0PC9wPjxwIHN0eWxlPSJtYXJnaW46
IDBweDsgZm9udC1mYW1pbHk6ICZxdW90O1BpbmdGYW5nIFRDJnF1b3Q7OyBmb250LXNpemU6IG1l
ZGl1bTsiPiZuYnNwOyBicmFuY2g6IG1hc3RlcjwvcD48cCBzdHlsZT0ibWFyZ2luOiAwcHg7IGZv
bnQtZmFtaWx5OiAmcXVvdDtQaW5nRmFuZyBUQyZxdW90OzsgZm9udC1zaXplOiBtZWRpdW07Ij5g
YGA8L3A+PHAgc3R5bGU9Im1hcmdpbjogMHB4OyBmb250LWZhbWlseTogJnF1b3Q7UGluZ0Zhbmcg
VEMmcXVvdDs7IGZvbnQtc2l6ZTogbWVkaXVtOyI+PGJyPjwvcD48cCBzdHlsZT0ibWFyZ2luOiAw
cHg7IGZvbnQtZmFtaWx5OiAmcXVvdDtQaW5nRmFuZyBUQyZxdW90OzsgZm9udC1zaXplOiBtZWRp
dW07Ij7ov5nml7bkuIDoiKzmmK/msqHmnIkgZ2l0IOWRveS7pOeahCjmiafooYwgaGV4byBkIOS8
muaKpemUmSnvvIzpnIDopoHlronoo4UgaGV4by1kZXBsb3llci1naXQ8L3A+PHAgc3R5bGU9Im1h
cmdpbjogMHB4OyBmb250LWZhbWlseTogJnF1b3Q7UGluZ0ZhbmcgVEMmcXVvdDs7IGZvbnQtc2l6
ZTogbWVkaXVtOyI+PGJyPjwvcD48cCBzdHlsZT0ibWFyZ2luOiAwcHg7IGZvbnQtZmFtaWx5OiAm
cXVvdDtQaW5nRmFuZyBUQyZxdW90OzsgZm9udC1zaXplOiBtZWRpdW07Ij5gYGA8L3A+PHAgc3R5
bGU9Im1hcmdpbjogMHB4OyBmb250LWZhbWlseTogJnF1b3Q7UGluZ0ZhbmcgVEMmcXVvdDs7IGZv
bnQtc2l6ZTogbWVkaXVtOyI+bnBtIGluc3RhbGwgaGV4by1kZXBsb3llci1naXQ8L3A+PHAgc3R5
bGU9Im1hcmdpbjogMHB4OyBmb250LWZhbWlseTogJnF1b3Q7UGluZ0ZhbmcgVEMmcXVvdDs7IGZv
bnQtc2l6ZTogbWVkaXVtOyI+YGBgPC9wPjxwIHN0eWxlPSJtYXJnaW46IDBweDsgZm9udC1mYW1p
bHk6ICZxdW90O1BpbmdGYW5nIFRDJnF1b3Q7OyBmb250LXNpemU6IG1lZGl1bTsiPjxicj48L3A+
PHAgc3R5bGU9Im1hcmdpbjogMHB4OyBmb250LWZhbWlseTogJnF1b3Q7UGluZ0ZhbmcgVEMmcXVv
dDs7IGZvbnQtc2l6ZTogbWVkaXVtOyI+5q2k5pe277yM6YCa6L+H5aaC5LiL5ZG95Luk5Y+v6L+b
6KGM5Y+R5biDPC9wPjxwIHN0eWxlPSJtYXJnaW46IDBweDsgZm9udC1mYW1pbHk6ICZxdW90O1Bp
bmdGYW5nIFRDJnF1b3Q7OyBmb250LXNpemU6IG1lZGl1bTsiPjxicj48L3A+PHAgc3R5bGU9Im1h
cmdpbjogMHB4OyBmb250LWZhbWlseTogJnF1b3Q7UGluZ0ZhbmcgVEMmcXVvdDs7IGZvbnQtc2l6
ZTogbWVkaXVtOyI+YGBgPC9wPjxwIHN0eWxlPSJtYXJnaW46IDBweDsgZm9udC1mYW1pbHk6ICZx
dW90O1BpbmdGYW5nIFRDJnF1b3Q7OyBmb250LXNpemU6IG1lZGl1bTsiPjEuIGhleG8gY2xlYW48
L3A+PHAgc3R5bGU9Im1hcmdpbjogMHB4OyBmb250LWZhbWlseTogJnF1b3Q7UGluZ0ZhbmcgVEMm
cXVvdDs7IGZvbnQtc2l6ZTogbWVkaXVtOyI+Mi4gaGV4byBnPC9wPjxwIHN0eWxlPSJtYXJnaW46
IDBweDsgZm9udC1mYW1pbHk6ICZxdW90O1BpbmdGYW5nIFRDJnF1b3Q7OyBmb250LXNpemU6IG1l
ZGl1bTsiPjMuIGhleG8gZDwvcD48cCBzdHlsZT0ibWFyZ2luOiAwcHg7IGZvbnQtZmFtaWx5OiAm
cXVvdDtQaW5nRmFuZyBUQyZxdW90OzsgZm9udC1zaXplOiBtZWRpdW07Ij5gYGA8L3A+PHAgc3R5
bGU9Im1hcmdpbjogMHB4OyBmb250LWZhbWlseTogJnF1b3Q7UGluZ0ZhbmcgVEMmcXVvdDs7IGZv
bnQtc2l6ZTogbWVkaXVtOyI+PGJyPjwvcD48cCBzdHlsZT0ibWFyZ2luOiAwcHg7IGZvbnQtZmFt
aWx5OiAmcXVvdDtQaW5nRmFuZyBUQyZxdW90OzsgZm9udC1zaXplOiBtZWRpdW07Ij7orr/pl64g
dXNlcm5hbWUuZ2l0aHViLmlvIOWNs+WPr+iuv+mXruiHquW3seeahCBibG9n44CCPC9wPgo=">
</div>
<br />
<div style="-webkit-text-stroke-width: 0px; color: black; font-family: Arial, sans; font-size: 12px; font-style: normal; font-variant-caps: normal; font-variant-ligatures: normal; font-weight: 400; letter-spacing: normal; margin: 0px 0px 1.2em !important; orphans: 2; text-align: start; text-decoration-color: initial; text-decoration-style: initial; text-indent: 0px; text-transform: none; white-space: normal; widows: 2; word-spacing: 0px;">
访问 username.github.io 即可访问自己的 blog。</div>
drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-91691023204386819312020-04-08T19:39:00.003-07:002021-04-20T00:39:23.020-07:00安全周事记(20200408)<pre class="markdown"/>
- 4.1 [AFL源码阅读笔记](https://www.anquanke.com/post/id/201760)
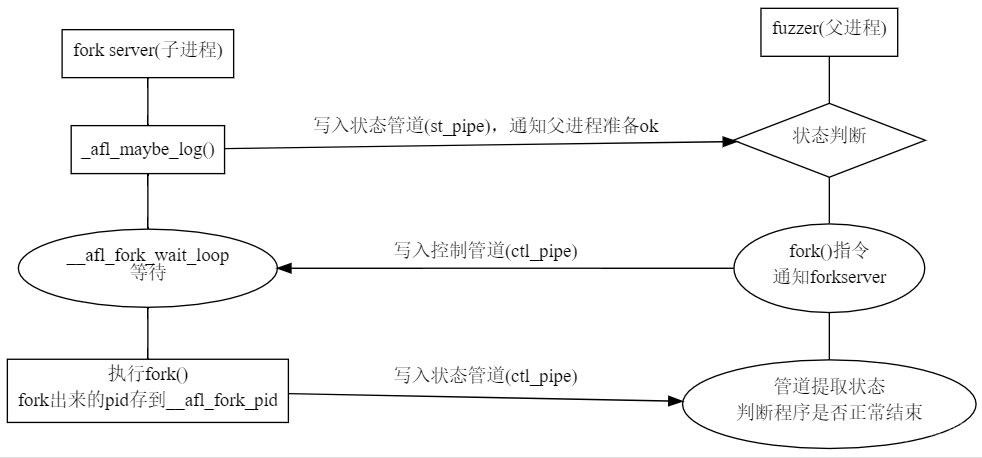
- 4.1 [TrickBot木马将获取交易身份验证码的应用推向德国银行客户](https://www.anquanke.com/post/id/202123)
国外研究员CERT-Bund的推文表示当用户的台式机上感染了TrickBot木马时,TrickBot会询问用户移动设备操作系统(OS)的类型和电话号码。然后提示用户安装假冒的安全应用程序进一步感染受害者的移动设备。
在应对德国的银行停止使用基于SMS的身份验证,转而使用专用于2FA方案的pushTAN应用程序(使用针对用户的推送通知,其中包含交易明细和交易身份验证号码)情况时。由于Android的应用程序沙箱阻止一个应用程序访问其他应用程序的数据。专为德国银行量身定制的较新版本恶意程序使用了以下两种方式获取交易身份验证号码(TAN)。
- 使用Android MediaRecorder类捕获屏幕视频或截屏。
- 使用可访问性服务遍历每个可访问性节点所包含的文本数据,其中包含屏幕上所有对象的文本数据如文本框里的文字。
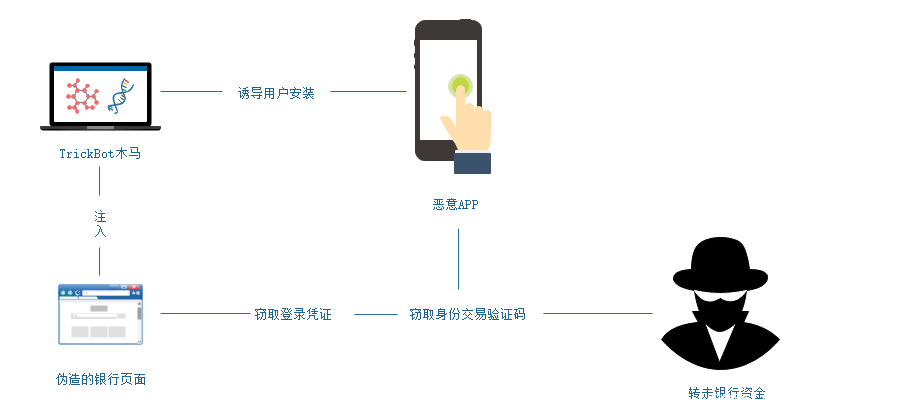
- 4.1 [NetSupport Manager RAT钓鱼攻击分析](https://www.freebuf.com/articles/network/228898.html)
2020年1月安全人员发现了一个伪造为受密码保护的恶意Microsoft Word文档,该文档在网络钓鱼活动中用于传播商业化远程访问工具(NetSupport Manager),此RAT通常用于管理员远程访问客户端计算机。但是攻击者将此RAT安装到受害者的系统上,从而获得访问权限。攻击活动中使用多种技术来规避动态和静态分析,并利用PowerShell PowerSploit来执行恶意文件安装。至少从2018年起NetSupport Manager RAT就已经出现在网络钓鱼活动中。
- 4.1 [远控免杀专题(5)-Veil免杀(VT免杀率23/71)](https://www.secpulse.com/archives/127186.html)
文章打包下载及相关软件下载:https://github.com/TideSec/BypassAntiVirus
- 4.1 [Rocke Group团伙新挖矿变种AliyunMiner分析](https://www.secpulse.com/archives/127162.html)
深信服安全团队捕获到Rocke Group黑产团伙运营的新挖矿病毒,该病毒通过ssh爆破、ssh免密登录、redis未授权访问漏洞以及redis弱密码爆破、jenkins远程代码执行漏洞以及jenkins弱口令爆破和ActiveMQ远程代码执行漏洞进行传播的挖矿病毒。深信服安全团队对该挖矿木马进行了详细的技术分析,并根据其传播域名特征将其命名为AliyunMiner。

***考虑过阿里的感受么?***
- 4.1 [针对香港用户的LightSpy水坑攻击](https://blog.trendmicro.com/trendlabs-security-intelligence/operation-poisoned-news-hong-kong-users-targeted-with-mobile-malware-via-local-news-links/)
趋势科技的安全研究人员发现了一个针对iOS用户的水坑攻击。其URL指向一个恶意网站,该网站具有指向不同站点的三个iframe,其中一个指向托管iOS漏洞利用主要脚本的网站,用户访问后会加载并运行恶意软件。
这些攻击利用了影响iOS 12.1和12.2设备的安全漏洞,以整个网站的用户为目标。通过支持外壳命令和文件操作,恶意软件使攻击者可以监视用户并完全控制受感染的设备。本质上是模块化的lightSpy允许对连接的WiFi历史记录、联系人、GPS位置、硬件信、iOS钥匙串、电话历史记录、Safari和Chrome浏览器历史记录、SMS消息以及本地网络IP地址进行过滤。

- 4.1 [为什么安全类AI模型准确性普遍虚高](https://www.anquanke.com/post/id/201282)
AI似乎成了目的而不是方法。
- “准确率”不准确
- 混淆“验证集”和“测试集”
- “误报”的放大
- 训练集的局限性
- 特征数量水分大
- 4.1 [干货 | Windows取证分析基础知识大全,赶快收藏!](https://www.secpulse.com/archives/127088.html)

- 4.1 [Zoom 客户端爆出安全漏洞 可向攻击者泄露 Windows 登陆凭据](http://hackernews.cc/archives/29841)
Windows 版 Zoom 客户端爆出了容易受到 NUC 路径注入攻击的安全漏洞。作为一款音视频会议应用,Zoom 还允许用户在聊天界面通过发送文本消息来互相交流。
Windows 网络 UNC 路径,也转换成了聊天消息中可单击的链接。若用户单击 UNC 路径链接,则 Windows 将尝试使用 SMB 文件共享协议连接到远程站点,默认情况下,Windows 将发送用户的登录名和 NTLM 密码哈希值,但稍有经验的攻击者均可借助 Hashcat 之类的免费工具来逆向运算。
- 4.2 [基于稀疏表示的物联网边缘僵尸网络攻击检测](https://www.anquanke.com/post/id/200877)
[原文网址](https://www.researchgate.net/publication/333567033_Botnet_Attack_Detection_at_the_IoT_Edge_Based_on_Sparse_Representation)
基于稀疏表示框架(sparsity representation)的物联网僵尸网络攻击检测方法,该方法使用重建错误阈值规则识别来自受感染的物联网设备的边缘恶意网络流量。僵尸网络攻击检测是基于小型良性IoT网络流量数据执行的,因此没有关于恶意IoT流量数据的先验知识。在基于物联网的真实网络数据集上展示了结果,并展示了提出的技术针对基于重构错误的自动编码器方法的有效性。
- 4.2 [警惕:Vollgar僵尸网络每天成功感染近3000台MSSQL服务器](https://www.freebuf.com/news/232295.html)
网络安全研究人员发现了一个名为Vollgar的加密挖矿僵尸网络,该僵尸网络至少自2018年以来一直在劫持MSSQL服务器,通过发起暴力攻击以接管服务器并安装Monero 和Vollar恶意挖矿软件。
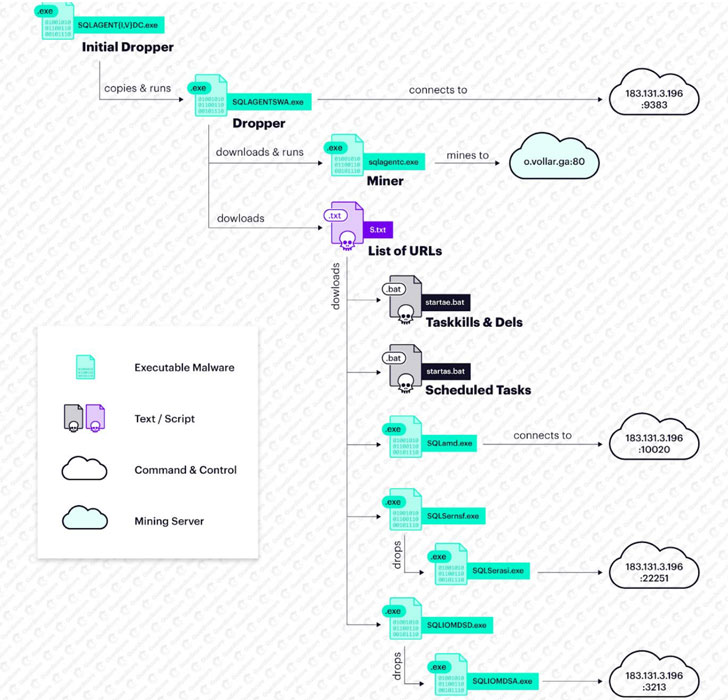
- 4.3 [一种工控蜜罐识别与反识别技术研究与应用实践](https://www.freebuf.com/articles/ics-articles/230402.html)
工控蜜罐通常指非真实工控设备,通常指应用服务、仿真程序等,比如服务蜜罐包括conpot、openplc、CryPLH2、仿真程序包括modbus tester、Mod Rssim、snap7、opendnp3、qtester104、DNP3_testhaness、EtherNetIP Virtual等。

- 4.3 [浅谈威胁情报应用场景](https://www.anquanke.com/post/id/202426)
威胁情报有以下几个常见的应用场景:
- 攻击检测与防御
- 攻击团伙追踪
- 威胁狩猎
- 事件监测与响应
- 基于情报驱动的漏洞管理
- 暗网情报发现
- 4.3 [Syborg:一款带有断路躲避系统的DNS子域名递归枚举工具](https://www.freebuf.com/sectool/227851.html)
[项目地址](https://github.com/MilindPurswani/Syborg)
- 4.3 [云视频会议软件Zoom连环漏洞陷信任危机](https://www.anquanke.com/post/id/202436)
- Zoom客户端聊天模块曝“惊天漏洞“ 可暴力破解目标用户Windows登录凭据
- Zoom安装包或将成为恶意代码发源地
Zoom使用的是捆绑了7zip手动解压缩应用程序的预安装脚本。如果当前用户在admin组中,不需要root,即可则将其直接安装到/ Applications。
- 4.4 [挖洞经验分享:关于IDOR的几个奇怪案例分析](https://www.freebuf.com/vuls/228918.html)
后端文件仍然是以“bookingId.pdf”的形式存储的,并且有一个中间件来负责将hdnBookingId解密为bookingId,或者说同时存储了一个订单的两种文件名称/格式,即同时存在“hdnBookingId.pdf”和“bookingId.pdf”。
- 4.4 [Android Cerberus恶意样本分析](https://www.freebuf.com/articles/terminal/230628.html)
Cerberus 恶意木马通过字符串混淆、执行流混淆、动态加载代码、动态解密字符串和实现了一个简单的计步器机制来对抗安全人员的分析工作。同时利用了 Android 无障碍服务的屏幕监控功能,通过监控手机屏幕内容的改变事件,模拟点击危险权限授权按钮进行自我授权、监控用户的安全扫描和卸载行为进行自我保护以及监控前台应用活动界面完成对目标的劫持攻击。
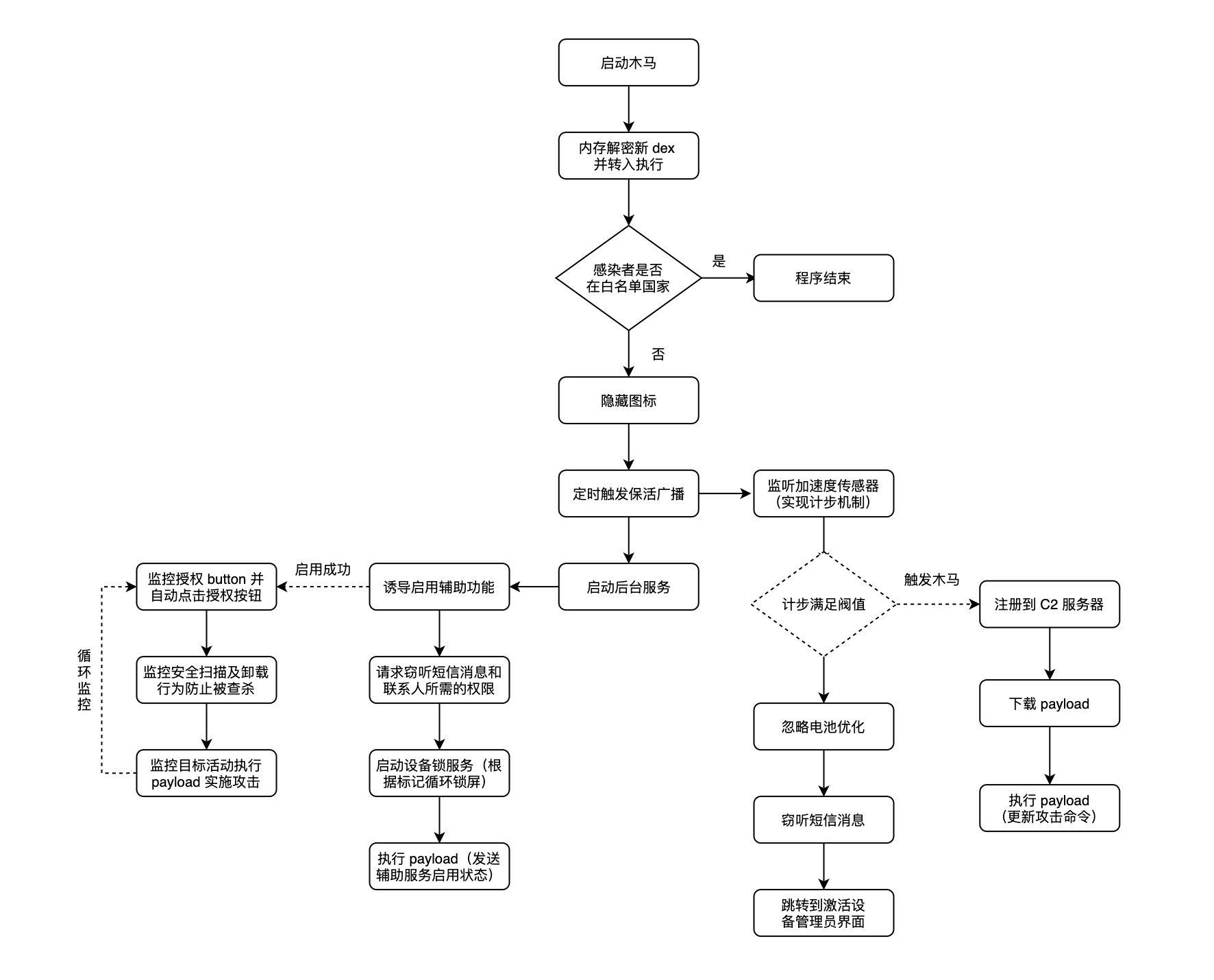
- 4.4 [12k+ Android apps contain master passwords, secret access keys, secret commands](https://www.zdnet.com/article/12k-android-apps-contain-master-passwords-secret-access-keys-secret-commands/)

- 4.5 [PrivescCheck:一款针对Windows系统的提权枚举脚本](https://www.freebuf.com/articles/system/229405.html)
[GitHub传送门](https://github.com/itm4n/PrivescCheck)
- 4.5 [利用COVID-19发起的网络攻击分析](https://www.freebuf.com/articles/network/230475.html)
Check Point发现了针对蒙古公共部门的网络攻击活动,该组织利用了冠状病毒恐慌情绪向目标发送恶意软件。研究发现其与可与在2016年进行的其他网络活动联系起来。多年来,这些行动的目标是多个国家/地区的不同部门,例如乌克兰,俄罗斯, 和白俄罗斯。
- 4.6 [中国驻外机构正遭受攻击!深信服VPN设备成境外国家级黑客突破口](https://www.anquanke.com/post/id/202526)
360安全大脑捕获到一起劫持深信服VPN的安全服务从而下发恶意文件的APT攻击活动,我们已第一时间将漏洞细节报告给厂商并得到确认。
通过进一步追踪溯源发现,此次攻击者为来自半岛的APT组织Darkhotel(APT-C-06),今年3月开始已失陷的VPN服务器超200台, 中国多处驻外机构遭到攻击,4月初攻击态势又再向北京、上海相关政府机构蔓延。
更为紧要的是,根据监测分析发现,攻击者已控制了大量相关单位的VPN服务器并控制了大量相关单位的计算机终端设备。
- 4.6 [文件解压引发的Getshell](https://www.freebuf.com/articles/others-articles/229928.html)
- PHPOK CMS后台任意文件上传
- Jspxcms后台的zip解压功能目录穿越漏洞导致getshell
- 4.6 [黑客帝国?论美国Hacker的养成之路](https://www.freebuf.com/articles/neopoints/230985.html)
全面培养、发展黑客力量是美国黑客帝国的基底,联动民间/私营企业是中坚力量,那么国家体系的运作就是黑客帝国的顶层战略指挥区。
美国有着完整的一套网络黑客运转体系,植根于其网络安全战略之中。
- 完整架构体系
- 作战经验丰富
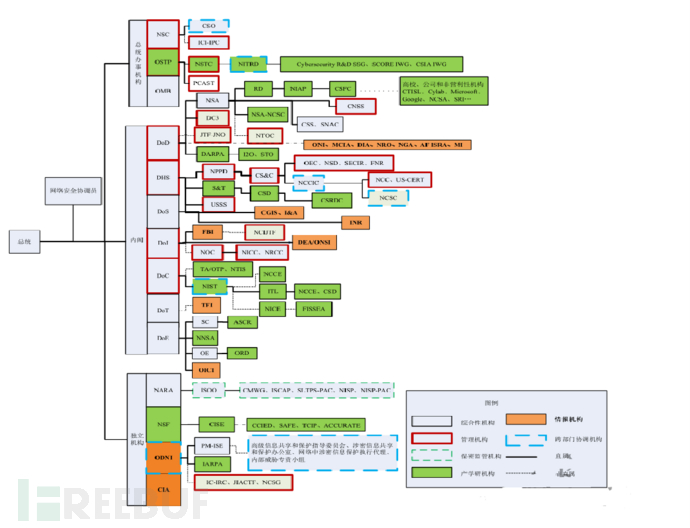
- 4.7 [Fuzzowski:一款功能强大的网络协议模糊测试工具](https://www.freebuf.com/sectool/227869.html)
该工具可以帮助研究人员对网络协议进行模糊测试,并且能够在整个测试过程中给我们提供帮助。除此之外,该工具还允许研究人员定义链接,并帮助识别服务的崩溃。
[GitHub传送门](https://github.com/nccgroup/fuzzowski)
- 4.7 [xHelper, the Unkillable Android malware that re-Installs after factory reset](https://securityaffairs.co/wordpress/101229/cyber-crime/xhelper-unkillable-android-malware.html)
- 4.8 [Clicker木马新家族:Haken木马](https://www.freebuf.com/articles/terminal/230524.html)
Haken木马通过将本机代码注入Facebook和Google广告SDK的库中来实现模拟用户点击广告功能。
- 4.8 [照弹不误:出站端口受限环境下反弹Shell的思考](https://www.freebuf.com/vuls/232544.html)
遇到能 ping 通外网但无法反弹的目标,得多个心眼考虑是否限制了出站端口.
- 4.8 [如何未经授权访问IOS和macOS上的摄像头](https://www.anquanke.com/post/id/202511)
原文地址:[Webcam Hacking-The story of how I gained unauthorized Camera access on iOS and macOS](https://www.anquanke.com/post/id/Webcam%20Hacking-The%20story%20of%20how%20I%20gained%20unauthorized%20Camera%20access%20on%20iOS%20and%20macOS)
1. 打开有害的HTTP网站;
2. HTTP网站变成一个data: URI;
3. 使用”空白“源将data: URI变成blob: URI;
4. 修改window.history(分两个步骤);
5. 创建一个包含about:blank的iframe,向其中执行document.write;
6. 为iframe动态添加sandbox标签;
7. 使用X-Frame-Options进行一次失败的框架导航;
8. 在iframe中执行window.open,打开一个弹窗,向其中执行document.write。
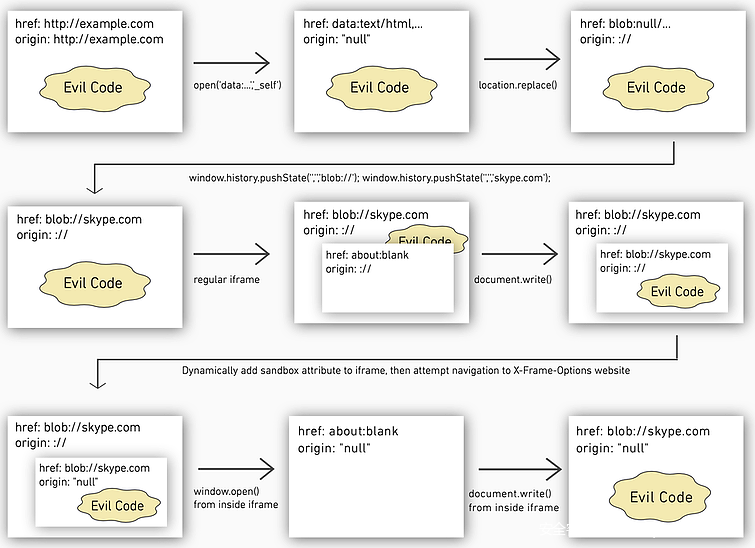
- 4.8 [针对某国际信息通信公司从前期探测到内网提权的一次成功漏洞测试](https://www.freebuf.com/vuls/230441.html)
- 4.8 [Molerats在多国政府和电信部门安装后门](https://www.freebuf.com/articles/network/230021.html)
Molerats早在2011年就已经开始攻击世界各地的政府组织,主要涉及非法访问和敏感数据收集。他们使用了大量的策略和技术,包括利用公开的后门工具,自我定制研发工具等。该组织主要利用社会工程学和鱼叉式钓鱼作为攻击切入手段,然后通过C2服务器下载恶意负载。该组织使用了多种技术手段使检测和分析变得更加困难,Spark C2通道利用3DES或AES加密HTTP POST请求和响应数据来逃避检测,并且随机生成的密钥对于每个有效载荷都是唯一的。
- 4.8 [DDG挖矿僵尸网络病毒最新变种分析](https://www.anquanke.com/post/id/202574)
- 4.8 [DDG的新征程——自研P2P协议构建混合P2P网络](https://blog.netlab.360.com/ddg-upgrade-to-new-p2p-hybrid-model/)
DDG Mining Botnet 是一个活跃已久的挖矿僵尸网络,其主要的盈利方式是挖 XMR。v5009 及以后的版本,则摒弃了以前基于 Memberlist 来构建 P2P 网络的方式,改用自研的 P2P 协议来构建混合模式 P2P 网络
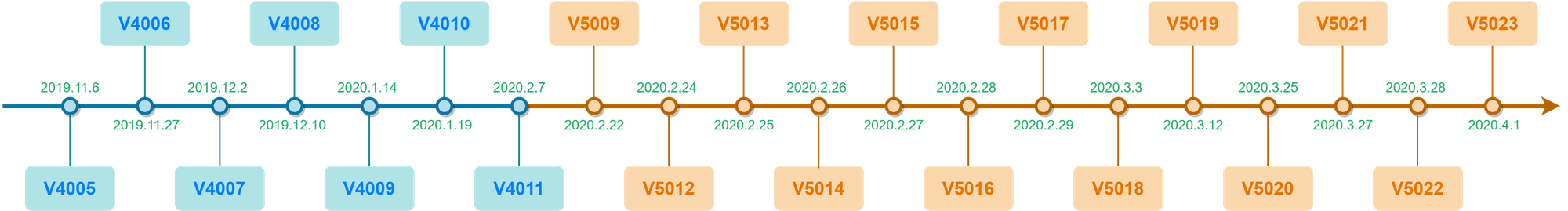
- 4.8 [安全专家在线破解!游戏账号买卖诈骗全过程](https://www.anquanke.com/post/id/202484)
不法分子伪装成买家,制作虚假图片骗取用户QQ;再冒充平台给用户发送邮件,用户访问邮件里的链接时,实际访问网址发生了跳转。
- 4.8 [暗网卖口罩,推特卖厕纸,疫情下的海外黑灰产](https://www.freebuf.com/articles/others-articles/232850.html)drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com1tag:blogger.com,1999:blog-1654671993539634666.post-34157920765435622752020-03-11T22:04:00.005-07:002021-05-13T05:43:37.342-07:00有效的xmind8 for mac 序列号<pre class='markdown'/>
1. 官网下载最新的安装包 XMind For Mac,断网安装(安装软件需在断网情况下进行!!!).
双击打开安装包xmind.dmg,直接拖动安装.

安装完成之后,打开 偏好设置-->常规-->启动,将如图所示的两个标签的对勾取消掉,然后点击确定,关闭软件.
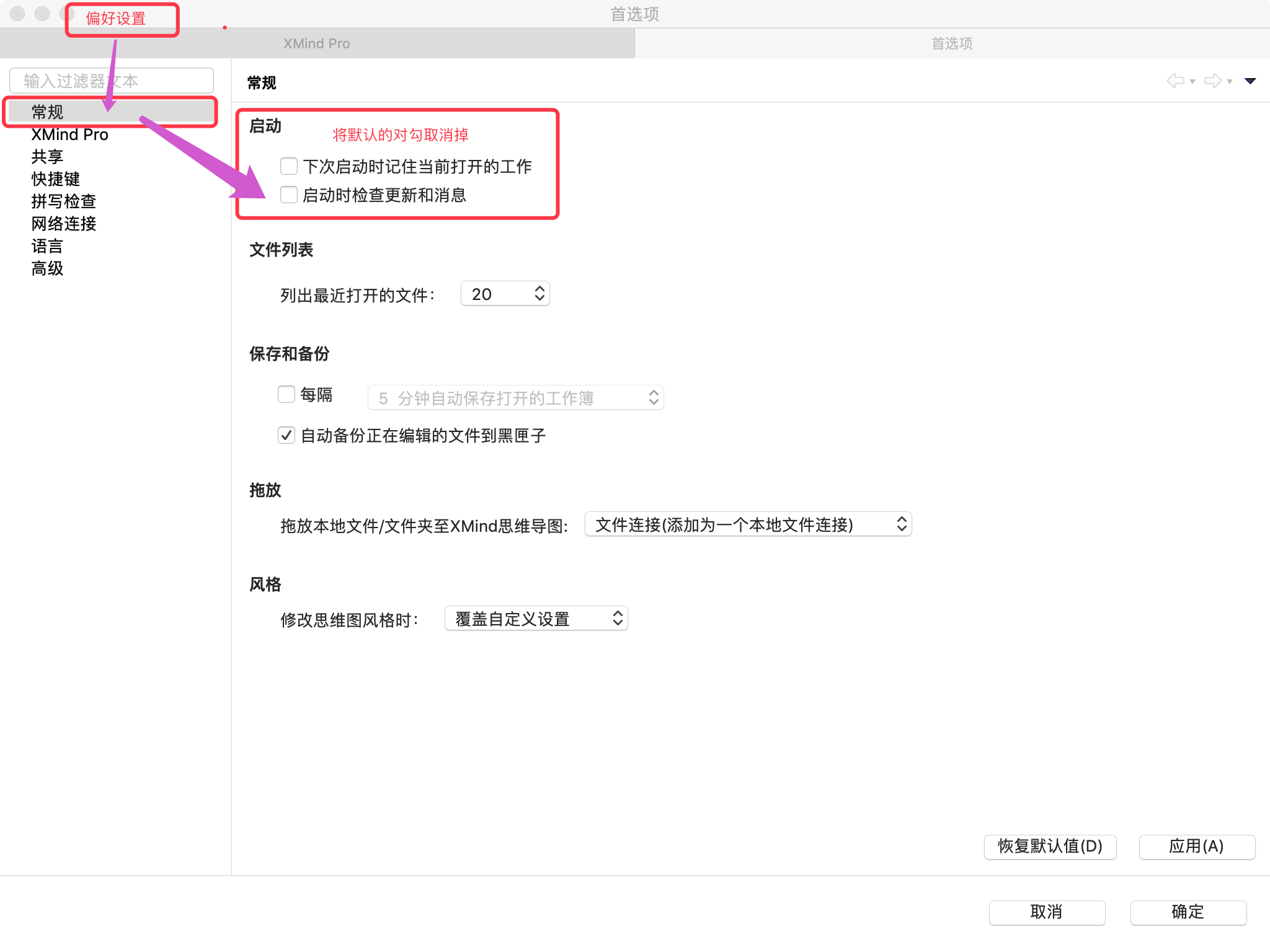
2. 下载破解包 XMindCrack.jar,链接: https://pan.baidu.com/s/1sCbCQHTI24CgyaVrwGW_kQ 提取码: dejw
3. 激活xmind:
a. 将下载的破解补丁复制到安装好的软件包下的Eclipse这个目录中:安装好的XMind-->鼠标右键显示包内容-->Contents-->Eclipse。
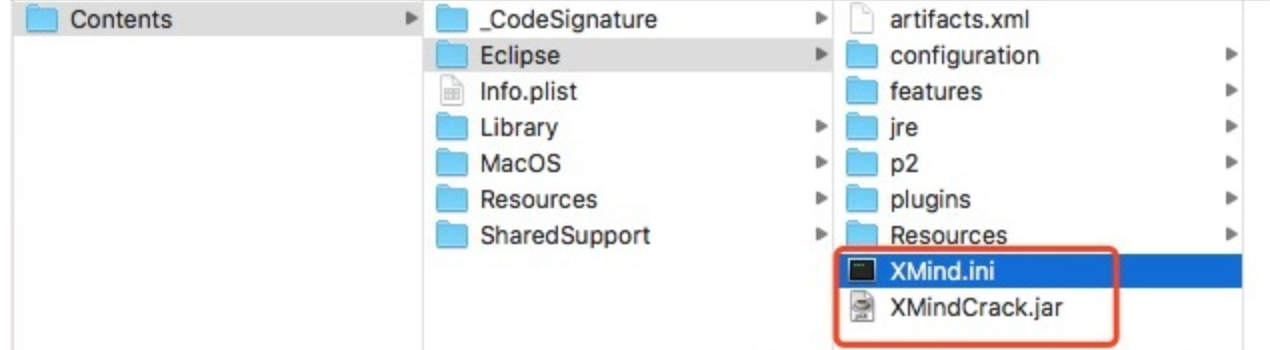
b. 打开安装目录Eclipse中的 XMind.ini (我下面使用的软件是Visual Studio Code,需要的自行Google吧)
c. 在 XMind.ini 最后追加一行XMindCrack.jar的绝对路径,并保存。(绝对路径如下可复制)
-javaagent:/Applications/XMind.app/Contents/Eclipse/XMindCrack.jar
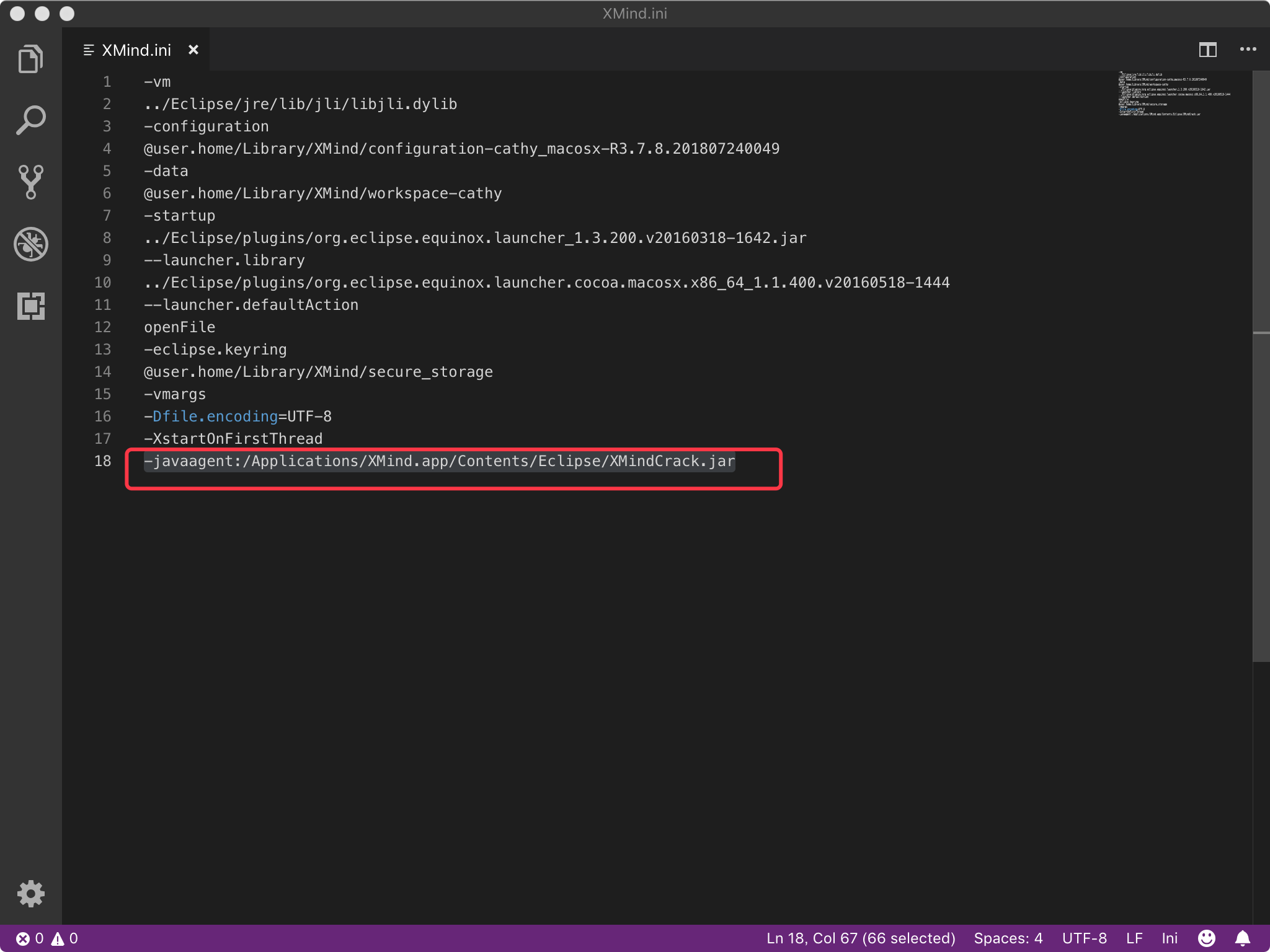
d. 重新打开 XMind, 点击 帮助-->序列号-->输入序列号,进入XMind激活页面,然后输入以下序列号 ,邮箱可以随便填,可以填自己的,提示激活成功之后点击'关闭'即可。
序列号:
>XAka34A2rVRYJ4XBIU35UZMUEEF64CMMIYZCK2FZZUQNODEKUHGJLFMSLIQMQUCUBXRENLK6NZL37JXP4PZXQFILMQ2RG5R7G4QNDO3PSOEUBOCDRYSSXZGRARV6MGA33TN2AMUBHEL4FXMWYTTJDEINJXUAV4BAYKBDCZQWVF3LWYXSDCXY546U3NBGOI3ZPAP2SO3CSQFNB7VVIY123456789012345drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-65031231491988132422020-01-17T19:29:00.001-08:002021-04-19T20:11:23.690-07:00安全周事记(20200117)<br />
<div class="markdown-here-wrapper" data-md-url="https://www.blogger.com/blogger.g?blogID=1654671993539634666#editor/target=post;postID=6503123149198813242;onPublishedMenu=allposts;onClosedMenu=allposts;postNum=3;src=postname">
<ul style="margin: 1.2em 0px; padding-left: 2em;">
<li style="margin: 0.5em 0px;">1.8 <a href="https://www.freebuf.com/articles/network/224520.html">针对WordPress的攻击调查</a></li>
<li style="margin: 0.5em 0px;">1.8 <a href="https://www.freebuf.com/articles/terminal/224707.html">Google Play恶意软件指向SideWinder组织</a></li>
<li style="margin: 0.5em 0px;">1.7 <a href="https://www.anquanke.com/post/id/196531">跳出单点思维,从上帝视角感知邮件安全态势</a></li>
<li style="margin: 0.5em 0px;">1.7 <a href="https://www.freebuf.com/articles/network/223383.html">致命APP,牟利7亿,10人殒命</a></li>
<li style="margin: 0.5em 0px;">1.10 <a href="https://www.freebuf.com/articles/network/224409.html">2019年网络攻击分析报告</a></li>
<li style="margin: 0.5em 0px;">1.10 <a href="https://www.anquanke.com/post/id/197004">TikTok安全性分析</a></li>
<li style="margin: 0.5em 0px;">1.10 <a href="https://www.freebuf.com/news/224982.html">MITRE发布首个针对工业控制系统(ICS)的ATT&CK知识库</a></li>
<li style="margin: 0.5em 0px;">1.9 <a href="https://www.anquanke.com/post/id/196979">2019年移动安全总结</a></li>
<li style="margin: 0.5em 0px;">1.13 <a href="https://www.freebuf.com/articles/terminal/223968.html">揭秘Agent Tesla间谍木马攻击活动</a></li>
<li style="margin: 0.5em 0px;">1.12 <a href="https://www.freebuf.com/articles/network/223654.html">APT32样本分析</a></li>
<li style="margin: 0.5em 0px;">1.12 <a href="https://www.freebuf.com/articles/system/223468.html">智能门铃背后的安全风险</a></li>
<li style="margin: 0.5em 0px;">1.11 <a href="https://www.freebuf.com/articles/terminal/223585.html">电诈团伙的千里眼:伪装成银监会移动端的恶意APP分析</a></li>
<li style="margin: 0.5em 0px;">1.11 <a href="https://www.freebuf.com/news/225062.html">Snake勒索软件正在威胁全球的企业网络</a></li>
<li style="margin: 0.5em 0px;">1.11 <a href="https://www.freebuf.com/articles/others-articles/224051.html">机器学习与恶意代码检测</a></li>
<li style="margin: 0.5em 0px;">1.13 <a href="http://hackernews.cc/archives/29262">美政府为低收入家庭提供手机被植入恶意程序 且无法清除</a></li>
<li style="margin: 0.5em 0px;">1.7 <a href="https://thehackernews.com/2020/01/android-zero-day-malware-apps.html">3 Google Play Store Apps Exploit Android Zero-Day Used by NSO Group</a></li>
<li style="margin: 0.5em 0px;">1.13 <a href="http://www.ijiandao.com/2b/baijia/345029.html">羊毛党跑去京东摸了年终奖</a></li>
<li style="margin: 0.5em 0px;">1.11 <a href="http://www.ijiandao.com/2b/baijia/344621.html">揭秘大数据时代秒级查询响应引擎的架构设计</a></li>
<li style="margin: 0.5em 0px;">1.11 <a href="http://www.ijiandao.com/2b/baijia/344581.html">阿里资深Leader:组建技术团队的一些思考</a></li>
<li style="margin: 0.5em 0px;">1.9 <a href="http://www.ijiandao.com/2b/baijia/344340.html">我花200块买了本弱智小说,据说能日入过万</a></li>
<li style="margin: 0.5em 0px;">1.14 <a href="https://www.freebuf.com/articles/web/224920.html">Tishna:一款功能强大的自动化Web应用渗透测试框架</a></li>
<li style="margin: 0.5em 0px;">1.14 <a href="https://www.secpulse.com/archives/121984.html">全勤矿工systemdMiner最新变种利用暗网代理下载恶意模块</a></li>
<li style="margin: 0.5em 0px;">1.14 <a href="https://securityaffairs.co/wordpress/96364/apt/china-linked-apt40-front-companies.html">China-linked APT40 group hides behind 13 front companies</a></li>
<li style="margin: 0.5em 0px;">1.15 <a href="https://www.freebuf.com/articles/network/225140.html">AppleJeus行动分析</a></li>
<li style="margin: 0.5em 0px;">1.15 <a href="https://www.anquanke.com/post/id/197266">“正版”监控软件被黑产利用,输出把关不严或成另一个TeamViewer?</a></li>
<li style="margin: 0.5em 0px;">1.16 <a href="https://www.freebuf.com/articles/neopoints/224824.html">对美国联邦存储图书馆网站被攻击挂黑页事件的简要技术分析</a></li>
<li style="margin: 0.5em 0px;">1.16 <a href="https://www.secpulse.com/archives/122090.html">“折纸”行动:针对南亚多国军政机构的网络攻击</a></li>
<li style="margin: 0.5em 0px;">1.16 <a href="https://www.sec-un.org/%e6%b4%8b%e8%91%b1%e5%bc%8f%e4%bf%a1%e6%81%af%e5%ae%89%e5%85%a8%e8%a7%82%e5%af%9f-%e5%b9%b8%e5%ad%98%e8%80%85%e5%81%8f%e5%b7%ae%e4%b8%8e%e5%a8%81%e8%83%81%e6%83%85%e6%8a%a5%e7%9a%84%e6%94%bb%e9%98%b2/">洋葱式信息安全观察-幸存者偏差与威胁情报的攻防演练应用</a></li>
<li style="margin: 0.5em 0px;">1.16 <a href="https://www.darknet.org.uk/2020/01/dsploit-apk-download-hacking-security-toolkit-for-android/?utm_source=feedly&utm_medium=webfeeds">dSploit APK Download – Hacking & Security Toolkit For Android</a></li>
<li style="margin: 0.5em 0px;">1.16 <a href="https://www.kaspersky.com.cn/blog/faketoken-trojan-sends-offensive-sms/10623/">发送攻击性短信的Faketoken木马</a></li>
<li style="margin: 0.5em 0px;">1.17 <a href="https://www.freebuf.com/articles/paper/225621.html">极验2019交互安全行业研究报告</a></li>
<li style="margin: 0.5em 0px;">1.16 <a href="http://www.ijiandao.com/2b/baijia/345990.html">不用AI搞仙人跳的黑产没有梦想</a></li>
</ul>
<div style="font-size: 0em; height: 0; margin: 0; max-height: 0; max-width: 0; overflow: hidden; padding: 0; width: 0;" title="MDH:PHA+LSAxLjggW+mSiOWvuVdvcmRQcmVzc+eahOaUu+WHu+iwg+afpV0oaHR0cHM6Ly93d3cuZnJl
ZWJ1Zi5jb20vYXJ0aWNsZXMvbmV0d29yay8yMjQ1MjAuaHRtbCk8L3A+PHA+LSAxLjggW0dvb2ds
ZSBQbGF55oG25oSP6L2v5Lu25oyH5ZCRU2lkZVdpbmRlcue7hOe7h10oaHR0cHM6Ly93d3cuZnJl
ZWJ1Zi5jb20vYXJ0aWNsZXMvdGVybWluYWwvMjI0NzA3Lmh0bWwpPC9wPjxwPi0gMS43IFvot7Pl
h7rljZXngrnmgJ3nu7TvvIzku47kuIrluJ3op4bop5LmhJ/nn6Xpgq7ku7blronlhajmgIHlir9d
KGh0dHBzOi8vd3d3LmFucXVhbmtlLmNvbS9wb3N0L2lkLzE5NjUzMSk8L3A+PHA+LSAxLjcgW+iH
tOWRvUFQUO+8jOeJn+WIqTfkur/vvIwxMOS6uuaukuWRvV0oaHR0cHM6Ly93d3cuZnJlZWJ1Zi5j
b20vYXJ0aWNsZXMvbmV0d29yay8yMjMzODMuaHRtbCk8L3A+PHA+LSAxLjEwIFsyMDE55bm0572R
57uc5pS75Ye75YiG5p6Q5oql5ZGKXShodHRwczovL3d3dy5mcmVlYnVmLmNvbS9hcnRpY2xlcy9u
ZXR3b3JrLzIyNDQwOS5odG1sKTwvcD48cD4tIDEuMTAgW1Rpa1Rva+WuieWFqOaAp+WIhuaekF0o
aHR0cHM6Ly93d3cuYW5xdWFua2UuY29tL3Bvc3QvaWQvMTk3MDA0KTwvcD48cD4tIDEuMTAgW01J
VFJF5Y+R5biD6aaW5Liq6ZKI5a+55bel5Lia5o6n5Yi257O757uf77yISUNT77yJ55qEQVRU77yG
Q0vnn6Xor4blupNdKGh0dHBzOi8vd3d3LmZyZWVidWYuY29tL25ld3MvMjI0OTgyLmh0bWwpPC9w
PjxwPi0gMS45IFsyMDE55bm056e75Yqo5a6J5YWo5oC757uTXShodHRwczovL3d3dy5hbnF1YW5r
ZS5jb20vcG9zdC9pZC8xOTY5NzkpPC9wPjxwPi0gMS4xMyBb5o+t56eYQWdlbnQgVGVzbGHpl7To
sI3mnKjpqazmlLvlh7vmtLvliqhdKGh0dHBzOi8vd3d3LmZyZWVidWYuY29tL2FydGljbGVzL3Rl
cm1pbmFsLzIyMzk2OC5odG1sKTwvcD48cD4tIDEuMTIgW0FQVDMy5qC35pys5YiG5p6QXShodHRw
czovL3d3dy5mcmVlYnVmLmNvbS9hcnRpY2xlcy9uZXR3b3JrLzIyMzY1NC5odG1sKTwvcD48cD4t
IDEuMTIgW+aZuuiDvemXqOmTg+iDjOWQjueahOWuieWFqOmjjumZqV0oaHR0cHM6Ly93d3cuZnJl
ZWJ1Zi5jb20vYXJ0aWNsZXMvc3lzdGVtLzIyMzQ2OC5odG1sKTwvcD48cD4tIDEuMTEgW+eUteiv
iOWbouS8meeahOWNg+mHjOecvO+8muS8quijheaIkOmTtuebkeS8muenu+WKqOerr+eahOaBtuaE
j0FQUOWIhuaekF0oaHR0cHM6Ly93d3cuZnJlZWJ1Zi5jb20vYXJ0aWNsZXMvdGVybWluYWwvMjIz
NTg1Lmh0bWwpPC9wPjxwPi0gMS4xMSBbU25ha2Xli5LntKLova/ku7bmraPlnKjlqIHog4Hlhajn
kIPnmoTkvIHkuJrnvZHnu5xdKGh0dHBzOi8vd3d3LmZyZWVidWYuY29tL25ld3MvMjI1MDYyLmh0
bWwpPC9wPjxwPi0gMS4xMSBb5py65Zmo5a2m5Lmg5LiO5oG25oSP5Luj56CB5qOA5rWLXShodHRw
czovL3d3dy5mcmVlYnVmLmNvbS9hcnRpY2xlcy9vdGhlcnMtYXJ0aWNsZXMvMjI0MDUxLmh0bWwp
PC9wPjxwPi0gMS4xMyBb576O5pS/5bqc5Li65L2O5pS25YWl5a625bqt5o+Q5L6b5omL5py66KKr
5qSN5YWl5oG25oSP56iL5bqPIOS4lOaXoOazlea4hemZpF0oaHR0cDovL2hhY2tlcm5ld3MuY2Mv
YXJjaGl2ZXMvMjkyNjIpPC9wPjxwPi0gMS43IFszIEdvb2dsZSBQbGF5IFN0b3JlIEFwcHMgRXhw
bG9pdCBBbmRyb2lkIFplcm8tRGF5IFVzZWQgYnkgTlNPIEdyb3VwXShodHRwczovL3RoZWhhY2tl
cm5ld3MuY29tLzIwMjAvMDEvYW5kcm9pZC16ZXJvLWRheS1tYWx3YXJlLWFwcHMuaHRtbCk8L3A+
PHA+LSAxLjEzIFvnvormr5vlhZrot5HljrvkuqzkuJzmkbjkuoblubTnu4jlpZZdKGh0dHA6Ly93
d3cuaWppYW5kYW8uY29tLzJiL2JhaWppYS8zNDUwMjkuaHRtbCk8L3A+PHA+LSAxLjExIFvmj63n
p5jlpKfmlbDmja7ml7bku6Pnp5Lnuqfmn6Xor6Llk43lupTlvJXmk47nmoTmnrbmnoTorr7orqFd
KGh0dHA6Ly93d3cuaWppYW5kYW8uY29tLzJiL2JhaWppYS8zNDQ2MjEuaHRtbCk8L3A+PHA+LSAx
LjExIFvpmL/ph4zotYTmt7FMZWFkZXLvvJrnu4Tlu7rmioDmnK/lm6LpmJ/nmoTkuIDkupvmgJ3o
gINdKGh0dHA6Ly93d3cuaWppYW5kYW8uY29tLzJiL2JhaWppYS8zNDQ1ODEuaHRtbCk8L3A+PHA+
LSAxLjkgW+aIkeiKsTIwMOWdl+S5sOS6huacrOW8seaZuuWwj+ivtO+8jOaNruivtOiDveaXpeWF
pei/h+S4h10oaHR0cDovL3d3dy5pamlhbmRhby5jb20vMmIvYmFpamlhLzM0NDM0MC5odG1sKTwv
cD48cD4tIDEuMTQgW1Rpc2huYe+8muS4gOasvuWKn+iDveW8uuWkp+eahOiHquWKqOWMlldlYuW6
lOeUqOa4l+mAj+a1i+ivleahhuaetl0oaHR0cHM6Ly93d3cuZnJlZWJ1Zi5jb20vYXJ0aWNsZXMv
d2ViLzIyNDkyMC5odG1sKTwvcD48cD4tIDEuMTQgW+WFqOWLpOefv+W3pXN5c3RlbWRNaW5lcuac
gOaWsOWPmOenjeWIqeeUqOaal+e9keS7o+eQhuS4i+i9veaBtuaEj+aooeWdl10oaHR0cHM6Ly93
d3cuc2VjcHVsc2UuY29tL2FyY2hpdmVzLzEyMTk4NC5odG1sKTwvcD48cD4tIDEuMTQgW0NoaW5h
LWxpbmtlZCBBUFQ0MCBncm91cCBoaWRlcyBiZWhpbmQgMTMgZnJvbnQgY29tcGFuaWVzXShodHRw
czovL3NlY3VyaXR5YWZmYWlycy5jby93b3JkcHJlc3MvOTYzNjQvYXB0L2NoaW5hLWxpbmtlZC1h
cHQ0MC1mcm9udC1jb21wYW5pZXMuaHRtbCk8L3A+PHA+LSAxLjE1IFtBcHBsZUpldXPooYzliqjl
iIbmnpBdKGh0dHBzOi8vd3d3LmZyZWVidWYuY29tL2FydGljbGVzL25ldHdvcmsvMjI1MTQwLmh0
bWwpPC9wPjxwPi0gMS4xNSBb4oCc5q2j54mI4oCd55uR5o6n6L2v5Lu26KKr6buR5Lqn5Yip55So
77yM6L6T5Ye65oqK5YWz5LiN5Lil5oiW5oiQ5Y+m5LiA5LiqVGVhbVZpZXdlcu+8n10oaHR0cHM6
Ly93d3cuYW5xdWFua2UuY29tL3Bvc3QvaWQvMTk3MjY2KTwvcD48cD4tIDEuMTYgW+Wvuee+juWb
veiBlOmCpuWtmOWCqOWbvuS5pummhue9keermeiiq+aUu+WHu+aMgum7kemhteS6i+S7tueahOeu
gOimgeaKgOacr+WIhuaekF0oaHR0cHM6Ly93d3cuZnJlZWJ1Zi5jb20vYXJ0aWNsZXMvbmVvcG9p
bnRzLzIyNDgyNC5odG1sKTwvcD48cD4tIDEuMTYgW+KAnOaKmOe6uOKAneihjOWKqO+8mumSiOWv
ueWNl+S6muWkmuWbveWGm+aUv+acuuaehOeahOe9kee7nOaUu+WHu10oaHR0cHM6Ly93d3cuc2Vj
cHVsc2UuY29tL2FyY2hpdmVzLzEyMjA5MC5odG1sKTwvcD48cD4tIDEuMTYgW+a0i+iRseW8j+S/
oeaBr+WuieWFqOinguWvny3lubjlrZjogIXlgY/lt67kuI7lqIHog4Hmg4XmiqXnmoTmlLvpmLLm
vJTnu4PlupTnlKhdKGh0dHBzOi8vd3d3LnNlYy11bi5vcmcvJWU2JWI0JThiJWU4JTkxJWIxJWU1
JWJjJThmJWU0JWJmJWExJWU2JTgxJWFmJWU1JWFlJTg5JWU1JTg1JWE4JWU4JWE3JTgyJWU1JWFm
JTlmLSVlNSViOSViOCVlNSVhZCU5OCVlOCU4MCU4NSVlNSU4MSU4ZiVlNSViNyVhZSVlNCViOCU4
ZSVlNSVhOCU4MSVlOCU4MyU4MSVlNiU4MyU4NSVlNiU4YSVhNSVlNyU5YSU4NCVlNiU5NCViYiVl
OSU5OCViMi8pPC9wPjxwPi0gMS4xNiBbZFNwbG9pdCBBUEsgRG93bmxvYWQg4oCTIEhhY2tpbmcg
JmFtcDsgU2VjdXJpdHkgVG9vbGtpdCBGb3IgQW5kcm9pZF0oaHR0cHM6Ly93d3cuZGFya25ldC5v
cmcudWsvMjAyMC8wMS9kc3Bsb2l0LWFway1kb3dubG9hZC1oYWNraW5nLXNlY3VyaXR5LXRvb2xr
aXQtZm9yLWFuZHJvaWQvP3V0bV9zb3VyY2U9ZmVlZGx5JmFtcDt1dG1fbWVkaXVtPXdlYmZlZWRz
KTwvcD48cD4tIDEuMTYgW+WPkemAgeaUu+WHu+aAp+efreS/oeeahEZha2V0b2tlbuacqOmprF0o
aHR0cHM6Ly93d3cua2FzcGVyc2t5LmNvbS5jbi9ibG9nL2Zha2V0b2tlbi10cm9qYW4tc2VuZHMt
b2ZmZW5zaXZlLXNtcy8xMDYyMy8pPC9wPjxwPi0gMS4xNyBb5p6B6aqMMjAxOeS6pOS6kuWuieWF
qOihjOS4mueglOeptuaKpeWRil0oaHR0cHM6Ly93d3cuZnJlZWJ1Zi5jb20vYXJ0aWNsZXMvcGFw
ZXIvMjI1NjIxLmh0bWwpPC9wPjxwPi0gMS4xNiBb5LiN55SoQUnmkJ7ku5nkurrot7PnmoTpu5Hk
uqfmsqHmnInmoqbmg7NdKGh0dHA6Ly93d3cuaWppYW5kYW8uY29tLzJiL2JhaWppYS8zNDU5OTAu
aHRtbCk8L3A+">
</div>
</div>
drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-12088969851388675452019-12-31T02:24:00.000-08:002021-04-19T20:11:37.053-07:00安全周事记(20191231)- 12.26 [由HTTPS抓包引发的一系列思考](https://www.freebuf.com/articles/web/222564.html)<br />
- 12.25 [Gafgyt家族物联网僵尸网络家族分析](https://www.freebuf.com/articles/others-articles/222677.html)<br />
- 12.24 [2019年移动应用安全十件影响力事件](https://www.anquanke.com/post/id/195635)<br />
- 12.24 [全新 Mozi P2P 僵尸网络入侵 Netgear、D-Link、Huawei 路由器](http://hackernews.cc/archives/29000)<br />
- 12.25 [Twitter Android app 漏洞被用于匹配 1700 万用户手机号码](https://www.solidot.org/story?sid=63050)<br />
- 12.26 [隐私政策保护中第三方sdk问题](https://blog.trustlook.com/yin-si-zheng-ce-bao-hu-zhong-di-san-fang-sdkwen-ti/)<br />
- 12.25 [ATT&CK 之防御逃逸](https://paper.seebug.org/1103/)<br />
- 12.26 [2019年勒索软件:针对市政部门的全面攻击](https://www.freebuf.com/articles/network/223202.html)<br />
- 12.26 [揭露电信诈骗之悄无声息的转走银行卡资金](https://www.anquanke.com/post/id/195840)<br />
- 12.30 [关于印发《App违法违规收集使用个人信息行为认定方法》的通知](https://www.anquanke.com/post/id/196074)<br />
- 12.31 [非法支付之恶:涉案540多亿的非法网络支付连环案告破](https://www.anquanke.com/post/id/196164)<br />
- 12.31 [警惕伪装成“Synaptics触摸板驱动程序”的新型蠕虫病毒](https://www.freebuf.com/articles/terminal/222991.html)<br />
- 12.30 [穷源溯流:KONNI APT组织伪装韩国Android聊天应用的攻击活动剖析](https://www.freebuf.com/articles/terminal/223567.html)<br />
- 12.30 [伸向中亚地区的触手——DustSquad APT组织针对乌兹别克斯坦的活动分析](https://www.anquanke.com/post/id/196067)<br />
- 12.29 [404 Keylogger最新木马,盗取受害者浏览器网站帐号和密码](https://www.freebuf.com/articles/system/222808.html)drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-57607995590616717752019-05-07T20:21:00.011-07:002021-04-19T20:24:20.704-07:00安全周事记(20190507)<pre class='markdown'/>
- 4.23 [Adware Plagues Google Play Store | Avast](https://blog.avast.com/adware-plagues-google-play)
- 4.24 [恶意SDK无感刷百度广告,数千款APP植入影响千万用户](https://www.freebuf.com/articles/terminal/201714.html)
- 4.24 [“天鼠”系列盗号木马分析报告](https://www.anquanke.com/post/id/177066)
- 4.24 [真假文件夹?FakeFolder病毒再次捣乱企业内网](https://www.secpulse.com/archives/104540.html)
- 4.25 [赛门铁克2019年互联网安全威胁报告:数据篇](https://www.freebuf.com/news/201265.html)
- 4.25 [新型赌博黑产攻击肆虐网吧:LOL博彩引流&棋牌盗号](https://www.freebuf.com/articles/system/201459.html)
- 4.25 [从源码层面看一款精致的病毒软件应具备哪些特质](https://www.freebuf.com/articles/system/200923.html)
- 4.25 [正则表达式所引发的DoS攻击(Redos)](https://www.anquanke.com/post/id/177100)
- 4.25 [卡巴斯基:除华硕外至少还有6家公司受到“影锤”行动攻击](http://hackernews.cc/archives/25333)
- 4.25 [外国骗子装成中国黑客造假0day骗钱删号走人](https://www.anquanke.com/post/id/177212)
- 4.26 [威胁情报在态势感知系统中的一种落地尝试](https://www.freebuf.com/articles/security-management/200882.html)
- 4.26 [海莲花APT组织2019年第一季度针对中国的攻击活动技术揭秘](https://www.freebuf.com/articles/network/201940.html)
- 4.27 [IoT-Home-Guard:一款可检测物联网设备中恶意行为的工具](https://www.freebuf.com/articles/terminal/198163.html)
- 4.28 [号称“十分在意用户隐私”的恶意软件罗宾汉是个啥?](https://www.freebuf.com/news/201080.html)
- 4.28 [APT34泄密武器分析报告](https://www.freebuf.com/articles/database/202303.html)
- 4.28 [因广告欺诈及滥用权限,百度子公司数十款应用被Google Play封杀](https://www.freebuf.com/news/202248.html)
- 4.29 [2019年Q1 Android Native病毒疫情报告](https://www.anquanke.com/post/id/177478)
- 4.30 [浅析某针对乌克兰国防和经济部门的大规模钓鱼事件](https://www.freebuf.com/articles/network/201788.html)
- 4.30 [AWS安全笔记|扯淡与权限](https://www.secpulse.com/archives/105062.html)
- 4.30 [The inception bar:一种新型网络钓鱼手段](https://www.anquanke.com/post/id/177488)
- 4.30 [DDoS攻击新趋势:海量移动设备成为新一代肉鸡](https://www.secpulse.com/archives/105045.html)
- 4.30 [防代码泄漏的监控系统架构与实践](https://www.freebuf.com/articles/es/201845.html)
- 5.2 [新型蠕虫病毒攻击服务器,政企电脑变矿机](https://www.freebuf.com/articles/database/201525.html)
- 5.3 [DDoS反射放大攻击全球探测分析](https://www.freebuf.com/articles/database/201804.html)
- 5.5 [聊聊安全测试中如何快速搞定Webshell](https://www.freebuf.com/articles/web/201421.html)
- 5.5 [ISPsystem漏洞分析](https://www.anquanke.com/post/id/177599)
- 5.5 [基于排序的SQL猜解问题](https://www.anquanke.com/post/id/177572)
- 5.5 [“盗梦空间栏”,Chrome 移动版上的新型网络钓鱼](http://hackernews.cc/archives/25369)drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-6907693914027178792019-04-23T20:18:00.017-07:002021-04-19T20:21:42.189-07:00安全周事记(20190423)<pre class='markdown'/>
- 4.16 [黑客 Gnosticplayers 兜售第五批数据:总涉44家企业近10亿用户记录](http://hackernews.cc/archives/25259)
- 4.16 [登录注册攻与防](https://www.secpulse.com/archives/104091.html)
- 4.17 [浅析基于人格特征的内部高风险用户识别方法](https://www.freebuf.com/articles/network/200564.html)
- 4.18 [CNCERT发布《2018年我国互联网网络安全态势报告》](https://www.freebuf.com/articles/network/201280.html)
- 4.18 [一些知名中國 app 因涉嫌大規模廣告詐騙而被 Google 下架](https://chinese.engadget.com/2019/04/18/google-pulls-android-apps-ad-fraud/)
- 4.19 [门罗币挖矿&远控木马样本分析](https://www.freebuf.com/articles/system/200875.html)
- 4.19 [新型Anatova恶意软件分析](https://www.freebuf.com/articles/database/199895.html)
- 4.19 [国家安全机关公布境外网络攻击窃密案件](https://www.anquanke.com/post/id/176944)
- 4.22 [Bilibili 源代码泄漏](https://www.solidot.org/story?sid=60351)
- 4.22 [APT34攻击全本分析](http://www.ijiandao.com/2b/baijia/245780.html)
- 4.19 [黑客在 Telegram 上出售伊朗间谍部队 APT34 的黑客工具源代码](http://hackernews.cc/archives/25286)
- 4.19 [黑客泄露APT 34组织工具、成员信息,扬言更多秘密将持续曝光](https://www.freebuf.com/news/201501.html)
- 4.22 [DNS劫持欺骗病毒“自杀”](https://www.freebuf.com/articles/system/201032.html)
- 4.23 [Targeted Attacks hit multiple embassies with Trojanized TeamViewer](https://securityaffairs.co/wordpress/84367/hacking/trojanized-teamviewer-hit-embassies.html)
- 4.23 [起底童星培训骗局:千亿级的“黑金”产业链,到底有多赚?](http://www.ijiandao.com/2b/baijia/246470.html)drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-66217565447534723642019-04-15T20:34:00.003-07:002021-04-19T20:16:47.605-07:00安全周事记(20190415)- 4.8 [GandCrab5.2勒索病毒伪装国家机关发送钓鱼邮件进行攻击](https://www.freebuf.com/articles/system/200070.html)<br />
- 4.9 [苹果企业证书再爆丑闻 间谍软件窃取用户隐私信息](http://hackernews.cc/archives/25210)<br />
- 4.10 [“银行提款机”变种病毒分析报告](https://www.freebuf.com/articles/paper/200284.html)<br />
- 4.10 [火眼推出 Windows 免费渗透测试套件,包含140多款工具](https://www.freebuf.com/sectool/200524.html)<br />
- 4.10 [流行开发工具 bootstrap-sass 被修改植入后门](https://www.solidot.org/story?sid=60184)<br />
- 4.15 [FuzzScanner:信息搜集开源小工具](https://www.freebuf.com/sectool/200344.html)<br />
- 4.15 [使用HTML注入进行信息泄露](https://www.anquanke.com/post/id/176565)<br />
- 4.15 [数据分析与可视化:谁是安全圈的吃鸡第一人](https://www.freebuf.com/articles/web/199925.html)drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-4391787402849586362019-04-08T05:07:00.001-07:002021-04-19T20:17:13.282-07:00安全周事记(20190408)- 4.2 [学习手册:窥探Web前端黑客技术](http://blog.nsfocus.net/spying-web-front-end-hacking-techniques/)<br />
- 4.2 [“铝”巨人遭勒索病毒攻击,工业互联时代如何保障网络安全](http://blog.nsfocus.net/how-to-guarantee-network-security-in-the-age-of-industrial-interconnecti/)<br />
- 4.3 [KBuster:以伪造韩国银行APP的韩国黑产活动披露](https://www.freebuf.com/articles/terminal/199175.html)<br />
- 4.3 [伊拉克电信公司遭到MuddyWater组织定向攻击](https://www.freebuf.com/articles/network/199008.html)<br />
- 4.3 [换瓶不换酒,盗号木马还在钻搜索引擎广告的空子](https://www.anquanke.com/post/id/175954)<br />
- 4.4 [Xiaomi Vulnerability: When Security Is Not What it Seems](http://blog.checkpoint.com/2019/04/04/xiaomi-vulnerability-when-security-is-not-what-it-seems/)<br />
- 4.5 [友讯路由器 DNS 流量遭黑客劫持](https://www.solidot.org/story?sid=60138)<br />
- 4.5 [Chashell:基于DNS的反向Shell](https://www.freebuf.com/sectool/199406.html)<br />
- 4.5 [2018全球网络安全图鉴](https://www.freebuf.com/articles/network/199133.html)<br />
- 4.6 [如何使用SQLMap脚本绕过Web应用防火墙](https://www.freebuf.com/sectool/198403.html)<br />
- 4.6 [“商贸信”病毒装成商品图片,双击就被安装商业间谍软件](https://www.freebuf.com/articles/network/199906.html)<br />
- 4.7 [奇思妙想之用JS给图片加口令](https://www.freebuf.com/articles/web/199559.html)<br />
- 4.7 [4月7日每日安全热点 - 湖北一公职人员泄露公民信息5万余条](https://www.anquanke.com/post/id/176043)<br />
- 4.8 [CISO的闪电战——2年甲方安全的自我修炼](https://www.anquanke.com/post/id/176075)<br />
- 4.8 [谁劫持了我的DNS:全球域名解析路径劫持测量与分析](https://www.inforsec.org/wp/?p=3161)drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-29821864728984981902019-03-27T01:13:00.001-07:002021-04-19T20:17:16.789-07:00安全周事记(20190327)<br />
<div class="markdown-here-wrapper" data-md-url="https://www.blogger.com/blogger.g?blogID=1654671993539634666#editor/src=sidebar">
<ul style="margin: 1.2em 0px; padding-left: 2em;">
<li style="margin: 0.5em 0px;">3.18 <a href="https://www.freebuf.com/articles/web/197823.html">浅谈RASP技术攻防之基础篇</a></li>
<li style="margin: 0.5em 0px;">3.18 <a href="http://www.ijiandao.com/2b/baijia/237024.html">物联网安全体系思考与探讨</a></li>
<li style="margin: 0.5em 0px;">3.18 <a href="http://www.ijiandao.com/2b/baijia/236811.html">Python 爬取蔡徐坤的 10 万转发数据,竟是假流量?</a></li>
<li style="margin: 0.5em 0px;">3.19 <a href="http://www.ijiandao.com/2b/baijia/237790.html">抖音刷赞骗局</a></li>
<li style="margin: 0.5em 0px;">3.19 <a href="https://www.solidot.org/story?sid=59953">Mirai 出现了新的变种</a></li>
<li style="margin: 0.5em 0px;">3.20 <a href="https://www.freebuf.com/articles/network/198688.html">Buhtrap新动向:针对俄罗斯、白俄罗斯金融机构的攻击活动</a></li>
<li style="margin: 0.5em 0px;">3.20 <a href="https://www.freebuf.com/sectool/198174.html">IoT-Implant-Toolkit:一款针对IoT设备的木马测试工具</a></li>
<li style="margin: 0.5em 0px;">3.20 <a href="https://www.freebuf.com/articles/system/197678.html">AFL漏洞挖掘技术漫谈(二):Fuzz结果分析和代码覆盖率</a></li>
<li style="margin: 0.5em 0px;">3.20 <a href="https://www.freebuf.com/articles/network/197714.html">个人蜜罐Cowrie的运营分析</a></li>
<li style="margin: 0.5em 0px;">3.20 <a href="https://www.sec-un.org/%e6%80%81%e5%8a%bf%e6%84%9f%e7%9f%a5%e4%bb%8e%e5%85%a5%e5%9d%91%e5%88%b0%e9%87%8d%e7%94%9f/">态势感知从入坑到重生</a></li>
<li style="margin: 0.5em 0px;">3.21 <a href="https://www.freebuf.com/articles/es/197825.html">小师妹聊安全标准</a></li>
<li style="margin: 0.5em 0px;">3.21 <a href="https://www.secpulse.com/archives/101931.html">Android-APP 安全(六)之android取证</a></li>
<li style="margin: 0.5em 0px;">3.21 <a href="https://www.sec-un.org/%e5%9f%ba%e4%ba%8e%e4%b8%bb%e5%8a%a8%e9%98%b2%e5%be%a1%e8%83%bd%e5%8a%9b%ef%bc%8c%e5%ae%89%e5%85%a8%e6%88%90%e7%86%9f%e5%ba%a6%e6%a8%a1%e5%9e%8b%e7%9a%84%e4%b8%80%e7%82%b9%e7%82%b9%e6%80%9d%e8%80%83/">基于主动防御能力,安全成熟度模型的一点点思考</a></li>
<li style="margin: 0.5em 0px;">3.22 <a href="https://www.freebuf.com/articles/system/198651.html">Sality感染蠕虫复活来袭,传播“剪切板幽灵”病毒窃取比特币</a></li>
<li style="margin: 0.5em 0px;">3.23 <a href="https://www.freebuf.com/articles/system/198869.html">传奇私服暗藏杀机,亡灵病毒肆虐江湖</a></li>
<li style="margin: 0.5em 0px;">3.23 <a href="https://www.freebuf.com/articles/paper/198032.html">VRVNAC软件携带恶意程序,公安等行业可能受影响</a></li>
<li style="margin: 0.5em 0px;">3.25 <a href="https://www.freebuf.com/vuls/198327.html">那些年挖过的SRC之我是捡漏王</a></li>
<li style="margin: 0.5em 0px;">3.25 <a href="https://www.freebuf.com/news/198966.html">黑产大数据:短视频及直播行业的暗流涌动</a></li>
<li style="margin: 0.5em 0px;">3.25 <a href="https://www.anquanke.com/post/id/174026">KBuster:以伪造韩国银行APP的韩国黑产活动披露</a></li>
<li style="margin: 0.5em 0px;">3.26 <a href="https://www.anquanke.com/post/id/175302">APT组织的聚类和攻击者活动关联</a></li>
<li style="margin: 0.5em 0px;">3.27 <a href="https://motherboard.vice.com/en_us/article/pan9wn/hackers-hijacked-asus-software-updates-to-install-backdoors-on-thousands-of-computers">Hackers Hijacked ASUS Software Updates to Install Backdoors on Thousands of Computers</a></li>
</ul>
<div style="font-size: 0em; height: 0; margin: 0; max-height: 0; max-width: 0; overflow: hidden; padding: 0; width: 0;" title="MDH:PHA+LSAzLjE4IFvmtYXosIhSQVNQ5oqA5pyv5pS76Ziy5LmL5Z+656GA56+HXShodHRwczovL3d3
dy5mcmVlYnVmLmNvbS9hcnRpY2xlcy93ZWIvMTk3ODIzLmh0bWwpPC9wPjxwPi0gMy4xOCBb54mp
6IGU572R5a6J5YWo5L2T57O75oCd6ICD5LiO5o6i6K6oXShodHRwOi8vd3d3LmlqaWFuZGFvLmNv
bS8yYi9iYWlqaWEvMjM3MDI0Lmh0bWwpPC9wPjxwPi0gMy4xOCBbUHl0aG9uIOeIrOWPluiUoeW+
kOWdpOeahCAxMCDkuIfovazlj5HmlbDmja7vvIznq5/mmK/lgYfmtYHph4/vvJ9dKGh0dHA6Ly93
d3cuaWppYW5kYW8uY29tLzJiL2JhaWppYS8yMzY4MTEuaHRtbCk8L3A+PHA+LSAzLjE5IFvmipbp
n7PliLfotZ7pqpflsYBdKGh0dHA6Ly93d3cuaWppYW5kYW8uY29tLzJiL2JhaWppYS8yMzc3OTAu
aHRtbCk8L3A+PHA+LSAzLjE5IFtNaXJhaSDlh7rnjrDkuobmlrDnmoTlj5jnp41dKGh0dHBzOi8v
d3d3LnNvbGlkb3Qub3JnL3N0b3J5P3NpZD01OTk1Myk8L3A+PHA+LSAzLjIwIFtCdWh0cmFw5paw
5Yqo5ZCR77ya6ZKI5a+55L+E572X5pav44CB55m95L+E572X5pav6YeR6J6N5py65p6E55qE5pS7
5Ye75rS75YqoXShodHRwczovL3d3dy5mcmVlYnVmLmNvbS9hcnRpY2xlcy9uZXR3b3JrLzE5ODY4
OC5odG1sKTwvcD48cD4tIDMuMjAgW0lvVC1JbXBsYW50LVRvb2xraXTvvJrkuIDmrL7pkojlr7lJ
b1Torr7lpIfnmoTmnKjpqazmtYvor5Xlt6XlhbddKGh0dHBzOi8vd3d3LmZyZWVidWYuY29tL3Nl
Y3Rvb2wvMTk4MTc0Lmh0bWwpPC9wPjxwPi0gMy4yMCBbQUZM5ryP5rSe5oyW5o6Y5oqA5pyv5ryr
6LCI77yI5LqM77yJ77yaRnV6eue7k+aenOWIhuaekOWSjOS7o+eggeimhueblueOh10oaHR0cHM6
Ly93d3cuZnJlZWJ1Zi5jb20vYXJ0aWNsZXMvc3lzdGVtLzE5NzY3OC5odG1sKTwvcD48cD4tIDMu
MjAgW+S4quS6uuicnOe9kENvd3JpZeeahOi/kOiQpeWIhuaekF0oaHR0cHM6Ly93d3cuZnJlZWJ1
Zi5jb20vYXJ0aWNsZXMvbmV0d29yay8xOTc3MTQuaHRtbCk8L3A+PHA+LSAzLjIwIFvmgIHlir/m
hJ/nn6Xku47lhaXlnZHliLDph43nlJ9dKGh0dHBzOi8vd3d3LnNlYy11bi5vcmcvJWU2JTgwJTgx
JWU1JThhJWJmJWU2JTg0JTlmJWU3JTlmJWE1JWU0JWJiJThlJWU1JTg1JWE1JWU1JTlkJTkxJWU1
JTg4JWIwJWU5JTg3JThkJWU3JTk0JTlmLyk8L3A+PHA+LSAzLjIxIFvlsI/luIjlprnogYrlronl
hajmoIflh4ZdKGh0dHBzOi8vd3d3LmZyZWVidWYuY29tL2FydGljbGVzL2VzLzE5NzgyNS5odG1s
KTwvcD48cD4tIDMuMjEgW0FuZHJvaWQtQVBQIOWuieWFqO+8iOWFre+8ieS5i2FuZHJvaWTlj5bo
r4FdKGh0dHBzOi8vd3d3LnNlY3B1bHNlLmNvbS9hcmNoaXZlcy8xMDE5MzEuaHRtbCk8L3A+PHA+
LSAzLjIxIFvln7rkuo7kuLvliqjpmLLlvqHog73lipvvvIzlronlhajmiJDnhp/luqbmqKHlnovn
moTkuIDngrnngrnmgJ3ogINdKGh0dHBzOi8vd3d3LnNlYy11bi5vcmcvJWU1JTlmJWJhJWU0JWJh
JThlJWU0JWI4JWJiJWU1JThhJWE4JWU5JTk4JWIyJWU1JWJlJWExJWU4JTgzJWJkJWU1JThhJTli
JWVmJWJjJThjJWU1JWFlJTg5JWU1JTg1JWE4JWU2JTg4JTkwJWU3JTg2JTlmJWU1JWJhJWE2JWU2
JWE4JWExJWU1JTllJThiJWU3JTlhJTg0JWU0JWI4JTgwJWU3JTgyJWI5JWU3JTgyJWI5JWU2JTgw
JTlkJWU4JTgwJTgzLyk8L3A+PHA+LSAzLjIyIFtTYWxpdHnmhJ/mn5PooJXomavlpI3mtLvmnaXo
oq3vvIzkvKDmkq3igJzliarliIfmnb/lub3ngbXigJ3nl4Xmr5LnqoPlj5bmr5TnibnluIFdKGh0
dHBzOi8vd3d3LmZyZWVidWYuY29tL2FydGljbGVzL3N5c3RlbS8xOTg2NTEuaHRtbCk8L3A+PHA+
LSAzLjIzIFvkvKDlpYfnp4HmnI3mmpfol4/mnYDmnLrvvIzkuqHngbXnl4Xmr5LogobomZDmsZ/m
uZZdKGh0dHBzOi8vd3d3LmZyZWVidWYuY29tL2FydGljbGVzL3N5c3RlbS8xOTg4NjkuaHRtbCk8
L3A+PHA+LSAzLjIzIFtWUlZOQUPova/ku7bmkLrluKbmgbbmhI/nqIvluo/vvIzlhazlronnrYno
oYzkuJrlj6/og73lj5flvbHlk41dKGh0dHBzOi8vd3d3LmZyZWVidWYuY29tL2FydGljbGVzL3Bh
cGVyLzE5ODAzMi5odG1sKTwvcD48cD4tIDMuMjUgW+mCo+S6m+W5tOaMlui/h+eahFNSQ+S5i+aI
keaYr+aNoea8j+eOi10oaHR0cHM6Ly93d3cuZnJlZWJ1Zi5jb20vdnVscy8xOTgzMjcuaHRtbCk8
L3A+PHA+LSAzLjI1IFvpu5HkuqflpKfmlbDmja7vvJrnn63op4bpopHlj4rnm7Tmkq3ooYzkuJrn
moTmmpfmtYHmtozliqhdKGh0dHBzOi8vd3d3LmZyZWVidWYuY29tL25ld3MvMTk4OTY2Lmh0bWwp
PC9wPjxwPi0gMy4yNSBbS0J1c3Rlcu+8muS7peS8qumAoOmfqeWbvemTtuihjEFQUOeahOmfqeWb
vem7keS6p+a0u+WKqOaKq+mcsl0oaHR0cHM6Ly93d3cuYW5xdWFua2UuY29tL3Bvc3QvaWQvMTc0
MDI2KTwvcD48cD4tIDMuMjYgW0FQVOe7hOe7h+eahOiBmuexu+WSjOaUu+WHu+iAhea0u+WKqOWF
s+iBlF0oaHR0cHM6Ly93d3cuYW5xdWFua2UuY29tL3Bvc3QvaWQvMTc1MzAyKTwvcD48cD4tIDMu
MjcgW0hhY2tlcnMgSGlqYWNrZWQgQVNVUyBTb2Z0d2FyZSBVcGRhdGVzIHRvIEluc3RhbGwgQmFj
a2Rvb3JzIG9uIFRob3VzYW5kcyBvZiBDb21wdXRlcnNdKGh0dHBzOi8vbW90aGVyYm9hcmQudmlj
ZS5jb20vZW5fdXMvYXJ0aWNsZS9wYW45d24vaGFja2Vycy1oaWphY2tlZC1hc3VzLXNvZnR3YXJl
LXVwZGF0ZXMtdG8taW5zdGFsbC1iYWNrZG9vcnMtb24tdGhvdXNhbmRzLW9mLWNvbXB1dGVycyk8
L3A+">
</div>
</div>
drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-23948399191245138072019-03-20T23:26:00.000-07:002021-04-19T20:17:19.443-07:00安全周事记(20190320)<br />
<div class="markdown-here-wrapper" data-md-url="https://www.blogger.com/blogger.g?blogID=1654671993539634666#editor/target=post;postID=2394839919124513807">
<ul style="margin: 1.2em 0px; padding-left: 2em;">
<li style="margin: 0.5em 0px;">3.11 <a href="https://www.anquanke.com/post/id/172996">活动 | 威胁猎人开源风控系统“星云”,促业务反欺诈基础设施普及</a></li>
<li style="margin: 0.5em 0px;">3.12 <a href="https://www.freebuf.com/sectool/197922.html">Ghidra:这个来自NSA的软件逆向工程工具终于来啦!</a></li>
<li style="margin: 0.5em 0px;">3.12 <a href="https://www.freebuf.com/articles/network/197574.html">软件供应链安全威胁:从“奥创纪元”到“无限战争”</a></li>
<li style="margin: 0.5em 0px;">3.12 <a href="https://www.freebuf.com/articles/neopoints/197271.html">威胁在外,压力在内 | CISO职场生存现状</a></li>
<li style="margin: 0.5em 0px;">3.14 <a href="http://hackernews.cc/archives/25054">CheckPoint:Android 恶意广告软件 SimBad 被下载近 1.5 亿次</a></li>
<li style="margin: 0.5em 0px;">3.15 <a href="https://www.freebuf.com/articles/network/197124.html">窃听Telegram Bot的恶意软件</a></li>
<li style="margin: 0.5em 0px;">3.15 <a href="https://research.checkpoint.com/simbad-a-rogue-adware-campaign-on-google-play/">SimBad: A Rogue Adware Campaign On Google Play - Check Point Research</a></li>
<li style="margin: 0.5em 0px;">3.15 <a href="https://www.freebuf.com/news/198385.html">3·15曝光台 | Wi-Fi 探针——潜伏在你身边的“信息窃贼”</a></li>
<li style="margin: 0.5em 0px;">3.15 <a href="https://www.freebuf.com/sectool/197709.html">Fibratus:一款功能强大的Windows内核漏洞利用和跟踪工具</a></li>
<li style="margin: 0.5em 0px;">3.16 <a href="https://www.freebuf.com/vuls/197632.html">基于Web页面验证码机制漏洞的检测</a></li>
<li style="margin: 0.5em 0px;">3.17 <a href="https://www.freebuf.com/articles/paper/197523.html">BankThief:针对波兰和捷克的新型银行钓鱼攻击</a></li>
<li style="margin: 0.5em 0px;">3.18 <a href="https://www.freebuf.com/vuls/198213.html">EOS假充值(hard_fail 状态攻击)红色预警细节披露与修复方案</a></li>
<li style="margin: 0.5em 0px;">3.18 <a href="https://www.freebuf.com/news/197653.html">瑞星首家发现Hybrid Analysis网站数据被“驱动人生木马”污染</a></li>
<li style="margin: 0.5em 0px;">3.19 <a href="https://www.freebuf.com/articles/system/197136.html">Kthrotlds挖矿病毒详细分析报告</a></li>
<li style="margin: 0.5em 0px;">3.19 <a href="https://www.freebuf.com/articles/es/197268.html">从零开始聊一聊态势感知</a></li>
</ul>
<div style="font-size: 0em; height: 0; margin: 0; max-height: 0; max-width: 0; overflow: hidden; padding: 0; width: 0;" title="MDH:PHA+LSAzLjExIFvmtLvliqggfCDlqIHog4HnjI7kurrlvIDmupDpo47mjqfns7vnu5/igJzmmJ/k
upHigJ3vvIzkv4PkuJrliqHlj43mrLror4jln7rnoYDorr7mlr3mma7lj4pdKGh0dHBzOi8vd3d3
LmFucXVhbmtlLmNvbS9wb3N0L2lkLzE3Mjk5Nik8L3A+PHA+LSAzLjEyIFtHaGlkcmHvvJrov5nk
uKrmnaXoh6pOU0HnmoTova/ku7bpgIblkJHlt6XnqIvlt6Xlhbfnu4jkuo7mnaXllabvvIFdKGh0
dHBzOi8vd3d3LmZyZWVidWYuY29tL3NlY3Rvb2wvMTk3OTIyLmh0bWwpPC9wPjxwPi0gMy4xMiBb
6L2v5Lu25L6b5bqU6ZO+5a6J5YWo5aiB6IOB77ya5LuO4oCc5aWl5Yib57qq5YWD4oCd5Yiw4oCc
5peg6ZmQ5oiY5LqJ4oCdXShodHRwczovL3d3dy5mcmVlYnVmLmNvbS9hcnRpY2xlcy9uZXR3b3Jr
LzE5NzU3NC5odG1sKTwvcD48cD4tIDMuMTIgW+WogeiDgeWcqOWklu+8jOWOi+WKm+WcqOWGhSB8
IENJU0/ogYzlnLrnlJ/lrZjnjrDnirZdKGh0dHBzOi8vd3d3LmZyZWVidWYuY29tL2FydGljbGVz
L25lb3BvaW50cy8xOTcyNzEuaHRtbCk8L3A+PHA+LSAzLjE0IFtDaGVja1BvaW5077yaQW5kcm9p
ZCDmgbbmhI/lub/lkYrova/ku7YgU2ltQmFkIOiiq+S4i+i9vei/kSAxLjUg5Lq/5qyhXShodHRw
Oi8vaGFja2VybmV3cy5jYy9hcmNoaXZlcy8yNTA1NCk8L3A+PHA+LSAzLjE1IFvnqoPlkKxUZWxl
Z3JhbSBCb3TnmoTmgbbmhI/ova/ku7ZdKGh0dHBzOi8vd3d3LmZyZWVidWYuY29tL2FydGljbGVz
L25ldHdvcmsvMTk3MTI0Lmh0bWwpPC9wPjxwPi0gMy4xNSBbU2ltQmFkOiBBIFJvZ3VlIEFkd2Fy
ZSBDYW1wYWlnbiBPbiBHb29nbGUgUGxheSAtIENoZWNrIFBvaW50IFJlc2VhcmNoXShodHRwczov
L3Jlc2VhcmNoLmNoZWNrcG9pbnQuY29tL3NpbWJhZC1hLXJvZ3VlLWFkd2FyZS1jYW1wYWlnbi1v
bi1nb29nbGUtcGxheS8pPC9wPjxwPi0gMy4xNSBbM8K3MTXmm53lhYnlj7AgfCBXaS1GaSDmjqLp
kojigJTigJTmvZzkvI/lnKjkvaDouqvovrnnmoTigJzkv6Hmga/nqoPotLzigJ1dKGh0dHBzOi8v
d3d3LmZyZWVidWYuY29tL25ld3MvMTk4Mzg1Lmh0bWwpPC9wPjxwPi0gMy4xNSBbRmlicmF0dXPv
vJrkuIDmrL7lip/og73lvLrlpKfnmoRXaW5kb3dz5YaF5qC45ryP5rSe5Yip55So5ZKM6Lef6Liq
5bel5YW3XShodHRwczovL3d3dy5mcmVlYnVmLmNvbS9zZWN0b29sLzE5NzcwOS5odG1sKTwvcD48
cD4tIDMuMTYgW+WfuuS6jldlYumhtemdoumqjOivgeeggeacuuWItua8j+a0nueahOajgOa1i10o
aHR0cHM6Ly93d3cuZnJlZWJ1Zi5jb20vdnVscy8xOTc2MzIuaHRtbCk8L3A+PHA+LSAzLjE3IFtC
YW5rVGhpZWbvvJrpkojlr7nms6LlhbDlkozmjbflhYvnmoTmlrDlnovpk7booYzpkpPpsbzmlLvl
h7tdKGh0dHBzOi8vd3d3LmZyZWVidWYuY29tL2FydGljbGVzL3BhcGVyLzE5NzUyMy5odG1sKTwv
cD48cD4tIDMuMTggW0VPU+WBh+WFheWAvO+8iGhhcmRfZmFpbCDnirbmgIHmlLvlh7vvvInnuqLo
ibLpooTorabnu4boioLmiqvpnLLkuI7kv67lpI3mlrnmoYhdKGh0dHBzOi8vd3d3LmZyZWVidWYu
Y29tL3Z1bHMvMTk4MjEzLmh0bWwpPC9wPjxwPi0gMy4xOCBb55Ge5pif6aaW5a625Y+R546wSHli
cmlkIEFuYWx5c2lz572R56uZ5pWw5o2u6KKr4oCc6amx5Yqo5Lq655Sf5pyo6ams4oCd5rGh5p+T
XShodHRwczovL3d3dy5mcmVlYnVmLmNvbS9uZXdzLzE5NzY1My5odG1sKTwvcD48cD4tIDMuMTkg
W0t0aHJvdGxkc+aMluefv+eXheavkuivpue7huWIhuaekOaKpeWRil0oaHR0cHM6Ly93d3cuZnJl
ZWJ1Zi5jb20vYXJ0aWNsZXMvc3lzdGVtLzE5NzEzNi5odG1sKTwvcD48cD4tIDMuMTkgW+S7jumb
tuW8gOWni+iBiuS4gOiBiuaAgeWKv+aEn+efpV0oaHR0cHM6Ly93d3cuZnJlZWJ1Zi5jb20vYXJ0
aWNsZXMvZXMvMTk3MjY4Lmh0bWwpPC9wPg==">
</div>
</div>
drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0tag:blogger.com,1999:blog-1654671993539634666.post-15421842095204678792019-03-14T23:25:00.000-07:002021-04-19T20:17:21.495-07:00安全周事记(20190314)<br />
<div class="markdown-here-wrapper" data-md-url="https://www.blogger.com/blogger.g?blogID=1654671993539634666#editor/src=sidebar">
<ul style="margin: 1.2em 0px; padding-left: 2em;">
<li style="margin: 0.5em 0px;">3.4 <a href="https://www.freebuf.com/vuls/197202.html">威胁预警 | ProtonMiner挖矿蠕虫扩大攻击面加速传播</a></li>
<li style="margin: 0.5em 0px;">3.4 <a href="https://www.anquanke.com/post/id/172111">kthrotlds挖矿病毒分析报告</a></li>
<li style="margin: 0.5em 0px;">3.4 <a href="https://www.anquanke.com/post/id/171891">渗透之权限维持杂谈</a></li>
<li style="margin: 0.5em 0px;">3.5 <a href="https://bartblaze.blogspot.com/2019/03/analysing-massive-office-365-phishing.html">Analyzing A Massive Office 365 Phishing Campaign</a></li>
<li style="margin: 0.5em 0px;">3.4 <a href="https://www.zdnet.com/article/comcast-buys-bluvector-an-ai-cybersecurity-firm/">Comcast buys BluVector, an AI cybersecurity firm</a></li>
<li style="margin: 0.5em 0px;">3.5 <a href="https://www.freebuf.com/articles/terminal/196604.html">冒用有效签名:Clop勒索病毒这股”韩流“已入侵国内企业</a></li>
<li style="margin: 0.5em 0px;">3.7 <a href="https://www.freebuf.com/articles/web/195044.html">简析认证加授权如何使API更安全</a></li>
<li style="margin: 0.5em 0px;">3.6 <a href="https://www.freebuf.com/articles/system/196834.html">警惕!WinRAR漏洞利用升级:社工、加密、无文件后门</a></li>
<li style="margin: 0.5em 0px;">3.7 <a href="http://hackernews.cc/archives/25013">“俄罗斯套娃”恶意软件通过海盗湾盗版下载传播</a></li>
<li style="margin: 0.5em 0px;">3.11 <a href="https://www.freebuf.com/geek/196409.html">键盘拦截器制作与测试</a></li>
<li style="margin: 0.5em 0px;">3.11 <a href="https://www.freebuf.com/articles/es/197394.html">2019年唠嗑企业安全之堡垒机(二)</a></li>
<li style="margin: 0.5em 0px;">3.10 <a href="https://www.freebuf.com/articles/system/196895.html">“匿影”挖矿病毒:借助公共网盘和图床隐匿自身</a></li>
<li style="margin: 0.5em 0px;">3.10 <a href="https://www.freebuf.com/articles/ics-articles/196647.html">2018年工业控制网络安全态势白皮书</a></li>
<li style="margin: 0.5em 0px;">3.8 <a href="https://www.freebuf.com/sectool/196778.html">CANalyzat0r :一款可以对专用汽车协议进行安全分析的强大工具</a></li>
<li style="margin: 0.5em 0px;">3.7 <a href="https://www.freebuf.com/news/197155.html">Android移动APP 安全形势分析</a></li>
<li style="margin: 0.5em 0px;">3.7 <a href="https://www.secpulse.com/archives/100184.html">Android-APP 安全(五)之android取证-文件系统与数据结构</a></li>
<li style="margin: 0.5em 0px;">3.12 <a href="http://hackernews.cc/archives/25040">微软 Word 中的新漏洞允许攻击者绕过所有防恶意软件防御</a></li>
<li style="margin: 0.5em 0px;">3.12 <a href="https://www.sec-un.org/%e5%ae%89%e5%85%a8%e4%b8%8e%e4%bf%a1%e4%bb%bb%e7%9a%84%e5%8d%8a%e6%af%9b%e9%92%b1%e5%85%b3%e7%b3%bb/">安全与信任的半毛钱关系</a></li>
<li style="margin: 0.5em 0px;">3.11 <a href="https://www.secpulse.com/archives/100660.html">为了追查盗照片的人,我在网上叫了个小姐。</a></li>
<li style="margin: 0.5em 0px;">3.9 <a href="http://www.ijiandao.com/2b/baijia/231512.html">让数百万台手机训练同一个模型?Google把这套框架开源了</a></li>
</ul>
<div style="font-size: 0em; height: 0; margin: 0; max-height: 0; max-width: 0; overflow: hidden; padding: 0; width: 0;" title="MDH:PHA+LSAzLjQgW+WogeiDgemihOitpiB8IFByb3Rvbk1pbmVy5oyW55+/6KCV6Jmr5omp5aSn5pS7
5Ye76Z2i5Yqg6YCf5Lyg5pKtXShodHRwczovL3d3dy5mcmVlYnVmLmNvbS92dWxzLzE5NzIwMi5o
dG1sKTwvcD48cD4tIDMuNCBba3Rocm90bGRz5oyW55+/55eF5q+S5YiG5p6Q5oql5ZGKXShodHRw
czovL3d3dy5hbnF1YW5rZS5jb20vcG9zdC9pZC8xNzIxMTEpPC9wPjxwPi0gMy40IFvmuJfpgI/k
uYvmnYPpmZDnu7TmjIHmnYLosIhdKGh0dHBzOi8vd3d3LmFucXVhbmtlLmNvbS9wb3N0L2lkLzE3
MTg5MSk8L3A+PHA+LSAzLjUgW0FuYWx5emluZyBBIE1hc3NpdmUgT2ZmaWNlIDM2NSBQaGlzaGlu
ZyBDYW1wYWlnbl0oaHR0cHM6Ly9iYXJ0YmxhemUuYmxvZ3Nwb3QuY29tLzIwMTkvMDMvYW5hbHlz
aW5nLW1hc3NpdmUtb2ZmaWNlLTM2NS1waGlzaGluZy5odG1sKTwvcD48cD4tIDMuNCBbQ29tY2Fz
dCBidXlzIEJsdVZlY3RvciwgYW4gQUkgY3liZXJzZWN1cml0eSBmaXJtXShodHRwczovL3d3dy56
ZG5ldC5jb20vYXJ0aWNsZS9jb21jYXN0LWJ1eXMtYmx1dmVjdG9yLWFuLWFpLWN5YmVyc2VjdXJp
dHktZmlybS8pPC9wPjxwPi0gMy41IFvlhpLnlKjmnInmlYjnrb7lkI3vvJpDbG9w5YuS57Si55eF
5q+S6L+Z6IKh4oCd6Z+p5rWB4oCc5bey5YWl5L615Zu95YaF5LyB5LiaXShodHRwczovL3d3dy5m
cmVlYnVmLmNvbS9hcnRpY2xlcy90ZXJtaW5hbC8xOTY2MDQuaHRtbCk8L3A+PHA+LSAzLjcgW+eu
gOaekOiupOivgeWKoOaOiOadg+WmguS9leS9v0FQSeabtOWuieWFqF0oaHR0cHM6Ly93d3cuZnJl
ZWJ1Zi5jb20vYXJ0aWNsZXMvd2ViLzE5NTA0NC5odG1sKTwvcD48cD4tIDMuNiBb6K2m5oOV77yB
V2luUkFS5ryP5rSe5Yip55So5Y2H57qn77ya56S+5bel44CB5Yqg5a+G44CB5peg5paH5Lu25ZCO
6ZeoXShodHRwczovL3d3dy5mcmVlYnVmLmNvbS9hcnRpY2xlcy9zeXN0ZW0vMTk2ODM0Lmh0bWwp
PC9wPjxwPi0gMy43IFvigJzkv4TnvZfmlq/lpZflqIPigJ3mgbbmhI/ova/ku7bpgJrov4fmtbfn
m5fmub7nm5fniYjkuIvovb3kvKDmkq1dKGh0dHA6Ly9oYWNrZXJuZXdzLmNjL2FyY2hpdmVzLzI1
MDEzKTwvcD48cD4tIDMuMTEgW+mUruebmOaLpuaIquWZqOWItuS9nOS4jua1i+ivlV0oaHR0cHM6
Ly93d3cuZnJlZWJ1Zi5jb20vZ2Vlay8xOTY0MDkuaHRtbCk8L3A+PHA+LSAzLjExIFsyMDE55bm0
5ZSg5ZeR5LyB5Lia5a6J5YWo5LmL5aCh5Z6S5py677yI5LqM77yJXShodHRwczovL3d3dy5mcmVl
YnVmLmNvbS9hcnRpY2xlcy9lcy8xOTczOTQuaHRtbCk8L3A+PHA+LSAzLjEwIFvigJzljL/lvbHi
gJ3mjJbnn7/nl4Xmr5LvvJrlgJ/liqnlhazlhbHnvZHnm5jlkozlm77luorpmpDljL/oh6rouqtd
KGh0dHBzOi8vd3d3LmZyZWVidWYuY29tL2FydGljbGVzL3N5c3RlbS8xOTY4OTUuaHRtbCk8L3A+
PHA+LSAzLjEwIFsyMDE45bm05bel5Lia5o6n5Yi2572R57uc5a6J5YWo5oCB5Yq/55m955qu5Lmm
XShodHRwczovL3d3dy5mcmVlYnVmLmNvbS9hcnRpY2xlcy9pY3MtYXJ0aWNsZXMvMTk2NjQ3Lmh0
bWwpPC9wPjxwPi0gMy44IFtDQU5hbHl6YXQwciDvvJrkuIDmrL7lj6/ku6Xlr7nkuJPnlKjmsb3o
vabljY/orq7ov5vooYzlronlhajliIbmnpDnmoTlvLrlpKflt6XlhbddKGh0dHBzOi8vd3d3LmZy
ZWVidWYuY29tL3NlY3Rvb2wvMTk2Nzc4Lmh0bWwpPC9wPjxwPi0gMy43IFtBbmRyb2lk56e75Yqo
QVBQIOWuieWFqOW9ouWKv+WIhuaekF0oaHR0cHM6Ly93d3cuZnJlZWJ1Zi5jb20vbmV3cy8xOTcx
NTUuaHRtbCk8L3A+PHA+LSAzLjcgW0FuZHJvaWQtQVBQIOWuieWFqO+8iOS6lO+8ieS5i2FuZHJv
aWTlj5bor4Et5paH5Lu257O757uf5LiO5pWw5o2u57uT5p6EXShodHRwczovL3d3dy5zZWNwdWxz
ZS5jb20vYXJjaGl2ZXMvMTAwMTg0Lmh0bWwpPC9wPjxwPi0gMy4xMiBb5b6u6L2vIFdvcmQg5Lit
55qE5paw5ryP5rSe5YWB6K645pS75Ye76ICF57uV6L+H5omA5pyJ6Ziy5oG25oSP6L2v5Lu26Ziy
5b6hXShodHRwOi8vaGFja2VybmV3cy5jYy9hcmNoaXZlcy8yNTA0MCk8L3A+PHA+LSAzLjEyIFvl
ronlhajkuI7kv6Hku7vnmoTljYrmr5vpkrHlhbPns7tdKGh0dHBzOi8vd3d3LnNlYy11bi5vcmcv
JWU1JWFlJTg5JWU1JTg1JWE4JWU0JWI4JThlJWU0JWJmJWExJWU0JWJiJWJiJWU3JTlhJTg0JWU1
JThkJThhJWU2JWFmJTliJWU5JTkyJWIxJWU1JTg1JWIzJWU3JWIzJWJiLyk8L3A+PHA+LSAzLjEx
IFvkuLrkuobov73mn6Xnm5fnhafniYfnmoTkurrvvIzmiJHlnKjnvZHkuIrlj6vkuobkuKrlsI/l
p5DjgIJdKGh0dHBzOi8vd3d3LnNlY3B1bHNlLmNvbS9hcmNoaXZlcy8xMDA2NjAuaHRtbCk8L3A+
PHA+LSAzLjkgW+iuqeaVsOeZvuS4h+WPsOaJi+acuuiuree7g+WQjOS4gOS4quaooeWei++8n0dv
b2dsZeaKiui/meWll+ahhuaetuW8gOa6kOS6hl0oaHR0cDovL3d3dy5pamlhbmRhby5jb20vMmIv
YmFpamlhLzIzMTUxMi5odG1sKTwvcD4=">
</div>
</div>
drovliuhttp://www.blogger.com/profile/11719500578108716716noreply@blogger.com0